Spring Security OAuth2 pure resource server
Solution 1
This is possible as long as the authorization server and resource server(s) access a shared tokenStore (e.g. using JdbcTokenStore with a common dataSource). You can just use DefaultTokenServices with a reference to your shared tokenStore. Below is an example Spring config which you should be able to tweak to fit your needs:
<?xml version="1.0" encoding="UTF-8"?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:security="http://www.springframework.org/schema/security"
xmlns:oauth2="http://www.springframework.org/schema/security/oauth2"
xsi:schemaLocation="
http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans-3.2.xsd
http://www.springframework.org/schema/security
http://www.springframework.org/schema/security/spring-security-3.1.xsd
http://www.springframework.org/schema/security/oauth2
http://www.springframework.org/schema/security/spring-security-oauth2.xsd">
<bean id="tokenStore" class="org.springframework.security.oauth2.provider.token.JdbcTokenStore">
<constructor-arg name="dataSource" ref="dataSource" />
</bean>
<bean id="tokenServices" class="org.springframework.security.oauth2.provider.token.DefaultTokenServices">
<property name="tokenStore" ref="tokenStore" />
</bean>
<bean id="authenticationEntryPoint" class="org.springframework.security.oauth2.provider.error.OAuth2AuthenticationEntryPoint">
<property name="realmName" value="myRealm" />
</bean>
<bean id="oauthAccessDeniedHandler" class="org.springframework.security.oauth2.provider.error.OAuth2AccessDeniedHandler" />
<bean id="accessDecisionManager" class="org.springframework.security.access.vote.UnanimousBased">
<constructor-arg>
<list>
<bean class="org.springframework.security.oauth2.provider.vote.ScopeVoter" />
<bean class="org.springframework.security.access.vote.RoleVoter" />
<bean class="org.springframework.security.access.vote.AuthenticatedVoter" />
</list>
</constructor-arg>
</bean>
<!-- This is not actually used, but it's required by Spring Security -->
<security:authentication-manager alias="authenticationManager" />
<oauth2:expression-handler id="oauthExpressionHandler" />
<oauth2:web-expression-handler id="oauthWebExpressionHandler" />
<security:global-method-security pre-post-annotations="enabled" proxy-target-class="true">
<security:expression-handler ref="oauthExpressionHandler" />
</security:global-method-security>
<oauth2:resource-server id="myResource" resource-id="myResourceId" token-services-ref="tokenServices" />
<security:http pattern="/myPattern/**" create-session="never"
entry-point-ref="authenticationEntryPoint" access-decision-manager-ref="accessDecisionManager">
<security:anonymous enabled="false" />
<security:intercept-url pattern="/**" access="SCOPE_READ" method="GET" />
<security:intercept-url pattern="/**" access="SCOPE_READ" method="HEAD" />
<security:intercept-url pattern="/**" access="SCOPE_READ" method="OPTIONS" />
<security:intercept-url pattern="/**" access="SCOPE_WRITE" method="PUT" />
<security:intercept-url pattern="/**" access="SCOPE_WRITE" method="POST" />
<security:intercept-url pattern="/**" access="SCOPE_WRITE" method="DELETE" />
<security:custom-filter ref="myResource" before="PRE_AUTH_FILTER" />
<security:access-denied-handler ref="oauthAccessDeniedHandler" />
<security:expression-handler ref="oauthWebExpressionHandler" />
</security:http>
</beans>
Solution 2
Yes its possible. Like you have already mentioned in your question, RemoteTokenServices is the solution.
I have created one sample which has separate auth and resource server. Its just a sample to give a quick idea about the concept and open for extension.
Spring-AngularJS-OAuth2-Sample
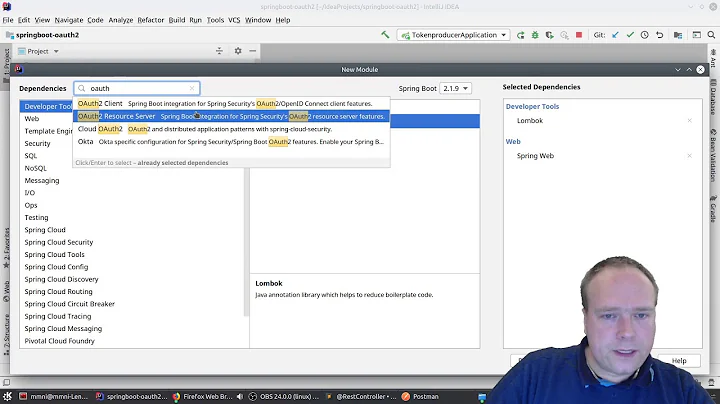
Related videos on Youtube
Explosion Pills
Deep in the heart of the lush forest of Gainesville, Florida -- pride of the sunshine. Software developer / director for Mobiquity, the greatest mobile development company ever conceived.
Updated on July 05, 2022Comments
-
Explosion Pills almost 2 years
We already have an OAuth2 authorization server set up, so I need to create a corresponding resource server (separate server). We plan to use the Spring Security OAuth2 project. Their documentation for setting up a resource server:
https://github.com/spring-projects/spring-security-oauth/wiki/oAuth2#resource-server-configuration
token-services-refshould point to the token-handling bean. However it seems like the token handling is done by the server itself even though it is the resource server. There doesn't seem to be any remote token services class or any configuration relating to a remote server. This is in contrast with the CloudFoundary UAA (https://github.com/cloudfoundry/uaa/blob/master/samples/api/src/main/webapp/WEB-INF/spring-servlet.xml) which has:<bean id="tokenServices" class="org.cloudfoundry.identity.uaa.oauth.RemoteTokenServices"> <property name="checkTokenEndpointUrl" value="${checkTokenEndpointUrl}" />Is there any way to use Spring Security OAuth2 for a resource server that communicates with a separate OAuth2 Authorization server? How can I set the communication endpoint?
-
Steven Francolla almost 10 yearsYessss! Thank you, @chris-h. Plug-n-played this to a quick 40 minute success, followed by a celebratory game of nerf h-o-r-s-e.
-
Ruwanka Madhushan about 7 yearsDon't we have any properties that can be configured to achieve this?
-
 Reginaldo Santos about 6 years@Rites in your example the RemoteTokenServices are using de /oauth/check_token endpoint. what about token validation using /oauth/token_id endpoint? Do you how this can be achieved?
Reginaldo Santos about 6 years@Rites in your example the RemoteTokenServices are using de /oauth/check_token endpoint. what about token validation using /oauth/token_id endpoint? Do you how this can be achieved? -
 Andrei Matei over 5 yearsdo you have an example with RemoteTokenServices for facebook graph?
Andrei Matei over 5 yearsdo you have an example with RemoteTokenServices for facebook graph? -
Joe over 4 years@All any has idea about: stackoverflow.com/questions/57672643/…