Ubuntu 16.04 openssl s_client write:errno=104
The very boring answer to this is that I was behind a firewall. I'd ruled out a firewall because it was blocking things like google.com and outlook.office.com and I was the only one having the problem.
It turns out that because I'm new in the company I have some configuration (I suspect it's just that my MAC is recognised) on new company laptop (even though it's a fresh Ubuntu install) that means that my traffic gets intercepted by the firewall.
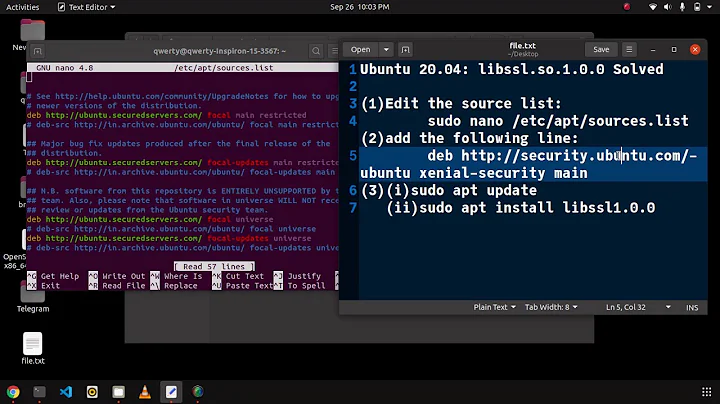
Related videos on Youtube
Comments
-
Todd Baur over 1 year
I'm getting the following error when trying to connect to github.com, google.com, dropbox.com via https, but stackoverflow.com, askubuntu.com and the majority of https websites work.
Relevant details:
- I'm behind a work proxy, but I can connect fine when using Fedora 28, it's just on Ubuntu 16.04 that I have the problem. No one else in the office has the problem, but they are mostly using Macs.
- This is on my own desktop, not on a server/VM/Docker etc.
- I can connect to these websites via my mobile hotspot or on other WiFi networks
- Edit: I tested on a separate Thinkpad laptop with Ubuntu 16.04 and there is no problem on there. So it's something specific to this machine (a Dell XPS 13 9370).
Error message:
$ openssl s_client -connect github.com:443 CONNECTED(00000003) write:errno=104 --- no peer certificate available --- No client certificate CA names sent --- SSL handshake has read 0 bytes and written 311 bytes --- New, (NONE), Cipher is (NONE) Secure Renegotiation IS NOT supported Compression: NONE Expansion: NONE No ALPN negotiated SSL-Session: Protocol : TLSv1.2 Cipher : 0000 Session-ID: Session-ID-ctx: Master-Key: Key-Arg : None PSK identity: None PSK identity hint: None SRP username: None Start Time: 1537527929 Timeout : 300 (sec) Verify return code: 0 (ok) ---I've upgraded OpenSSL to the most recent version but that makes no difference:
$ openssl version OpenSSL 1.0.2p 14 Aug 2018I get the following error when running CURL:
$ curl -v https://google.com * Rebuilt URL to: https://google.com/ * Trying 172.217.17.46... * Connected to google.com (172.217.17.46) port 443 (#0) * found 148 certificates in /etc/ssl/certs/ca-certificates.crt * found 597 certificates in /etc/ssl/certs * ALPN, offering http/1.1 * gnutls_handshake() failed: Error in the pull function. * Closing connection 0 curl: (35) gnutls_handshake() failed: Error in the pull function.There's numerous other answers that have similar problems but I can't find any that deal with my situation:
- 16.04 - curl: (35) gnutls_handshake() failed: Error in the pull function
- https://stackoverflow.com/questions/24457408/openssl-command-to-check-if-a-server-is-presenting-a-certificate
- "error: gnutls_handshake() failed" when connecting to https servers
- https://serverfault.com/questions/892880/curl-gnutls-handshake-failed-error-in-the-pull-function
- Can't connect to certain HTTPS sites
- update fails with "gnutls_handshake() failed: Error in the pull function."
Here's an example of it working with stackoverflow.com:
$ openssl s_client -connect stackoverflow.com:443 CONNECTED(00000003) depth=1 C = US, O = DigiCert Inc, OU = www.digicert.com, CN = DigiCert SHA2 High Assurance Server CA verify error:num=20:unable to get local issuer certificate --- Certificate chain 0 s:/C=US/ST=NY/L=New York/O=Stack Exchange, Inc./CN=*.stackexchange.com i:/C=US/O=DigiCert Inc/OU=www.digicert.com/CN=DigiCert SHA2 High Assurance Server CA 1 s:/C=US/O=DigiCert Inc/OU=www.digicert.com/CN=DigiCert SHA2 High Assurance Server CA i:/C=US/O=DigiCert Inc/OU=www.digicert.com/CN=DigiCert High Assurance EV Root CA --- Server certificate -----BEGIN CERTIFICATE----- MIIHHjCCBgagAwIBAgIQDhG71w1UtxDQxvVAtrUspDANBgkqhkiG9w0BAQsFADBw MQswCQYDVQQGEwJVUzEVMBMGA1UEChMMRGlnaUNlcnQgSW5jMRkwFwYDVQQLExB3 d3cuZGlnaWNlcnQuY29tMS8wLQYDVQQDEyZEaWdpQ2VydCBTSEEyIEhpZ2ggQXNz dXJhbmNlIFNlcnZlciBDQTAeFw0xNjA1MjEwMDAwMDBaFw0xOTA4MTQxMjAwMDBa MGoxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJOWTERMA8GA1UEBxMITmV3IFlvcmsx HTAbBgNVBAoTFFN0YWNrIEV4Y2hhbmdlLCBJbmMuMRwwGgYDVQQDDBMqLnN0YWNr ZXhjaGFuZ2UuY29tMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAr0YD zscT5i6T2FaRsTGNCiLB8OtPXu8N9iAyuaROh/nS0kRRsN8wUMk1TmgZhPuYM6oF S377V8W2LqhLBMrPXi7lnhvKt2DFWCyw38RrDbEsM5dzVGErmhux3F0QqcTI92zj VW61DmE7NSQLiR4yonVpTpdAaO4jSPJxn8d+4p1sIlU2JGSk8LZSWFqaROc7KtXt lWP4HahNRZtdwvL5dIEGGNWx+7B+XVAfY1ygc/UisldkA+a3D2+3WAtXgFZRZZ/1 CWFjKWJNMAI6ZBAtlbgSNgRYxdcdleIhPLCzkzWysfltfiBmsmgz6VCoFR4KgJo8 Gd3MeTWojBthM10SLwIDAQABo4IDuDCCA7QwHwYDVR0jBBgwFoAUUWj/kK8CB3U8 zNllZGKiErhZcjswHQYDVR0OBBYEFFrBQmPCYhOznZSEqjIeF8tto4Z7MIIB6AYD VR0RBIIB3zCCAduCEyouc3RhY2tleGNoYW5nZS5jb22CEXN0YWNrb3ZlcmZsb3cu Y29tghMqLnN0YWNrb3ZlcmZsb3cuY29tgg1zdGFja2F1dGguY29tggtzc3RhdGlj Lm5ldIINKi5zc3RhdGljLm5ldIIPc2VydmVyZmF1bHQuY29tghEqLnNlcnZlcmZh dWx0LmNvbYINc3VwZXJ1c2VyLmNvbYIPKi5zdXBlcnVzZXIuY29tgg1zdGFja2Fw cHMuY29tghRvcGVuaWQuc3RhY2thdXRoLmNvbYIRc3RhY2tleGNoYW5nZS5jb22C GCoubWV0YS5zdGFja2V4Y2hhbmdlLmNvbYIWbWV0YS5zdGFja2V4Y2hhbmdlLmNv bYIQbWF0aG92ZXJmbG93Lm5ldIISKi5tYXRob3ZlcmZsb3cubmV0gg1hc2t1YnVu dHUuY29tgg8qLmFza3VidW50dS5jb22CEXN0YWNrc25pcHBldHMubmV0ghIqLmJs b2dvdmVyZmxvdy5jb22CEGJsb2dvdmVyZmxvdy5jb22CGCoubWV0YS5zdGFja292 ZXJmbG93LmNvbYIVKi5zdGFja292ZXJmbG93LmVtYWlsghNzdGFja292ZXJmbG93 LmVtYWlsMA4GA1UdDwEB/wQEAwIFoDAdBgNVHSUEFjAUBggrBgEFBQcDAQYIKwYB BQUHAwIwdQYDVR0fBG4wbDA0oDKgMIYuaHR0cDovL2NybDMuZGlnaWNlcnQuY29t L3NoYTItaGEtc2VydmVyLWc1LmNybDA0oDKgMIYuaHR0cDovL2NybDQuZGlnaWNl cnQuY29tL3NoYTItaGEtc2VydmVyLWc1LmNybDBMBgNVHSAERTBDMDcGCWCGSAGG /WwBATAqMCgGCCsGAQUFBwIBFhxodHRwczovL3d3dy5kaWdpY2VydC5jb20vQ1BT MAgGBmeBDAECAjCBgwYIKwYBBQUHAQEEdzB1MCQGCCsGAQUFBzABhhhodHRwOi8v b2NzcC5kaWdpY2VydC5jb20wTQYIKwYBBQUHMAKGQWh0dHA6Ly9jYWNlcnRzLmRp Z2ljZXJ0LmNvbS9EaWdpQ2VydFNIQTJIaWdoQXNzdXJhbmNlU2VydmVyQ0EuY3J0 MAwGA1UdEwEB/wQCMAAwDQYJKoZIhvcNAQELBQADggEBAAzJAMGSdKoX1frdqNlN iXu8Gcbsm/DxWMXpcTXlZn8s+/qQQoc+/3o0CK3C8/j9n5DmsYa88P6Ntt5ysDs+ b0ynXFva4CAEyKaoPM4SIpOjwfWBRSUOqAIkQO2/LhKBwT/EnpaIHIKGnI0UdXLQ oDfkMDg6mgJsEBsKdKF5EfEX7iU3NO5xVJPJE8/R0btLAdYwxB9S6fSpCXGe2HqQ D101O/7/4MWNdFSbfdDSFcn5oEm+idimrqiNrF5knmuJy4qPBkL7thNuGK6rvYCF ZJM03ZEZhkQmn2jG/7LgjfwZmvfcITeADCpylf88bL+lf+vxe6cCl9CyqWgBDpsI xpE= -----END CERTIFICATE----- subject=/C=US/ST=NY/L=New York/O=Stack Exchange, Inc./CN=*.stackexchange.com issuer=/C=US/O=DigiCert Inc/OU=www.digicert.com/CN=DigiCert SHA2 High Assurance Server CA --- No client certificate CA names sent Peer signing digest: SHA512 Server Temp Key: ECDH, P-256, 256 bits --- SSL handshake has read 3688 bytes and written 437 bytes --- New, TLSv1/SSLv3, Cipher is ECDHE-RSA-AES128-GCM-SHA256 Server public key is 2048 bit Secure Renegotiation IS supported Compression: NONE Expansion: NONE No ALPN negotiated SSL-Session: Protocol : TLSv1.2 Cipher : ECDHE-RSA-AES128-GCM-SHA256 Session-ID: 6108011C279498322CD465101770BB0F5B33BB71138CBC79FCDF8CAD77595F29 Session-ID-ctx: Master-Key: CC8F5FD8CC5197DA6C57E6BF13A47954A8045202DAD80C9C74C26A358613CFDE4430C27F8347FFC9F38F34AF789AF511 Key-Arg : None PSK identity: None PSK identity hint: None SRP username: None TLS session ticket lifetime hint: 7200 (seconds) TLS session ticket: 0000 - 77 0d 86 c9 22 54 0f 4b-97 9a 3e 46 78 cc 14 46 w..."T.K..>Fx..F 0010 - 2d 82 e9 5f 63 b7 4c ae-de 3e c8 08 4e 35 4b e5 -.._c.L..>..N5K. 0020 - 65 89 ef fa b6 83 a6 25-b6 77 c2 c9 a7 35 a7 95 e......%.w...5.. 0030 - c8 2c f1 98 81 19 20 11-84 10 a1 c6 0d 95 61 6d .,.... .......am 0040 - 68 76 2c fc d2 d1 1e 98-1f b2 36 84 3a 83 e0 20 hv,.......6.:.. 0050 - 75 98 9a ef 53 76 23 e1-03 f1 ef a2 e5 9a de 6f u...Sv#........o 0060 - e8 69 8e a4 9a 57 db 82-3f 19 e4 1b a0 85 19 54 .i...W..?......T 0070 - ba e3 4c 0a f7 30 0f 68-16 6b 40 f2 65 81 db 6f [email protected] 0080 - aa 41 4f 75 79 dd 75 1a-aa b3 66 3f 6c dd 19 70 .AOuy.u...f?l..p 0090 - cf b5 87 72 61 40 cb 1e-73 1a bd 69 92 a3 16 66 [email protected] Start Time: 1537529712 Timeout : 300 (sec) Verify return code: 20 (unable to get local issuer certificate) ---This is the relevant
ifconfigdetails for the proxy connection:wlp2s0 Link encap:Ethernet HWaddr 9c:b6:d0:8e:76:8f inet addr:10.1.64.58 Bcast:10.1.79.255 Mask:255.255.240.0 inet6 addr: fe80::75a:cefe:ae7f:73f1/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:24463 errors:0 dropped:0 overruns:0 frame:0 TX packets:25120 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:13605579 (13.6 MB) TX bytes:5419669 (5.4 MB)
Edit: Output of
ldd $(which curl):$ ldd $(which curl) linux-vdso.so.1 => (0x00007ffd885fc000) libcurl-gnutls.so.4 => /usr/lib/x86_64-linux-gnu/libcurl-gnutls.so.4 (0x00007fd8d24f7000) libz.so.1 => /lib/x86_64-linux-gnu/libz.so.1 (0x00007fd8d22dd000) libpthread.so.0 => /lib/x86_64-linux-gnu/libpthread.so.0 (0x00007fd8d20c0000) libc.so.6 => /lib/x86_64-linux-gnu/libc.so.6 (0x00007fd8d1cf6000) libidn.so.11 => /usr/lib/x86_64-linux-gnu/libidn.so.11 (0x00007fd8d1ac3000) librtmp.so.1 => /usr/lib/x86_64-linux-gnu/librtmp.so.1 (0x00007fd8d18a7000) libnettle.so.6 => /usr/lib/x86_64-linux-gnu/libnettle.so.6 (0x00007fd8d1671000) libgnutls.so.30 => /usr/lib/x86_64-linux-gnu/libgnutls.so.30 (0x00007fd8d1341000) libgssapi_krb5.so.2 => /usr/lib/x86_64-linux-gnu/libgssapi_krb5.so.2 (0x00007fd8d10f7000) liblber-2.4.so.2 => /usr/lib/x86_64-linux-gnu/liblber-2.4.so.2 (0x00007fd8d0ee8000) libldap_r-2.4.so.2 => /usr/lib/x86_64-linux-gnu/libldap_r-2.4.so.2 (0x00007fd8d0c97000) /lib64/ld-linux-x86-64.so.2 (0x00007fd8d2993000) libhogweed.so.4 => /usr/lib/x86_64-linux-gnu/libhogweed.so.4 (0x00007fd8d0a64000) libgmp.so.10 => /usr/lib/x86_64-linux-gnu/libgmp.so.10 (0x00007fd8d07e4000) libp11-kit.so.0 => /usr/lib/x86_64-linux-gnu/libp11-kit.so.0 (0x00007fd8d0580000) libtasn1.so.6 => /usr/lib/x86_64-linux-gnu/libtasn1.so.6 (0x00007fd8d036d000) libkrb5.so.3 => /usr/lib/x86_64-linux-gnu/libkrb5.so.3 (0x00007fd8d009b000) libk5crypto.so.3 => /usr/lib/x86_64-linux-gnu/libk5crypto.so.3 (0x00007fd8cfe6c000) libcom_err.so.2 => /lib/x86_64-linux-gnu/libcom_err.so.2 (0x00007fd8cfc68000) libkrb5support.so.0 => /usr/lib/x86_64-linux-gnu/libkrb5support.so.0 (0x00007fd8cfa5d000) libresolv.so.2 => /lib/x86_64-linux-gnu/libresolv.so.2 (0x00007fd8cf842000) libsasl2.so.2 => /usr/lib/x86_64-linux-gnu/libsasl2.so.2 (0x00007fd8cf627000) libgssapi.so.3 => /usr/lib/x86_64-linux-gnu/libgssapi.so.3 (0x00007fd8cf3e6000) libffi.so.6 => /usr/lib/x86_64-linux-gnu/libffi.so.6 (0x00007fd8cf1de000) libdl.so.2 => /lib/x86_64-linux-gnu/libdl.so.2 (0x00007fd8cefda000) libkeyutils.so.1 => /lib/x86_64-linux-gnu/libkeyutils.so.1 (0x00007fd8cedd6000) libheimntlm.so.0 => /usr/lib/x86_64-linux-gnu/libheimntlm.so.0 (0x00007fd8cebcd000) libkrb5.so.26 => /usr/lib/x86_64-linux-gnu/libkrb5.so.26 (0x00007fd8ce943000) libasn1.so.8 => /usr/lib/x86_64-linux-gnu/libasn1.so.8 (0x00007fd8ce6a1000) libhcrypto.so.4 => /usr/lib/x86_64-linux-gnu/libhcrypto.so.4 (0x00007fd8ce46e000) libroken.so.18 => /usr/lib/x86_64-linux-gnu/libroken.so.18 (0x00007fd8ce258000) libwind.so.0 => /usr/lib/x86_64-linux-gnu/libwind.so.0 (0x00007fd8ce02f000) libheimbase.so.1 => /usr/lib/x86_64-linux-gnu/libheimbase.so.1 (0x00007fd8cde20000) libhx509.so.5 => /usr/lib/x86_64-linux-gnu/libhx509.so.5 (0x00007fd8cdbd5000) libsqlite3.so.0 => /usr/lib/x86_64-linux-gnu/libsqlite3.so.0 (0x00007fd8cd900000) libcrypt.so.1 => /lib/x86_64-linux-gnu/libcrypt.so.1 (0x00007fd8cd6c8000)
Edit 2: Thanks to Simon Sutter for his comments. I have updated to Ubuntu 18.04 in an attempt to resolve it but there are still the similar problems.
Actually the curl error is now slightly different which is useful:
$ curl -v https://google.com * Rebuilt URL to: https://google.com/ * Trying 172.217.19.206... * TCP_NODELAY set * Connected to google.com (172.217.19.206) port 443 (#0) * ALPN, offering h2 * ALPN, offering http/1.1 * successfully set certificate verify locations: * CAfile: /etc/ssl/certs/ca-certificates.crt CApath: /etc/ssl/certs * TLSv1.2 (OUT), TLS handshake, Client hello (1): * OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to google.com:443 * stopped the pause stream! * Closing connection 0 curl: (35) OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to google.com:443Searching for the
SSL_ERROR_SYSCALLbug I came across a SO answer that suggests it might have something to do with IPv6 and suggests tryingwget. This is what I get withwget:$ wget https://stackoverflow.com --2018-09-26 09:33:12-- https://stackoverflow.com/ Resolving stackoverflow.com (stackoverflow.com)... 151.101.129.69, 151.101.193.69, 151.101.1.69, ... Connecting to stackoverflow.com (stackoverflow.com)|151.101.129.69|:443... connected. HTTP request sent, awaiting response... 200 OK Length: 263668 (257K) [text/html] Saving to: ‘index.html’ index.html 100%[=============>] 257.49K 864KB/s in 0.3s 2018-09-26 09:33:13 (864 KB/s) - ‘index.html’ saved [263668/263668] $ wget https://google.com --2018-09-26 09:33:25-- https://google.com/ Resolving google.com (google.com)... 172.217.20.110, 2a00:1450:400e:80a::200e Connecting to google.com (google.com)|172.217.20.110|:443... connected. Unable to establish SSL connection.Interestingly from that google makes an IPv6 request but stackoverflow doesn't. However a further check shows that I have an issue with bitbucket.org too and that makes no indication of an IPv6 connection:
$ wget https://bitbucket.org/ --2018-09-26 10:03:40-- https://bitbucket.org/ Resolving bitbucket.org (bitbucket.org)... 18.205.93.2, 18.205.93.1, 18.205.93.0, ... Connecting to bitbucket.org (bitbucket.org)|18.205.93.2|:443... connected. Unable to establish SSL connection.I did some further checking on this by disabling IPv6 but that made no difference - as in I get the same errors when running
curlorwget.Now because I'm on Ubuntu 18.04 here's an updated set of checks.
$ curl --version curl 7.58.0 (x86_64-pc-linux-gnu) libcurl/7.58.0 OpenSSL/1.1.0g zlib/1.2.11 libidn2/2.0.4 libpsl/0.19.1 (+libidn2/2.0.4) nghttp2/1.30.0 librtmp/2.3 Release-Date: 2018-01-24 Protocols: dict file ftp ftps gopher http https imap imaps ldap ldaps pop3 pop3s rtmp rtsp smb smbs smtp smtps telnet tftp Features: AsynchDNS IDN IPv6 Largefile GSS-API Kerberos SPNEGO NTLM NTLM_WB SSL libz TLS-SRP HTTP2 UnixSockets HTTPS-proxy PSLRelevant
ifconfigdetails:wlp2s0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500 inet 10.1.64.53 netmask 255.255.240.0 broadcast 10.1.79.255 inet6 fe80::75a:cefe:ae7f:73f1 prefixlen 64 scopeid 0x20<link> ether 9c:b6:d0:8e:76:8f txqueuelen 1000 (Ethernet) RX packets 1203608 bytes 1323281319 (1.3 GB) RX errors 0 dropped 0 overruns 0 frame 0 TX packets 434207 bytes 63876155 (63.8 MB) TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0Curl libraries:
$ ldd $(which curl) linux-vdso.so.1 (0x00007ffcba0bb000) libcurl.so.4 => /usr/lib/x86_64-linux-gnu/libcurl.so.4 (0x00007ff5cba6b000) libz.so.1 => /lib/x86_64-linux-gnu/libz.so.1 (0x00007ff5cb84e000) libpthread.so.0 => /lib/x86_64-linux-gnu/libpthread.so.0 (0x00007ff5cb62f000) libc.so.6 => /lib/x86_64-linux-gnu/libc.so.6 (0x00007ff5cb23e000) libnghttp2.so.14 => /usr/lib/x86_64-linux-gnu/libnghttp2.so.14 (0x00007ff5cb019000) libidn2.so.0 => /usr/lib/x86_64-linux-gnu/libidn2.so.0 (0x00007ff5cadfc000) librtmp.so.1 => /usr/lib/x86_64-linux-gnu/librtmp.so.1 (0x00007ff5cabe0000) libpsl.so.5 => /usr/lib/x86_64-linux-gnu/libpsl.so.5 (0x00007ff5ca9d2000) libssl.so.1.1 => /usr/lib/x86_64-linux-gnu/libssl.so.1.1 (0x00007ff5ca768000) libcrypto.so.1.1 => /usr/lib/x86_64-linux-gnu/libcrypto.so.1.1 (0x00007ff5ca2f0000) libgssapi_krb5.so.2 => /usr/lib/x86_64-linux-gnu/libgssapi_krb5.so.2 (0x00007ff5ca0a5000) libldap_r-2.4.so.2 => /usr/lib/x86_64-linux-gnu/libldap_r-2.4.so.2 (0x00007ff5c9e53000) liblber-2.4.so.2 => /usr/lib/x86_64-linux-gnu/liblber-2.4.so.2 (0x00007ff5c9c45000) /lib64/ld-linux-x86-64.so.2 (0x00007ff5cbf21000) libunistring.so.2 => /usr/lib/x86_64-linux-gnu/libunistring.so.2 (0x00007ff5c98c7000) libgnutls.so.30 => /usr/lib/x86_64-linux-gnu/libgnutls.so.30 (0x00007ff5c9562000) libhogweed.so.4 => /usr/lib/x86_64-linux-gnu/libhogweed.so.4 (0x00007ff5c932e000) libnettle.so.6 => /usr/lib/x86_64-linux-gnu/libnettle.so.6 (0x00007ff5c90f8000) libgmp.so.10 => /usr/lib/x86_64-linux-gnu/libgmp.so.10 (0x00007ff5c8e77000) libdl.so.2 => /lib/x86_64-linux-gnu/libdl.so.2 (0x00007ff5c8c73000) libkrb5.so.3 => /usr/lib/x86_64-linux-gnu/libkrb5.so.3 (0x00007ff5c899d000) libk5crypto.so.3 => /usr/lib/x86_64-linux-gnu/libk5crypto.so.3 (0x00007ff5c876b000) libcom_err.so.2 => /lib/x86_64-linux-gnu/libcom_err.so.2 (0x00007ff5c8567000) libkrb5support.so.0 => /usr/lib/x86_64-linux-gnu/libkrb5support.so.0 (0x00007ff5c835c000) libresolv.so.2 => /lib/x86_64-linux-gnu/libresolv.so.2 (0x00007ff5c8141000) libsasl2.so.2 => /usr/lib/x86_64-linux-gnu/libsasl2.so.2 (0x00007ff5c7f26000) libgssapi.so.3 => /usr/lib/x86_64-linux-gnu/libgssapi.so.3 (0x00007ff5c7ce5000) libp11-kit.so.0 => /usr/lib/x86_64-linux-gnu/libp11-kit.so.0 (0x00007ff5c79b6000) libtasn1.so.6 => /usr/lib/x86_64-linux-gnu/libtasn1.so.6 (0x00007ff5c77a3000) libkeyutils.so.1 => /lib/x86_64-linux-gnu/libkeyutils.so.1 (0x00007ff5c759f000) libheimntlm.so.0 => /usr/lib/x86_64-linux-gnu/libheimntlm.so.0 (0x00007ff5c7396000) libkrb5.so.26 => /usr/lib/x86_64-linux-gnu/libkrb5.so.26 (0x00007ff5c7109000) libasn1.so.8 => /usr/lib/x86_64-linux-gnu/libasn1.so.8 (0x00007ff5c6e67000) libhcrypto.so.4 => /usr/lib/x86_64-linux-gnu/libhcrypto.so.4 (0x00007ff5c6c31000) libroken.so.18 => /usr/lib/x86_64-linux-gnu/libroken.so.18 (0x00007ff5c6a1b000) libffi.so.6 => /usr/lib/x86_64-linux-gnu/libffi.so.6 (0x00007ff5c6813000) libwind.so.0 => /usr/lib/x86_64-linux-gnu/libwind.so.0 (0x00007ff5c65ea000) libheimbase.so.1 => /usr/lib/x86_64-linux-gnu/libheimbase.so.1 (0x00007ff5c63db000) libhx509.so.5 => /usr/lib/x86_64-linux-gnu/libhx509.so.5 (0x00007ff5c6191000) libsqlite3.so.0 => /usr/lib/x86_64-linux-gnu/libsqlite3.so.0 (0x00007ff5c5e88000) libcrypt.so.1 => /lib/x86_64-linux-gnu/libcrypt.so.1 (0x00007ff5c5c50000) libm.so.6 => /lib/x86_64-linux-gnu/libm.so.6 (0x00007ff5c58b2000)env | grep -i proxyreturns nothing.Package statuses:
$ dpkg -l curl ca-certificates Desired=Unknown/Install/Remove/Purge/Hold | Status=Not/Inst/Conf-files/Unpacked/halF-conf/Half-inst/trig-aWait/Trig-pend |/ Err?=(none)/Reinst-required (Status,Err: uppercase=bad) ||/ Name Version Architecture Description +++-==============================-====================-====================-================================================================== ii ca-certificates 20180409 all Common CA certificates ii curl 7.58.0-2ubuntu3.3 amd64 command line tool for transferring data with URL syntaxIf it is a certificate error somewhere in the chain I know that I did install a work CA certificate when I first setup the computer.
Edit 3:
Here's a list of the sites that work:
https://duckduckgo.comhttps://*.stackexchange.comhttps://stackoverflow.comhttps://www.getharvest.com/https://www.bbc.com/newshttps://egghead.iohttps://news.ycombinator.comhttps://www.speedtest.net/-
https://ipleak.net/- indicates that I have no IPv6 connection -
https://*.atlassian.net(but bitbucket.org fails)
A list of the sites that fail:
https://google.comhttps://dropbox.comhttps://outlook.live.com/owa/https://bitbucket.orghttps://www.facebook.com/https://www.slack.comhttps://twitter.comhttps://github.com
Half works:
https://outlook.office.com/owa/
The site at https://outlook.office.com/owa/?bO=1 has experienced a network protocol violation that cannot be repaired.
Edit 4:
I think I've made some progress with my Ubuntu problems. It works on a separate Ubuntu 16 laptop that I've tried. Further, I think I've tracked it down to a firewall issue (via this Security.SE answer) and the handling of TLS v1.1 vs TLS v1.2.
I tracked down which sites I could access vs not access (above). An interesting example is bitbucket.org (fails) vs atlassian.net (works).
Then if I try with openssl (forcing TLS v1.1):
openssl s_client -connect bitbucket.org:443 -tls1_1 # this fails openssl s_client -connect atlassian.net:443 -tls1_1 # this worksSo I think that the firewall might be blocking TLS v1.2 traffic in some way.
On my other Ubuntu machine when I run:
openssl s_client -connect bitbucket.org:443 -tls1_1 # this works!Also the same works on a Mac that I tried.
-
Simon Sudler over 5 yearsCan you please add the output of
ldd $(which curl) -
Simon Sudler over 5 yearsYou wrote, that you are behind a proxy server... but
openssl s_clientdoes not work with http proxies. How did the command established the connection (NAT, forwarding proxy)? -
Todd Baur over 5 years@SimonSudler thanks for the comments, I've added the
lddoutput. To be honest I'm at the limits of my knowledge, it's entirely possible I'm just doing completely stupid things. I do know thatopenssl s_clientdoes work on my Fedora laptop which is the only comparison that I've got to work on. I've got Docker installed on my laptop, which could potentially be knackering my network connection, but I'm trying to duplicate a setup that's working fine on Fedora (Docker included). -
Simon Sudler over 5 yearsOkay, I need more information on your environment: Check if there are some proxy settings
env | grep -i proxy. Post some more information on curlcurl --versionanddpkg -l curl ca-certificates. As you can see in thelddoutput, curl does not use openssl, it useslibgnutls.so.30. So there sould not be any impact from the new openssl. -
Todd Baur over 5 years@SimonSudler thanks again, I've tried updating to Ubuntu 18 but I'm still getting the similar errors, I've put in all the info that you requested and done further tests using
wget. Allwget,curlandopensslfail.