Troubles with sssd and Active Directory Integration
20,171
Try below settings, They work pretty well in my environment.
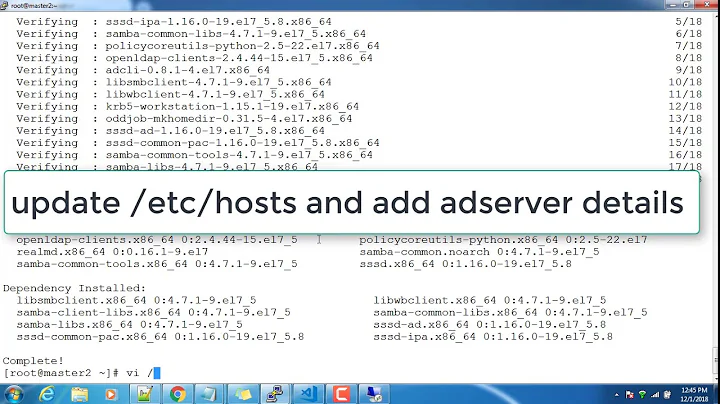
Make changes to /etc/sssd/sssd.conf
[root@localhost ~]# cat /etc/sssd/sssd.conf |grep -v ^# |grep -v ^$
[sssd]
config_file_version = 2
reconnection_retries = 3
sbus_timeout = 30
services = nss, pam
domains = default
[nss]
filter_groups = root
filter_users = root
reconnection_retries = 3
[pam]
reconnection_retries = 3
[domain/default]
ldap_default_authtok_type = password
ldap_id_use_start_tls = False
cache_credentials = True
ldap_group_object_class = group
ldap_search_base = dc=example,dc=com
chpass_provider = krb5
ldap_default_authtok = RedHat1!
id_provider = ldap
auth_provider = krb5
ldap_default_bind_dn = cn=Administrator,cn=Users,dc=example,dc=com
ldap_user_gecos = displayName
debug_level = 0
ldap_uri = ldap://10.65.208.43/
krb5_realm = EXAMPLE.COM
krb5_kpasswd = 10.65.208.43
ldap_schema = rfc2307bis
ldap_force_upper_case_realm = True
ldap_user_object_class = person
ldap_tls_cacertdir = /etc/openldap/cacerts
krb5_server = 10.65.208.43
- Run the authconfig-tui tool. Select ldap under the "User Information" section and Kerberos under the "Authentication" Section.
- On the ldap Settings step. Leave the use TLS option unselected put the AD servers fully qualified domain name in and the base DN.
- On the kerberos Settings page enter the AD servers Realm, also list the AD servers fully qualified domain name for the KDC and Admin Server.
This will result in restarting sssd daemon.
Verify :-
[root@localhost ~]# id user1
Make sure you have IDMU installed on your AD box & users have unix attributes set.
Related videos on Youtube
Author by
Alexey Malov
Updated on September 18, 2022Comments
-
Alexey Malov over 1 year
I have Debian Squeeze and sssd installed. When I try to login to server by user 'alexwinner' by ssh I see in the log:
(Fri May 11 18:56:03 2012) [[sssd[krb5_child[26281]]]] [get_and_save_tgt] (1): 523: [-1765328360][Preauthentication failed]But when I execute
kinit alexwinnerall is ok, I receive ticket. This is my sssd.conf[sssd] config_file_version = 2 reconnection_retries = 3 sbus_timeout = 30 services = nss, pam domains = MYDOMAIN.COM [nss] filter_groups = root filter_users = root reconnection_retries = 3 ; entry_cache_timeout = 600 ; entry_cache_nowait_timeout = 300 [pam] reconnection_retries = 3 [domain/MYDOMAIN.COM] description = LDAP domain with AD server enumerate = true min_id = 1000 cache_credentials = false id_provider = ldap auth_provider = krb5 chpass_provider = krb5 krb5_realm = MYDOMAIN.COM krb5_kdcip = 172.27.250.141 krb5_kpasswd = 172.27.250.141 ldap_pwd_policy = none ldap_id_use_start_tls = false ldap_tls_reqcert = never ldap_uri = ldap://172.27.250.141:3268/ ldap_schema = rfc2307bis ldap_default_bind_dn = [email protected] ldap_default_authtok_type = password ldap_default_authtok = veryhardpassword ldap_user_search_base = ou=linux,ou=users,ou=pro,dc=mydomain,DC=com ldap_user_object_class = user ldap_user_uid_number = uidNumber ldap_user_gid_number = GIDNumber ldap_user_home_directory = unixHomeDirectory ldap_user_shell = loginShell ldap_user_principal = userPrincipalName ldap_user_name = sAMAccountName ldap_user_gecos = displayName ldap_user_uuid = objectGUID ldap_group_search_base = OU=Linux,OU=Roles,DC=mydomain,DC=com ldap_group_object_class = group ldap_group_name = Name ldap_group_gid_number = GidNumber ldap_force_upper_case_realm = Trueand this is my krb5.conf
[libdefaults] default_realm = MYDOMAIN.COM forwardable = true [realms] MYDOMAIN.COM = { kdc = 172.27.250.141 admin_server = 172.27.250.141 }I tried to see tcpdump for kerberos packages and see that padata is different for login and kinit.
What can I do?