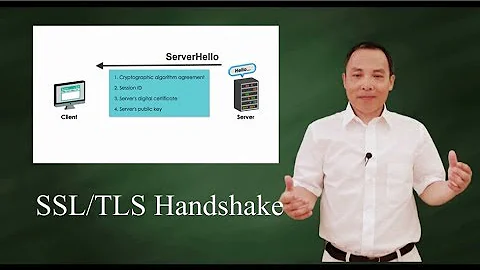
SSL connection issue with s_client
You set which ciphers are accepted in server.xml, e.g.
SSLCipherSuite="ALL:!ADH:!SSLv2:!EXPORT40:!EXP:!LOW"
which excludes SSLv2. There's more information at techstacks
Related videos on Youtube
Crushing
Updated on September 18, 2022Comments
-
Crushing over 1 year
I'm trying to configure SSL on two machines (on LAN) from a local CA I created and am hitting an issue when testing with s_client, I can't seem to locate helpful info w/ my google-fu skills. I'm trying to familiarize myself with info security and seemed like a good place to start. My scenario is
host1: ubuntu 12.04, tomcat7
host2: ubuntu 12.04, tomcat7
configured tomcat w/ ssl on both hosts, and can reach the tomcat homepage @ https://{host}:8443 from either machine. I configured the connector w/ my keystore & pass, I believe tomcat is happy w/ the params as earlier I had tomcat startup errors not being able to extract the private key but that is resolved. here's what I did
// create tomcat server keystore 1. sudo keytool -genkey -alias tomcat7 -keyalg rsa -keystore /etc/tomcat7/keystore/host1.jks 2. openssl genrsa -aes256 -out host1_key.pem 2048 3. openssl req -new -key host1_key.pem -out host1.csr 4. openssl x509 -req -days 3650 -in host1.csr -CA root_ca.cer -CAkey root_ca_key.pem - CAcreateserial -setalias host1 -addtrust serverAuth -addtrust clientAuth -extensions client -outform PEM -out host1.cer // export to keystore 5. openssl pkcs12 -export -in host1.cer -inkey host1_key.pem -out host1.p12 -name "host1" // import keystore 6. sudo keytool -importkeystore -srckeystore host1.p12 -destkeystore /etc/tomcat7/keystore/host1.jks -srcstoretype pkcs12 dest passwd: src passwd: Entry for alias host1 successfully imported Import command completed: 1 entries successfully imported, 0 entries failed or cancelled 7. view keystore host1.jks Enter keystore password: Keystore type: JKS Keystore provider: SUN Your keystore contains 2 entries tomcat7, Feb 18, 2013, PrivateKeyEntry, Certificate fingerprint (MD5): 2A:F1:5A:D1:5B:B1:24:5E:C7:96:3F:71:C8:17:09:E8 host1, Feb 18, 2013, PrivateKeyEntry, Certificate fingerprint (MD5): 3F:81:FD:79:78:85:98:32:72:C4:42:8F:D6:2F:DD:09 8. Configure connector in tomcat w/ this keystore. restart tomcat. Boots w/out error. Browse to https://host1:8443 from host2 and will get to "It Works!" pageThe next step I did was test the connection from one machine to the other
host2: openssl s_client -connect host1:8443 CONNECTED(00000003) 140310470641312:error:14077438:SSL routines:SSL23_GET_SERVER_HELLO:tlsv1 alert internal error:s23_clnt.c:724: --- no peer certificate available --- No client certificate CA names sent --- SSL handshake has read 7 bytes and written 226 bytes --- New, (NONE), Cipher is (NONE) Secure Renegotiation IS NOT supported Compression: NONE Expansion: NONE ---In Wireshark I set my filter for all TLS protocol ("ssl.record.version == 0x0301") and I don't even see a request go out when I run the above command. I think that means openssl can't extract my certificate? I'm not sure where to look from here, if I change my keystore password to something invalid in my tomcat connector, i'll see errors in tomcat when it boots. Otherwise I should have seen the handshaking requests in wireshark.
I'll see the same if I try from my other host.
I've read about 'truststores' when trying to resolve my issue, would that be another keystore w/ the other server's .p12 imported and my local CA?
Thanks, any direction would be helpful.
-
Crushing about 11 yearsIf I force ssl3 via -ssl3 I get a successful connection; I see my server cert and a massive list of acceptable CA names. I guess this means I don't have an issue and must use ssl3.. would this be something I specify in the tomcat connector?
-