Signing a Windows EXE file
Solution 1
You can try using Microsoft's Sign Tool
You download it as part of the Windows SDK for Windows Server 2008 and .NET 3.5. Once downloaded you can use it from the command line like so:
signtool sign /a MyFile.exe
This signs a single executable, using the "best certificate" available. (If you have no certificate, it will show a SignTool error message.)
Or you can try:
signtool signwizard
This will launch a wizard that will walk you through signing your application. (This option is not available after Windows SDK 7.0.)
If you'd like to get a hold of certificate that you can use to test your process of signing the executable you can use the .NET tool Makecert.
Certificate Creation Tool (Makecert.exe)
Once you've created your own certificate and have used it to sign your executable, you'll need to manually add it as a Trusted Root CA for your machine in order for UAC to tell the user running it that it's from a trusted source. Important. Installing a certificate as ROOT CA will endanger your users privacy. Look what happened with DELL. You can find more information for accomplishing this both in code and through Windows in:
Stack Overflow question Install certificates in to the Windows Local user certificate store in C#
Installing a Self-Signed Certificate as a Trusted Root CA in Windows Vista
Hopefully that provides some more information for anyone attempting to do this!
Solution 2
I had the same scenario in my job and here are our findings
The first thing you have to do is get the certificate and install it on your computer, you can either buy one from a Certificate Authority or generate one using makecert.
Here are the pros and cons of the 2 options
Buy a certificate
-
Pros
- Using a certificate issued by a CA(Certificate Authority) will ensure that Windows will not warn the end user about an application from an "unknown publisher" on any Computer using the certificate from the CA (OS normally comes with the root certificates from manny CA's)
-
Cons:
-
There is a cost involved on getting a certificate from a CA
For prices, see https://cheapsslsecurity.com/sslproducts/codesigningcertificate.html and https://www.digicert.com/code-signing/
-
Generate a certificate using Makecert
-
Pros:
- The steps are easy and you can share the certificate with the end users
-
Cons:
- End users will have to manually install the certificate on their machines and depending on your clients that might not be an option
- Certificates generated with makecert are normally used for development and testing, not production
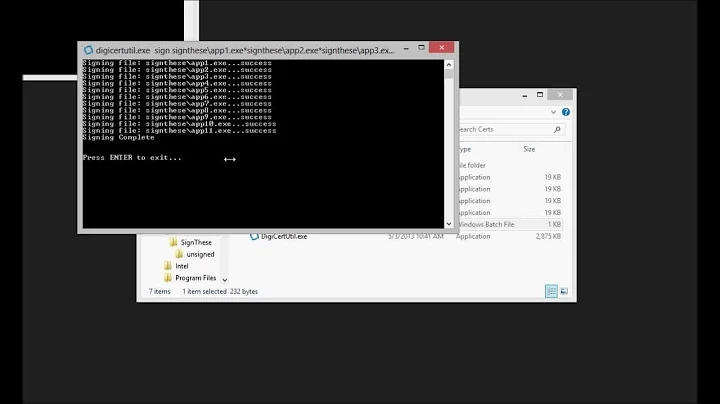
Sign the executable file
There are two ways of signing the file you want:
-
Using a certificate installed on the computer
signtool.exe sign /a /s MY /sha1 sha1_thumbprint_value /t http://timestamp.verisign.com/scripts/timstamp.dll /v "C:\filename.dll"- In this example we are using a certificate stored on the Personal folder with a SHA1 thumbprint (This thumbprint comes from the certificate) to sign the file located at
C:\filename.dll
- In this example we are using a certificate stored on the Personal folder with a SHA1 thumbprint (This thumbprint comes from the certificate) to sign the file located at
-
Using a certificate file
signtool sign /tr http://timestamp.digicert.com /td sha256 /fd sha256 /f "c:\path\to\mycert.pfx" /p pfxpassword "c:\path\to\file.exe"- In this example we are using the certificate
c:\path\to\mycert.pfxwith the passwordpfxpasswordto sign the filec:\path\to\file.exe
- In this example we are using the certificate
Test Your Signature
-
Method 1: Using signtool
Go to: Start > Run
TypeCMD> click OK
At the command prompt, enter the directory wheresigntoolexists
Run the following:signtool.exe verify /pa /v "C:\filename.dll" -
Method 2: Using Windows
Right-click the signed file
Select Properties
Select the Digital Signatures tab. The signature will be displayed in the Signature list section.
I hope this could help you
Sources:
-
https://www.digicert.com/kb/code-signing/signcode-signtool-command-line.htm
-
https://docs.microsoft.com/en-us/windows/win32/seccrypto/makecert
Solution 3
You can get a free cheap code signing certificate from Certum if you're doing open source development.
I've been using their certificate for over a year, and it does get rid of the unknown publisher message from Windows.
As far as signing code I use signtool.exe from a script like this:
signtool.exe sign /t http://timestamp.verisign.com/scripts/timstamp.dll /f "MyCert.pfx" /p MyPassword /d SignedFile.exe SignedFile.exe
Solution 4
Another option, if you need to sign the executable on a Linux box is to use signcode from the Mono project tools. It is supported on Ubuntu.
Solution 5
The ASP's magazine ASPects has a detailed description on how to sign code (You have to be a member to read the article). You can download it through http://www.asp-shareware.org/
Here's link to a description how you can make your own test certificate.
This might also be interesting.
Related videos on Youtube
Lasar
Web dude. Business: liepins.net Private: liepins.de Too many sites: 10110101.net
Updated on April 07, 2022Comments
-
Lasar about 2 years
I have an EXE file that I should like to sign so that Windows will not warn the end user about an application from an "unknown publisher". I am not a Windows developer. The application in question is a screensaver generated from an application that generates screensaver applications. As such I have no influence on how the file is generated.
I've already found out that I will need a code signing certificate from a CA like Verisign or instantssl.com. What I don't understand is what I need to do (if at all possible) to sign my EXE file. What is a simple explanation?
Mel Green's answer took me further, but signtool wants me to specify what certificate to use in any case. Can I get a free code signing certificate somehow to test if this will work for me at all?
Also please specify which certificate kind is the correct one. Most sites only mention "code signing" and talk about signing applications that are actually compiled by the user. This is not the case for me.
-
 Server Overflow over 6 yearsJust curious - how much one has to pay to buy a certificate?
Server Overflow over 6 yearsJust curious - how much one has to pay to buy a certificate? -
 Sharan Arumugam about 5 years@Rigel roughly $400 a year, probably not worth :)
Sharan Arumugam about 5 years@Rigel roughly $400 a year, probably not worth :) -
 Server Overflow about 5 years@SharanArumugam: WHAAT?????? It is like Microsfot is against cheap/free software!
Server Overflow about 5 years@SharanArumugam: WHAAT?????? It is like Microsfot is against cheap/free software! -
 RBT over 2 years
RBT over 2 years -
prosach over 2 yearsDoes this answer your question? How do I create a self-signed certificate for code signing on Windows?
-
-
A. Wilson over 11 yearsAddendum four years later: Comodo was compromised sometime in early 2012 (blogs.comodo.com/it-security/data-security/…) and so lots of user agents now reject certificates with a Comodo root authority
-
Dan W almost 11 yearsIs Comodo still a risky bet in mid 2013, and by 'user agents', does that mean Microsoft/Windows as surely they're the ones who decide whether to show that notorious 'unknown publisher' message.
-
The_Ghost about 10 yearsA working workflow in separate question: stackoverflow.com/questions/84847/…
-
Westy92 almost 10 years"This tool is automatically installed with Visual Studio. To run the tool, use the Developer Command Prompt (or the Visual Studio Command Prompt in Windows 7)." msdn.microsoft.com/en-us/library/8s9b9yaz(v=vs.110).aspx
-
 hultqvist almost 9 yearsIt doesn't look free anymore, still much cheaper, € 14
hultqvist almost 9 yearsIt doesn't look free anymore, still much cheaper, € 14 -
Lee Richardson over 8 yearsYou're right it doesn't look free any more. fwiw I just renewed, and I didn't pay anything. Maybe I'm grandfathered in. Maybe their internal processes are broken. Their website sure is complicated.
-
Gromski over 7 yearsSorry, removed the explicit service recommendations, which are 1) out of date and 2) have been ruled off-topic now (because 1.).
-
 Marian almost 7 yearsThat's very helpful! The package is available in Debian as well, under the name mono-devel.
Marian almost 7 yearsThat's very helpful! The package is available in Debian as well, under the name mono-devel. -
Overdrivr over 5 yearsVery curious about the certificate used by signtool too.
-
 thoni56 over 5 years
thoni56 over 5 yearsosslsigncodeis also available undercygwin, so if you are already using that (as I am), then you can sign in your current environment, rather than needing to switch to WSL. -
 Omar Reis over 5 years"signwizard" option is not available after Windows SDK 7.0
Omar Reis over 5 years"signwizard" option is not available after Windows SDK 7.0 -
ewerybody about 5 yearsThat is €25.00 now? (en.sklep.certum.pl/data-safety/code-signing-certificates/…)
-
Alexander Revo over 4 yearsMakecert has been deprecated and a PowerShell cmdlet New-SelfSignedCertificate should be used to create a testing certificate instead. Details in stackoverflow.com/a/51443366/38117911 (answer to a question linked by The_Ghost).
-
 Legorooj over 4 years@MelGreen your TechNet link doesn't work - you need techcommunity.microsoft.com/t5/windows-server-essentials-and/…
Legorooj over 4 years@MelGreen your TechNet link doesn't work - you need techcommunity.microsoft.com/t5/windows-server-essentials-and/… -
 Poikilos about 4 years@will-croxford The article says that was made "even worse" by distributing the private key, but isn't that the only problem & only affect https? Say you had a program where the private key is in a public repo, as is a common practice. If the program didn't use the certificate for traffic, but only used it for signing the application, wouldn't that be fine? According to docs.microsoft.com/en-us/dotnet/standard/assembly/strong-named, application signing appears to be only for identifying the application uniquely (in GAC). So, you should use a different key for that and be fine, or what?
Poikilos about 4 years@will-croxford The article says that was made "even worse" by distributing the private key, but isn't that the only problem & only affect https? Say you had a program where the private key is in a public repo, as is a common practice. If the program didn't use the certificate for traffic, but only used it for signing the application, wouldn't that be fine? According to docs.microsoft.com/en-us/dotnet/standard/assembly/strong-named, application signing appears to be only for identifying the application uniquely (in GAC). So, you should use a different key for that and be fine, or what? -
Markus Laire almost 4 yearsCertum shop says that their open source certificate WILL NOT remove Microsoft SmartScreen Filter message.
-
 Server Overflow over 3 yearsAlso see: stackoverflow.com/questions/64134677/…
Server Overflow over 3 yearsAlso see: stackoverflow.com/questions/64134677/… -
 Anston Sorensen over 3 yearsWhen I download my program after I uploaded it, it says, "Failed, Virus Detected"
Anston Sorensen over 3 yearsWhen I download my program after I uploaded it, it says, "Failed, Virus Detected" -
Tim Pederick over 2 years@MarkusLaire You can bypass SmartScreen by buying the expensive EV certificate. Otherwise your EXE (and your certificate) need to build "reputation" before SmartScreen will stop flagging it. Getting enough users—and apparently internal users are fine—will do the job, but how many users and for how long seems to be unpredictable.
-
Markus Laire over 2 years@TimPederick My understanding is that a person can't get EV certificate, that those are only available to corporations.
-
Tim Pederick over 2 years@MarkusLaire Mine too. I'm just pointing out that you can get your software past SmartScreen even as a sole and/or open-source developer… you just have to have a userbase (e.g. testers) willing to click through its warnings at first.
-
Bob over 2 yearsWhy OV doesn't help much?
-
 TheLegendaryCopyCoder over 2 yearsIt now costs about the the same as a regular code signing cert at 69 Euros per year.
TheLegendaryCopyCoder over 2 yearsIt now costs about the the same as a regular code signing cert at 69 Euros per year. -
 Server Overflow over 2 years@Bob - Windows still shows some warnings when your app is signed with OV.
Server Overflow over 2 years@Bob - Windows still shows some warnings when your app is signed with OV. -
 Server Overflow about 2 yearsCan I use the "signtool.exe" tool without installing the whole SDK (1GB) crap?
Server Overflow about 2 yearsCan I use the "signtool.exe" tool without installing the whole SDK (1GB) crap? -
mozey almost 2 yearsosslsigncode is a better option for me: "osslsigncode is based on OpenSSL and cURL, and thus should be able to compile on most platforms where these exist"