Ubuntu 18.04 no DNS resolution when connected to OpenVPN
Solution 1
I found a solution on this blog post. While there are two solutions mentioned, I prefer using the second one because it means my DNS is set by the OpenVPN server (the first solution means I use the same DNS servers whether or not I'm connected to the OpenVPN server).
In short:
sudo mkdir -p /etc/openvpn/scriptssudo wget https://raw.githubusercontent.com/jonathanio/update-systemd-resolved/master/update-systemd-resolved -P /etc/openvpn/scripts/sudo chmod +x /etc/openvpn/scripts/update-systemd-resolved
Then edit your OpenVPN client file (e.g. client.ovpn) by changing the up/down scripts to:
script-security 2
# up /etc/openvpn/update-resolv-conf
# down /etc/openvpn/update-resolv-conf
up /etc/openvpn/scripts/update-systemd-resolved
down /etc/openvpn/scripts/update-systemd-resolved
(I have commented out the original up/down settings).
Solution 2
Problem
The file /etc/resolv.conf does not get updated by the /etc/openvpn/update-resolv-conf script because resolvconf is not installed by default on ubuntu 18.04.
In fact, one of the first lines of that script checks for the /sbin/resolvconf executable:
[ -x /sbin/resolvconf ] || exit 0
Installing resolvconf via apt-get is not a solution as the /etc/openvpn/update-resolv-conf script updates the /etc/resolv.conf file with the pushed DNS entry but the tun device seems to ignore it.
Solution
-
Ubuntu 18.04 uses
systemd-resolved, so all you have to do is install the openvpn helper script forsystemd-resolvedviasudo apt install openvpn-systemd-resolvedor with these GitHub instructions
-
Update your
config.ovpnfile adding these lines:script-security 2 up /etc/openvpn/update-systemd-resolved down /etc/openvpn/update-systemd-resolved down-preThat instead of adding up and down of
/etc/openvpn/update-resolv-confto the conf. -
To prevent DNS Leakage, you should add this line to the end of the
config.ovpnfile (according to this systemd issue comment):dhcp-option DOMAIN-ROUTE .
Solution 3
Actually, there is a much easier solution to this problem. The issue is with DNS traffic and how Ubuntu 18 manages that. By default IP forwarding is disabled which is what OpenVPN needs in order to provide proper networking. All you have to do is run the following command:
sudo nano /etc/sysctl.conf
Once you have this file opened, look for the line that contains net.ipv4.ip_forward. If this line is commented, remove the # sign at the front of the line (if it is not commented then you have another issue). Save the file and then restart your OpenVPN server instance.
This fix does not require any modifications to the client or OpenVPN code following upgrade to Ubuntu 18. Tested and confirmed working.
However, this obviously requires you can administer the server. And unfortunately, the bug exists for many who just connect with 18.04 to an OpenVPN server that is administered by somebody else...
Solution 4
Tested on Ubuntu 18.04 at 13 Sep 2018
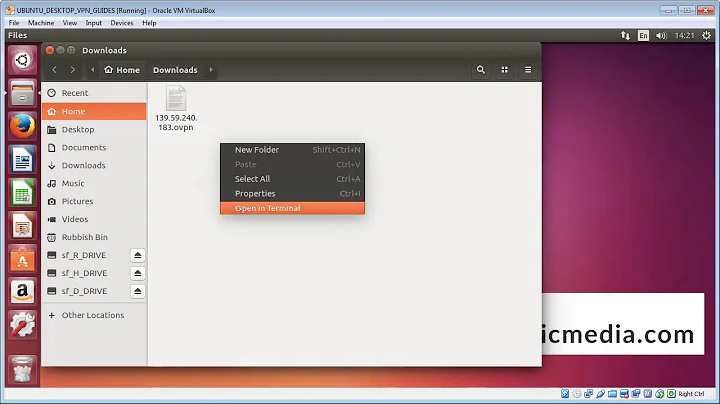
There is another useful command to setup what you need via command line. You can control your VPN connection both with command line and GUI.
sudo nmcli connection add type vpn vpn-type openvpn con-name la.vpn.contoso.com ifname --
ifname -- is the required by default, but does not affect anything
sudo nmcli connection modify la.vpn.contoso.com ipv4.dns 172.16.27.1
sudo nmcli connection modify la.vpn.contoso.com ipv4.dns-search int.contoso.com
sudo nmcli connection modify la.vpn.contoso.com ipv4.never-default yes
never-default should not use remote gateway as default route
And much more interested final touch:
nmcli connection modify la.vpn.contoso.com vpn.data 'ca = /tmp/la.vpn.contoso.com/you/ca.crt, key = /tmp/you.key, dev = tun, cert = /tmp/you.crt, cert-pass-flags = 1, comp-lzo = adaptive, remote = la.vpn.contoso.com:1194, connection-type = tls'
Afterwards you can control vpn with GUI or use following commands:
sudo nmcli --ask connection up la.vpn.contoso.com
sudo nmcli connection down la.vpn.contoso.com
Solution 5
I'm impacted too. In my case, I'm using OpenVPN with an internal name server (which is inside the VPN). That worked until Ubuntu 17.10 (with hosts: files dns in /etc/nsswitch.conf).
/etc/resolv.conf was updated correctly by the openvpn scripts (through calls to /etc/openvpn/update-resolv-conf in the openvpn client configuration file).
However, name resolution for hosts inside the VPN was not working any more (or at least sporadically... I guess the local DNS cache was picking the names, but after a rather long time).
What seems to help, or even resolve the issue (though that's too early to say) is to install the below package:
sudo apt install openvpn-systemd-resolved
Related videos on Youtube
Comments
-
orestis over 1 year
When I connect to a VPN network through Gnome Network-manager I lose DNS resolution and in practice, I cannot access resources inside the VPN network or outside.
When I was using Ubuntu 16.04 and I was using the VPN, the "
/etc/resolv.conf/" file would contain the DNS servers of the (VPN) network I had connected. Now it always contains the following entries:nameserver 127.0.0.53 search myprovider.comFrom what I have understood
127.0.0.53is the address of the DNS stub used by thesystem-resolved.I suspect that this is a bug because the VPN was working fine the Ubuntu 16.04. Is there any way that I can set the DNS servers of my network when I am using a VPN service?
Update:
I tried connecting to the OpenVPN network with the configuration file attached at the end of the post, but I get the following error:
Authenticate/Decrypt packet error: cipher final failedI have verified that the server uses lzo compression and I have enabled it as well. The connection stays active but I cannot navigate to any page inside or outside the VPN.
In the configuration file listed below, I have included the solutions posted in the replies
client dev tun proto udp remote openvpn.bibsys.no 1194 remote my-server-2 1194 resolv-retry infinite nobind user myuser group myuser persist-key persist-tun ca ca-cert.pem cert openvpn.crt key openvpn.key cipher AES-256-CBC comp-lzo yes script-security 2 up /etc/openvpn/scripts/update-systemd-resolved down /etc/openvpn/scripts/update-systemd-resolved down-pre-
notbad.jpeg about 5 yearsWhen debugging a similar problem to this that couldn't be solved exactly the same, I used
resolvectl statusandresolvectl helpto figure out my specific solution.
-
-
Michael Opdenacker about 6 yearsEventually, it doesn't seem to be a solution. I have the problem again. I guess something else made it work...
-
orestis about 6 yearsIf one is using the gnome openvpn utility where should the file config.ovpn be stored?
-
Andy Turfer almost 6 years
config.ovpnisn't "found" - it's the client config file used for connecting. You either generate it, or it is issued to you by your OpenVPN provider (and it might not be calledconfig.ovpn- it could be called anything, likeclient.ovpn). -
 lucidyan almost 6 yearsThanks a lot, working for me on Ubuntu 18.04. And I want to specify, that parameter
lucidyan almost 6 yearsThanks a lot, working for me on Ubuntu 18.04. And I want to specify, that parameterscript-security 2is still needed before up/down lines, otherwise the program falls down with an error (OpenVPN 2.4.4) -
Qlimax almost 6 yearsGlad it helped :) Changed the last sentence in the answer, with in my case
script-security 2was not necessary. That's perhaps because I'm running the openvpn client as root (with sudo) -
n1ghtm4n4g3r almost 6 yearsI am running the client as root and I still (also) need to add
script-security 2for this setup to work. BTW, thanks a lot for this tip, @Qlimax. :-) -
orestis almost 6 years@Qlimax Do you know how do we import these settings to the gnome openvpn client?
-
Qlimax almost 6 years@orestis you have to install this package
sudo apt-get install network-manager-openvpn-gnomeThen you should be able to import .ovpn config files into the gnome network manager. askubuntu.com/questions/187511/… UI has changed over time, you should be able to find that in settings->network->vpn -
 lucidyan almost 6 yearsMaybe then you delete your answer? It seems that the decision has already been found below
lucidyan almost 6 yearsMaybe then you delete your answer? It seems that the decision has already been found below -
hwjp over 5 yearsdidn't work for me. how did you determine that this was the problem, in your case?
-
Vanessa Deagan over 5 yearsThis should be the accepted answer.
-
Ahsanul Haque over 5 yearsThis works just perfectly.
-
A. Ahanchi about 5 yearsThanks! The last line for preventing dns leakage is necessary because the systems still uses the default dns.
-
blockhead about 5 yearsI get
WARNING: Failed running command (--up/--down): external program fork failed -
higuita almost 5 yearsWARNING: you do not need to enable ip_forward on the openvpn client, NEVER! it is a security risk. On the openvpn server, you may need it, depending on the config used and this is probably why this comment show up.
-
 Harald almost 5 yearsSurprised this works for so many of you: I have an ovpn.config, yes, but NetworkManager does not seem to use it. Did you edit the file and the re-import it, in particular to replace the up/downs scripts. Because I see this opaque binary /usr/lib/NetworkManager/nm-openvpn-service-openvpn-helper used for which i could not find documentation. If re-import of ovpn.config is needed, please amend the answer.
Harald almost 5 yearsSurprised this works for so many of you: I have an ovpn.config, yes, but NetworkManager does not seem to use it. Did you edit the file and the re-import it, in particular to replace the up/downs scripts. Because I see this opaque binary /usr/lib/NetworkManager/nm-openvpn-service-openvpn-helper used for which i could not find documentation. If re-import of ovpn.config is needed, please amend the answer. -
 Saisurya Kattamuri over 4 yearsUnfortunately this didn’t work for a vpn which is using tcp, sites outside vpn are not resolved, hence I started using client.pritunl.com/#install found useful
Saisurya Kattamuri over 4 yearsUnfortunately this didn’t work for a vpn which is using tcp, sites outside vpn are not resolved, hence I started using client.pritunl.com/#install found useful -
 lucidyan over 4 yearsWithout
lucidyan over 4 yearsWithoutdown-prein the end of .ovpn file, you would get nasty warnings at stopupdate-systemd-resolved: Invalid device name: 'tun0'. Usage: update-systemd-resolved up|down device_name. WARNING: Failed running command (--up/--down): external program exited with error status: 1 Exiting due to fatal error -
 Milan Maharjan over 4 yearsthis worked for me as well
Milan Maharjan over 4 yearsthis worked for me as well -
 Kevin C over 4 yearsThis was it for me. Weird issue. Thanks.
Kevin C over 4 yearsThis was it for me. Weird issue. Thanks. -
Karl Forner over 4 yearsthis seems to work for me ! Thanks. I tested so many different fixes...
-
Joao Tavora over 4 yearsCan't +1 this enough. It really should be the accepted answer
-
Mnemosyne over 4 yearsThis did not work for me either. Am having the exact same issue.
-
Falc over 4 yearsMy client.ovpn file doesn't have up and down lines, can I just add them?
-
chaz about 4 yearsDidn't work for me at first because my resolv.conf was still looking at my router dns. I made sure the stub was used first (127.0.0.53) on ubuntu 19.10, and it worked. I still can't figure out how to get the stub resolver to do the local then remote resolving by itself, but this is a good workaround for now.
-
Andy Turfer about 4 years@Falc Yes, you can.
-
Amit Patil about 4 yearsSorry but not worked with me.
-
Zorglub29 almost 4 yearsIs it expected that this should solve Pritunl problems on Ubuntu 20.04 too?
-
Shayan almost 4 yearsAdding the
script-security 2and (up/down)/etc/openvpn/update-resolv-conflines fixed it for me. -
nekofar over 3 yearsThank you! This is still valid for Ubuntu 20.04.1 LTS.
-
foo over 2 yearsas of 2021-10, there's also the package "openvpn-systemd-resolved" as part of standard repositories, instead of referring to some githubusercontent URL.
-
JonnyRaa over 2 yearsthe final line
dhcp-option DOMAIN-ROUTE .was critical - my problem wasn't fixed until I added that aswell -
axel22 about 2 yearsBest. Answer. On the Internet. Thanks - it took me a while until I found your answer, the part that
resolveconfshould have been installed.

![Quick fix This site cant be reached Ubuntu [DNS_PROBE_FINISHED]/fix DNS server errors (Technoder)](https://i.ytimg.com/vi/_J0Lsmucx08/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLAe1TULSbhHjyjrh2prDlqGRGx6CA)

