Simple L2TP/IPsec server not working (openswan, xl2tpd, Ubuntu, Windows)
Solution 1
Well, that was terrible.
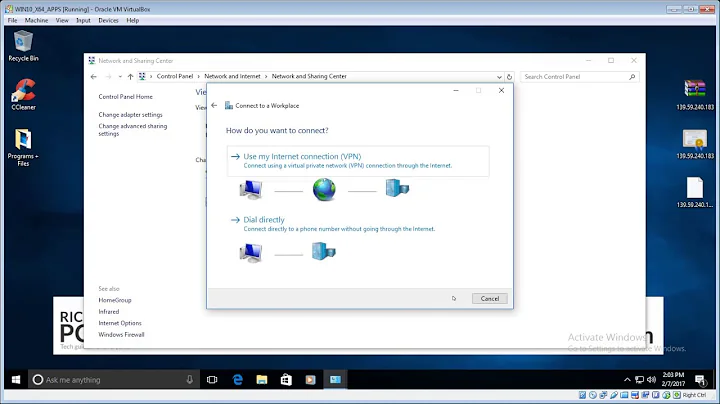
I found the solution in the last place I would've looked: the client. Windows does not support IPsec NAT-T by default, which is used whenever the server is behind a NAT (as in this case). You have to add a registry key to enable this - see http://support.microsoft.com/kb/926179/en-us (still applies to Windows 8). Then everything just works.
How I found it: this post, which I in turn found as the second hit from Googling for openswan ipsec STATE_QUICK_R2: IPsec SA established transport mode ESP/NAT.
Solution 2
I had similar problem.
My server doesn't NAT, so this piece is not needed so removed it:
conn L2TP-PSK-NAT
rightsubnet=vhost:%priv
also=L2TP-PSK-noNAT
And when that's done NAT Traversel must be set to yes.
nat_traversal=yes
Solution 3
In ipsec.conf, left needs to be not your public IP, but whatever IP your server sees, so 10.252.194.250 in this case. That way it can "match" up a left/right side connection. Where left=you, and right=%any.
Related videos on Youtube
madankundu
Updated on September 18, 2022Comments
-
madankundu over 1 year
I configured openswan and xl2tpd on an Ubuntu 12.04 server (on EC2) by following various tutorials/documentation which seem to largely say the same things, but most recently this one.
However, my attempts to connect from Windows (which I configured with the shared secret and username/password) fail. Logs suggest that an IPsec tunnel is established, but nothing happens.
Here are packet dumps and log activity (nothing occurs in syslog, so no iptables log msgs):
$ sudo tcpdump -n host 64.236.139.254 and not port 22 21:00:49.843198 IP 64.236.139.254.26712 > 10.252.60.213.500: isakmp: phase 1 I ident 21:00:49.844815 IP 10.252.60.213.500 > 64.236.139.254.26712: isakmp: phase 1 R ident 21:00:49.928882 IP 64.236.139.254.26712 > 10.252.60.213.500: isakmp: phase 1 I ident 21:00:49.930819 IP 10.252.60.213.500 > 64.236.139.254.26712: isakmp: phase 1 R ident 21:00:49.972728 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 1 I ident[E] 21:00:49.973924 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 1 R ident[E] 21:00:50.000353 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:50.001429 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:00:50.030932 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:50.037256 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:50.055200 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:00:50.415676 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:50.415731 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:00:50.416605 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:00:53.055631 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:53.060694 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:00:53.088162 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:53.088180 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:00:53.088437 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:00:57.069750 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:57.070741 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:00:57.101194 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:00:57.101390 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:00:57.101817 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:01:05.087873 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:01:05.089292 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:01:05.117423 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:01:05.117815 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:01:05.118026 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:01:09.122471 IP 10.252.60.213.4500 > 64.236.139.254.26724: isakmp-nat-keep-alive 21:01:09.122664 IP 10.252.60.213.4500 > 64.236.139.254.26724: isakmp-nat-keep-alive 21:01:09.301582 IP 64.236.139.254.26724 > 10.252.60.213.4500: isakmp-nat-keep-alive 21:01:15.180248 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:01:15.181699 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 21:01:15.288574 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 21:01:15.288612 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:01:15.289452 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:01:25.229928 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:01:25.230090 IP 64.236.139.254.26724 > 10.252.60.213.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 21:01:25.233650 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] 21:01:25.251769 IP 10.252.60.213.4500 > 64.236.139.254.26724: NONESP-encap: isakmp: phase 2/others R inf[E] $ tail -fn0 /var/log/syslog Feb 6 21:00:30 ip-10-252-60-213 kernel: [11977313.441315] device eth0 entered promiscuous mode $ tail -fn0 /var/log/auth.log Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring unknown Vendor ID payload [01528bbbc00696121849ab9a1c5b2a5100000001] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring Vendor ID payload [MS NT5 ISAKMPOAKLEY 00000009] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: received Vendor ID payload [RFC 3947] method set to=109 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: received Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02_n] meth=106, but already using method 109 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring Vendor ID payload [FRAGMENTATION] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring Vendor ID payload [MS-Negotiation Discovery Capable] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring Vendor ID payload [Vid-Initial-Contact] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26712: ignoring Vendor ID payload [IKE CGA version 1] Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: responding to Main Mode from unknown peer 64.236.139.254 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: OAKLEY_GROUP 20 not supported. Attribute OAKLEY_GROUP_DESCRIPTION Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: OAKLEY_GROUP 19 not supported. Attribute OAKLEY_GROUP_DESCRIPTION Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: transition from state STATE_MAIN_R0 to state STATE_MAIN_R1 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: STATE_MAIN_R1: sent MR1, expecting MI2 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: NAT-Traversal: Result using RFC 3947 (NAT-Traversal): both are NATed Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: transition from state STATE_MAIN_R1 to state STATE_MAIN_R2 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: STATE_MAIN_R2: sent MR2, expecting MI3 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: Main mode peer ID is ID_IPV4_ADDR: '10.0.2.15' Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[15] 64.236.139.254 #50: switched from "L2TP-PSK-NAT" to "L2TP-PSK-NAT" Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: deleting connection "L2TP-PSK-NAT" instance with peer 64.236.139.254 {isakmp=#0/ipsec=#0} Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: transition from state STATE_MAIN_R2 to state STATE_MAIN_R3 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: new NAT mapping for #50, was 64.236.139.254:26712, now 64.236.139.254:26724 Feb 6 21:00:49 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: STATE_MAIN_R3: sent MR3, ISAKMP SA established {auth=OAKLEY_PRESHARED_KEY cipher=aes_256 prf=oakley_sha group=modp2048} Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/0 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: responding to Quick Mode proposal {msgid:01000000} Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #51: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0xed4ff6b8 <0x9232de04 xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/1701 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: responding to Quick Mode proposal {msgid:02000000} Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: keeping refhim=4294901761 during rekey Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #52: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0xb245cb36 <0x76292945 xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0xed4ff6b8) payload: deleting IPSEC State #51 Feb 6 21:00:50 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/1701 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: responding to Quick Mode proposal {msgid:03000000} Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: keeping refhim=4294901761 during rekey Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #53: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0xb6953c9c <0x3331cb4f xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0xb245cb36) payload: deleting IPSEC State #52 Feb 6 21:00:53 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/1701 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: responding to Quick Mode proposal {msgid:04000000} Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: keeping refhim=4294901761 during rekey Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #54: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0x2ca92f36 <0x86256756 xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0xb6953c9c) payload: deleting IPSEC State #53 Feb 6 21:00:57 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/1701 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: responding to Quick Mode proposal {msgid:05000000} Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: keeping refhim=4294901761 during rekey Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #55: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0x8df1a782 <0x61eed691 xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0x2ca92f36) payload: deleting IPSEC State #54 Feb 6 21:01:05 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: the peer proposed: 54.245.182.129/32:17/1701 -> 10.0.2.15/32:17/1701 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: NAT-Traversal: received 2 NAT-OA. using first, ignoring others Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: responding to Quick Mode proposal {msgid:06000000} Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: us: 10.252.60.213<10.252.60.213>[+S=C]:17/1701 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: them: 64.236.139.254[10.0.2.15,+S=C]:17/1701===10.0.2.15/32 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: keeping refhim=4294901761 during rekey Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #56: STATE_QUICK_R2: IPsec SA established transport mode {ESP/NAT=>0x021d5dde <0xc9c31f90 xfrm=AES_128-HMAC_SHA1 NATOA=10.0.2.15 NATD=64.236.139.254:26724 DPD=none} Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0x8df1a782) payload: deleting IPSEC State #55 Feb 6 21:01:15 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA(0x021d5dde) payload: deleting IPSEC State #56 Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: ERROR: netlink XFRM_MSG_DELPOLICY response for flow eroute_connection delete included errno 2: No such file or directory Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received and ignored informational message Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254 #50: received Delete SA payload: deleting ISAKMP State #50 Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: "L2TP-PSK-NAT"[16] 64.236.139.254: deleting connection "L2TP-PSK-NAT" instance with peer 64.236.139.254 {isakmp=#0/ipsec=#0} Feb 6 21:01:25 ip-10-252-60-213 pluto[1464]: packet from 64.236.139.254:26724: received and ignored informational messageNothing seems to happen after that, and Windows gives up.
Here are the packets I see on the client side - I see the exact same packets, so nothing's getting filtered out:
$ sudo tcpdump -i wlan3 -n host $ip and not port 22 12:59:16.170388 IP 10.66.230.208.53383 > 54.245.182.129.500: isakmp: phase 1 I ident 12:59:16.197972 IP 54.245.182.129.500 > 10.66.230.208.53383: isakmp: phase 1 R ident 12:59:16.255396 IP 10.66.230.208.53383 > 54.245.182.129.500: isakmp: phase 1 I ident 12:59:16.282917 IP 54.245.182.129.500 > 10.66.230.208.53383: isakmp: phase 1 R ident 12:59:16.299043 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 1 I ident[E] 12:59:16.326840 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 1 R ident[E] 12:59:16.328144 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:16.357804 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 12:59:16.358888 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:16.362385 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:16.741818 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 12:59:16.743117 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:16.743396 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 12:59:16.769431 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R inf[E] 12:59:19.383010 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:19.414362 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 12:59:19.415559 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] ... 12:59:31.441952 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R oakley-quick[E] 12:59:31.443878 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:31.444124 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 12:59:31.476359 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R inf[E] 12:59:35.499825 IP 54.245.182.129.4500 > 10.66.230.208.53200: isakmp-nat-keep-alive 12:59:35.500068 IP 54.245.182.129.4500 > 10.66.230.208.53200: isakmp-nat-keep-alive 12:59:35.629175 IP 10.66.230.208.53200 > 54.245.182.129.4500: isakmp-nat-keep-alive 12:59:41.429705 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:41.534606 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R oakley-quick[E].537423 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I oakley-quick[E] 12:59:41.537675 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 12:59:41.642367 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R inf[E] 12:59:51.482628 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 12:59:51.482836 IP 10.66.230.208.53200 > 54.245.182.129.4500: NONESP-encap: isakmp: phase 2/others I inf[E] 12:59:51.587334 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R inf[E] 12:59:51.604347 IP 54.245.182.129.4500 > 10.66.230.208.53200: NONESP-encap: isakmp: phase 2/others R inf[E]Here is the state of affairs:
+ sudo ipsec verify Checking your system to see if IPsec got installed and started correctly: Version check and ipsec on-path [OK] Linux Openswan U2.6.37/K3.2.0-37-virtual (netkey) Checking for IPsec support in kernel [OK] SAref kernel support [N/A] NETKEY: Testing XFRM related proc values [OK] [OK] [OK] Checking that pluto is running [OK] Pluto listening for IKE on udp 500 [OK] Pluto listening for NAT-T on udp 4500 [OK] Checking for 'ip' command [OK] Checking /bin/sh is not /bin/dash [WARNING] Checking for 'iptables' command [OK] Opportunistic Encryption Support [DISABLED] + ifconfig eth0 Link encap:Ethernet HWaddr 22:00:0a:fc:3c:d5 inet addr:10.252.60.213 Bcast:10.252.60.255 Mask:255.255.255.192 inet6 addr: fe80::2000:aff:fefc:3cd5/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:4803 errors:0 dropped:0 overruns:0 frame:0 TX packets:3147 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:376849 (376.8 KB) TX bytes:628809 (628.8 KB) Interrupt:25 eth0:0 Link encap:Ethernet HWaddr 22:00:0a:fc:3c:d5 inet addr:172.22.1.1 Bcast:172.22.1.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 Interrupt:25 lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:0 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:0 (0.0 B) TX bytes:0 (0.0 B) + sudo iptables -t nat -L Chain PREROUTING (policy ACCEPT) target prot opt source destination Chain INPUT (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain POSTROUTING (policy ACCEPT) target prot opt source destination MASQUERADE all -- anywhere anywhere LOG all -- anywhere anywhere LOG level warning prefix "blah blah: " + sudo egrep -v '^[[:space:]]*(#|$)' /etc/ipsec.conf version 2.0 # conforms to second version of ipsec.conf specification config setup dumpdir=/var/run/pluto/ nat_traversal=yes virtual_private=%v4:172.16.0.0/12 oe=off protostack=auto conn L2TP-PSK-NAT rightsubnet=vhost:%priv also=L2TP-PSK-noNAT conn L2TP-PSK-noNAT authby=secret pfs=no auto=add keyingtries=3 rekey=no ikelifetime=8h keylife=1h type=transport left=10.252.60.213 leftprotoport=17/1701 right=%any rightprotoport=17/%any forceencaps=yes + sudo cat /etc/ppp/options.xl2tpd require-mschap-v2 ms-dns 8.8.8.8 ms-dns 8.8.4.4 asyncmap 0 auth crtscts lock hide-password modem debug name l2tpd proxyarp lcp-echo-interval 30 lcp-echo-failure 4 + sudo cat /proc/sys/net/ipv4/ip_forward /proc/sys/net/ipv4/conf/*/{accept,send}_redirects 1 0 0 0 0 0 0 0 ==> /proc/sys/net/ipv4/conf/lo/send_redirects <== 0 + grep -v '^;' /etc/xl2tpd/xl2tpd.conf [global] ipsec saref = no debug avp = yes debug network = yes debug packet = yes debug state = yes debug tunnel = yes [lns default] ip range = 172.22.1.2-172.22.1.99 local ip = 172.22.1.1 refuse chap = yes refuse pap = yes require authentication = yes ppp debug = yes pppoptfile = /etc/ppp/options.xl2tpd length bit = yes + sudo cat /etc/ipsec.secrets include /var/lib/openswan/ipsec.secrets.inc 10.252.60.213 %any: PSK "MYSHAREDSECRET" + sudo cat /etc/ppp/chap-secrets # client server secret IP addresses yang l2tpd MYPASSWORD * -
madankundu over 11 yearsThanks, this seems to have changed something, but connecting still fails. Updating my question.
-
Willie over 11 yearsYour logs now show "STATE_QUICK_R2: IPsec SA established transport mode" so the IPsec part is now working. Probably your iptables blocking L2TP traffic at this point, but I didn't look super closely.
-
madankundu over 11 yearsI pasted my iptables setup, which has almost nothing in it. I also added iptables logging but nothing gets logged.
-
Willie over 11 yearsYou posted your nat table of iptables. Your filter table would be more interesting and relevant probably.
-
madankundu over 11 yearsThe filter table is empty.
-
Bob Banks about 11 yearsI love you, man. After hours of struggling, this was the fix!
-
 sudo over 7 yearsI don't get why there are so many random files you have to edit to make this VPN work. Can't you just
sudo over 7 yearsI don't get why there are so many random files you have to edit to make this VPN work. Can't you justapt-get installa VPN and have it work?
![[P1] VPN L2TP / IPSec- Easy and convenient - Connect a remote computer to the corporate network](https://i.ytimg.com/vi/QmLv-OKyrng/hqdefault.jpg?sqp=-oaymwEcCOADEI4CSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLAoONfdmVCY8zTLtYyhKqI7MNLm_w)
![The L2TP Connection Attempt Failed Because the Security Layer Encountered a Processing Error [FIX]](https://i.ytimg.com/vi/hvrLx3Nci-E/hqdefault.jpg?sqp=-oaymwEcCOADEI4CSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBbdHflKFNOhJRaveCbil710JOdiA)

