Truecrypt v. PGP v. Bitlocker for whole disk encryption?
Solution 1
If you're already using TrueCrypt, there's no compelling reason to switch at this point in time. Most people find BitLocker easier to implement, and if you have the appropriate edition of Windows 7 there's nothing wrong with using it. Its been a long time since I last looked at PGP so I can't really comment there.
In the end you'll do better to focus on making sure things like master passwords are sufficiently complex and hard to guess, that you're locking the logged in account when you're not there, and watching for other commonly missed vectors of attack. You'd be surprised how many "securely encrypted disks" are compromised by having weak authentication measures or are left logged in...
Ultimately the best solution is the one you use. ;)
Solution 2
Using PGP right now in our environment. PGP will prompt for authentication coming out of hibernation as well as system boot, but not from sleep. Not sure about BitLocker or TrueCrypt. I'm looking at evaluating BitLocker right now.
Solution 3
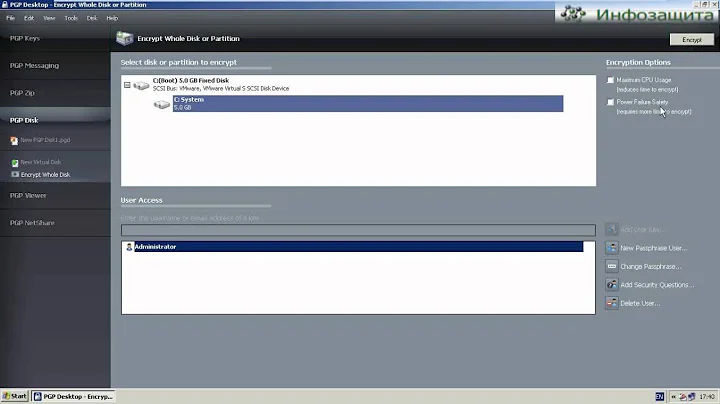
I have tried both PGP and Bitlocker and found that both are easy to implement, but Bitlocker asks for a recovery key every time there is a change in the hardware — it looks like this:
BitLocker Recovery Key: 402853-586311-176957-360866-697576-425466-365607-689666
This key needs to be with you all the time in case the system asks for it, which I find very difficult to memorize or keep comparing to passwords in PGP.
I have seen Bitlocker ask for this key more than once during my Bitlocker tests.
Other advantages of PGP over Bitlocker in my opinion are:
- You don't care what MS OS you are running, if you had to read your drive from a different machine (all you have to do is to install PGP software and you are ready to go)
- You can configure more than one user to access the drive (ex. admin and the regular user)
Disadvantages are maybe in recovering a damaged OS since Windows doesn't have PGP drivers embedded and therefore Windows can not access the drive.
Related videos on Youtube
andrewj
Updated on September 17, 2022Comments
-
andrewj over 1 year
This is a follow up on a previous thread from last year (What software should I use to encrypt my hard drive?): any more thoughts on whole disk encryption? I'm getting a new laptop and am willing to spend some money for a straightforward, easy to implement disk encryption method.
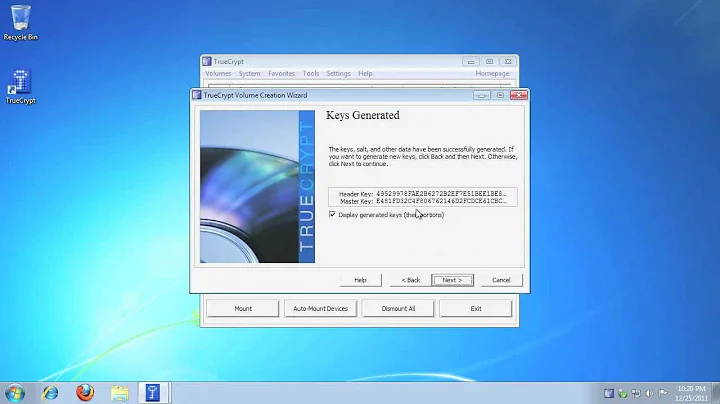
I already use Truecrypt, which has the advantage of being open source and free, but am worried that it may be somewhat clunky to implement for whole disk encryption. It seems on face value, that Bitlocker may be the easiest to use solution, enough to warrant upgrading from Windows 7 Professional to the Ultimate version. On the other hand, I've also seen people use PGP as well.
Also, do any of these programs interfere with the ability of the system to go into hibernation or standby mode or have problems with solid state drives?
-
AnonJr almost 14 yearsIf you're going to reference a prior question, it would help to link to that question so we all know which particular one you are referring to.
-
andrewj almost 14 yearsThe prior thread is superuser.com/questions/127/…
-
 Admin almost 13 yearsthe point of bit locker is that it uses TPM, one of the advantages of TPM is that you dont need a complex password as dictionary attacks are thwarted by the physical implementation of an electronically enforced maximum number of retries.
Admin almost 13 yearsthe point of bit locker is that it uses TPM, one of the advantages of TPM is that you dont need a complex password as dictionary attacks are thwarted by the physical implementation of an electronically enforced maximum number of retries. -
 LawrenceC almost 13 yearsTruecrypt isn't difficult to use at all for full disk encryption unless you have multiple OSes involved. If you're full disk encrypting a standard Windows install, it's not very difficult.
LawrenceC almost 13 yearsTruecrypt isn't difficult to use at all for full disk encryption unless you have multiple OSes involved. If you're full disk encrypting a standard Windows install, it's not very difficult. -
Overmind almost 7 yearsMy vote goes to Truecrypt. I've been using it for years. And yes, it works with W10 and SSDs quite well too.
-
-
 slhck about 12 yearsHow so? Can you provide a reference to back up your claims?
slhck about 12 yearsHow so? Can you provide a reference to back up your claims? -
Zac B over 11 yearsYou can use Group Policy (or local policy) to relax BitLocker's paranoia level about checksum changes to bootloaders etc., reducing the likelihood of it prompting you for the recovery key for no apparent reason. See: technet.microsoft.com/en-us/library/ee706521(v=ws.10).aspx
-
Zac B over 11 yearsI can: hackaday.com/2010/02/09/tpm-crytography-cracked Heck, even Microsoft admits it: windowsteamblog.com/windows/b/windowssecurity/archive/2010/02/… However, that's a pretty involved and delicate hack. I wouldn't worry.
-
soandos over 11 yearsReferences would make this more authoritative