SSH Public Key Authentication not working with PuTTY
The SELinux contexts on your /root/.ssh directory are most likely wrong.
Verify the problem with:
ls -alZ /root/.ssh
These files should have the type ssh_home_t.
Fix the problem with:
restorecon -r -v /root/.ssh
Related videos on Youtube
haydenc2
Updated on September 18, 2022Comments
-
haydenc2 almost 2 years
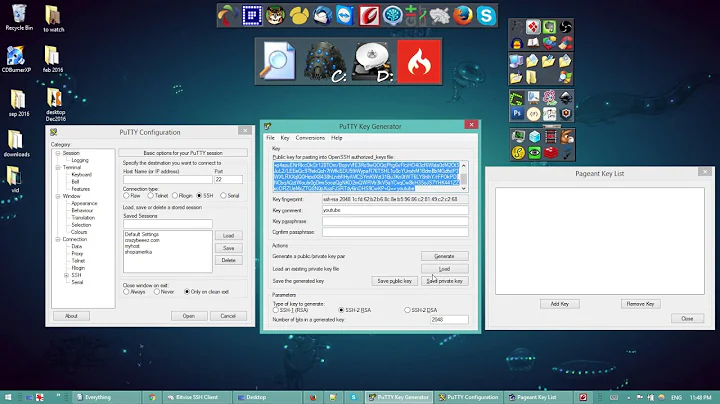
I have created a virtual machine and installed Redhat 6. I am having issues connecting using public key authentication.
I can use PuTTY on my Windows host to connect to the redhat guest, where I am prompted for a password. I am trying to setup public-key authentication for the root user, so I have created a folder
~/.sshwith what I believe to be the correct permissions.[root@redhat ~]# cd ~/.ssh [root@redhat .ssh]# pwd /root/.ssh [root@redhat .ssh]# ls -la total 16 drwx------. 2 root root 4096 Aug 21 16:28 . dr-x------. 3 root root 4096 Aug 20 17:20 .. -rw-r--r--. 1 root root 250 Aug 20 17:20 authorized_keys -rw-r--r--. 1 root root 391 Aug 21 16:28 known_hostsI am running Pageant with my private key loaded, this is working successfully with other hosts, so I don't think that's the problem.
When I attempt to PuTTY to the VM guest, I am getting prompted for a password.
If I check the PuTTY Event Log, I find the following messages.
2012-08-21 17:29:41 Pageant is running. Requesting keys. 2012-08-21 17:29:41 Pageant has 1 SSH-2 keys 2012-08-21 17:29:46 Trying Pageant key #0 2012-08-21 17:29:46 Server refused our keyI have Agent forwarding enabled, and one thing I stumbled across was somebody suggested running another copy of sshd in debug mode, which I tried. (I have snipped out portions of the output to keep this somewhat brief).
[root@redhat ~]# /usr/sbin/sshd -d -p 2222 debug1: sshd version OpenSSH_5.3p1 debug1: read PEM private key done: type RSA debug1: private host key: #0 type 1 RSA debug1: read PEM private key done: type DSA debug1: private host key: #1 type 2 DSA <...> debug1: Bind to port 2222 on 0.0.0.0. Server listening on 0.0.0.0 port 2222. <...>At this point I connect from another session on the vm using the command
ssh localhost -p 2222<...> Connection from ::1 port 36844 debug1: Client protocol version 2.0; client software version OpenSSH_5.3 debug1: match: OpenSSH_5.3 pat OpenSSH* debug1: Enabling compatibility mode for protocol 2.0 debug1: Local version string SSH-2.0-OpenSSH_5.3 <...> debug1: userauth-request for user root service ssh-connection method none debug1: attempt 0 failures 0 debug1: PAM: initializing for "root" debug1: PAM: setting PAM_RHOST to "localhost" debug1: userauth-request for user root service ssh-connection method publickey debug1: attempt 1 failures 0 debug1: test whether pkalg/pkblob are acceptable debug1: PAM: setting PAM_TTY to "ssh" debug1: temporarily_use_uid: 0/0 (e=0/0) debug1: trying public key file /root/.ssh/authorized_keys debug1: fd 4 clearing O_NONBLOCK debug1: matching key found: file /root/.ssh/authorized_keys, line 1 Found matching RSA key: <snip> debug1: restore_uid: 0/0 Postponed publickey for root from ::1 port 36844 ssh2 debug1: userauth-request for user root service ssh-connection method publickey debug1: attempt 2 failures 0 debug1: temporarily_use_uid: 0/0 (e=0/0) debug1: trying public key file /root/.ssh/authorized_keys debug1: fd 4 clearing O_NONBLOCK debug1: matching key found: file /root/.ssh/authorized_keys, line 1 Found matching RSA key: <snip> debug1: restore_uid: 0/0 debug1: ssh_rsa_verify: signature correct debug1: do_pam_account: called Accepted publickey for root from ::1 port 36844 ssh2 debug1: monitor_child_preauth: root has been authenticated by privileged process <...>At this point I have authenticated sucessfully using my public key, and I logout by pressing
Ctrl-D.debug1: Received SIGCHLD. <...> Received disconnect from ::1: 11: disconnected by user <...> [root@redhat ~]#So strangely using the SSH Agent forwarding was enough to successfully authenticate against sshd running in debug mode, but not the 'normal' sshd running on port 22.
Does anyone have any ideas why this would be?
Thanks!