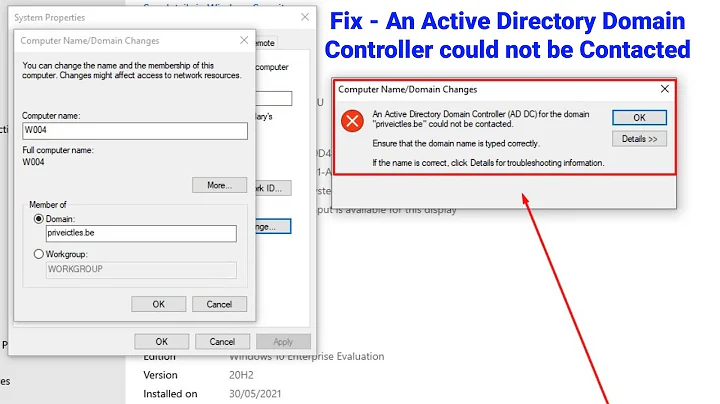
Trouble Joining an Active Directory Domain
The problem seems to have been that my admin had created an entry on the Domain Controller for this server. This apparently caused a conflict that caused Kerberos to encounter the following error when trying to join:
kyle@Server21:~$ sudo net ads join -k
Failed to join domain: failed to lookup DC info for domain 'COMPANYNAME.LOCAL' over rpc: An internal error occurred.
I'm not sure that this error was entirely accurate since my admin said the server was joined to the domain on his end and realmd indicated that I was joined as well:
kyle@Server21:~$ realm join COMPANYNAME.LOCAL
realm: Already joined to this domain
The steps I followed to get a successful Kerberos join were as follows:
- Admin removed the entry in the Domain Controller
- Reran Kerberos configuration using:
sudo dpkg-reconfigure krb5-config - Chose the options in the configuration to add the Domain Controller explicitly to the
[realms]section ofkrb5.conf - Changed the hostname to ensure a new record was created
- Pulled a new ticket using
kinit - Joined the domain using
sudo net ads join -k
Final result:
kyle@SERV21:~$ sudo net ads join -k
Using short domain name -- COMPANYNAME
Joined 'SERV21' to dns domain 'CompanyName.Local'
Related videos on Youtube
embedded.kyle
Adept engineering polymath with 15+ years of experience. Specializing in all areas of Embedded Systems from circuit design and board bring-up to firmware development, OS optimization, and end-user application programming. Proficient in utilizing a wide variety of programs and languages. An enthusiastic teacher and ambitious learner.
Updated on September 18, 2022Comments
-
embedded.kyle over 1 year
I'm trying to join an Ubuntu 16.04 server to a Windows 2003 R2 domain by following the Ubuntu SSSD and Active Directory Guide. My admin says that from the controller side, it is part of the domain. But SSSD can't seem to start and
net ads joinfails.The
krb5.confwas modified by the installer and now has this:kyle@Server21:~$ cat /etc/krb5.conf [libdefaults] default_realm = COMAPNYNAME.LOCALOn a previous install I thought there was something else in
[realms]that was asked for during the install but I can't remember what and it wasn't asked for this time around.My
smb.conf:[global] ## Browsing/Identification ### # Change this to the workgroup/NT-domain name your Samba server will part of workgroup = COMPANYNAME client signing = yes client use spnego = yes kerberos method = secrets and keytab realm = COMPANYNAME.LOCAL security = adsMy
sssd.conf:kyle@Server21:~$ sudo cat /etc/sssd/sssd.conf [sssd] services = nss, pam config_file_version = 2 domains = COMPANYNAME.LOCAL [domain/COMPANYNAME.LOCAL] id_provider = ad access_provider = ad override_homedir = /home/%d/%uThough the SSSD service can't seem to start:
kyle@Server21:~$ systemctl status sssd.service ● sssd.service - System Security Services Daemon Loaded: loaded (/lib/systemd/system/sssd.service; enabled; vendor preset: enabled) Active: failed (Result: exit-code) since Wed 2016-06-22 09:57:57 EDT; 37min ago Process: 16027 ExecStart=/usr/sbin/sssd -D -f (code=exited, status=1/FAILURE) Jun 22 09:57:55 Server21 sssd[16038]: Starting up Jun 22 09:57:55 Server21 sssd[16041]: Starting up Jun 22 09:57:55 Server21 sssd[16042]: Starting up Jun 22 09:57:56 Server21 sssd[be[16043]: Starting up Jun 22 09:57:57 Server21 sssd[be[16043]: Failed to read keytab [default]: No such file or directory Jun 22 09:57:57 Server21 sssd[16031]: Exiting the SSSD. Could not restart critical service [COMPANYNAME.LOCAL]. Jun 22 09:57:57 Server21 systemd[1]: sssd.service: Control process exited, code=exited status=1 Jun 22 09:57:57 Server21 systemd[1]: Failed to start System Security Services Daemon. Jun 22 09:57:57 Server21 systemd[1]: sssd.service: Unit entered failed state. Jun 22 09:57:57 Server21 systemd[1]: sssd.service: Failed with result 'exit-code'.And since the guide says that ownership and permissions are important:
kyle@Server21:~$ sudo ls -la /etc/sssd total 12 drwx--x--x 2 sssd sssd 4096 Jun 21 14:34 . drwxr-xr-x 103 root root 4096 Jun 22 10:21 .. -rw------- 1 root root 172 Jun 21 14:22 sssd.confMy
nsswitch.conf:kyle@Server21:~$ cat /etc/nsswitch.conf # /etc/nsswitch.conf # # Example configuration of GNU Name Service Switch functionality. # If you have the `glibc-doc-reference' and `info' packages installed, try: # `info libc "Name Service Switch"' for information about this file. passwd: compat sss group: compat sss shadow: compat sss gshadow: files hosts: files dns networks: files protocols: db files services: db files sss ethers: db files rpc: db files netgroup: nis sss sudoers: files sssMy
hosts:kyle@Server21:~$ cat /etc/hosts 127.0.0.1 localhost 127.0.1.1 Server21.COMPANYNAME.LOCAL Server21 192.168.11.11 Server21.COMPANYNAME.LOCAL Server21 # The following lines are desirable for IPv6 capable hosts ::1 localhost ip6-localhost ip6-loopback ff02::1 ip6-allnodes ff02::2 ip6-allroutersHere is where the trouble starts. Using
sudoto runkinitresults in the following:kyle@Server21:~$ sudo kinit adminstrator kinit: Client '[email protected]' not found in Kerberos database while getting initial credentialsIt will authenticate if I drop the
sudothough:kyle@Server21:~$ kinit -V administrator Using default cache: /tmp/krb5cc_1000 Using principal: [email protected] Password for [email protected]: Authenticated to Kerberos v5And I can verify the ticket:
kyle@Server21:~$ klist Ticket cache: FILE:/tmp/krb5cc_1000 Default principal: [email protected] Valid starting Expires Service principal 06/23/2016 13:41:55 06/23/2016 23:41:55 krbtgt/[email protected] renew until 06/24/2016 13:41:48But when I try to join the domain:
kyle@Server21:~$ sudo net ads join -k Failed to join domain: failed to lookup DC info for domain 'COMPANYNAME.LOCAL' over rpc: An internal error occurred.I had previously received the
NT_STATUS_UNSUCCESSFULmessage mentioned in the guide but was able to solve that by modifying myhostsfile.The guide talks about verifying that the computer account was created in the Active Directory. And my admin says that he can see the machine just fine so I believe that is okay. The second verification option does not tell me what I'm supposed to get back from that command but I don't receive anything so I suppose it isn't working.
So where am I going wrong here?
Edit:
I'm not sure what I did, but SSSD is now running.
-
embedded.kyle almost 8 years
/etc/krb5.keytabalready exists and has some encrypted stuff interspersed with the server name and domain name. Do I need to create an additional one?