Usefulness of packets in wireshark? SSDP protocol, rather than HTTP?
Solution 1
... all of the HTTP traffic is coming through as the SSDP protocol ...
Nope, all of your HTTP traffic is still coming over traditional TCP. You are just being flooded with SSDP packets and unable to separate these from real HTTP packets.
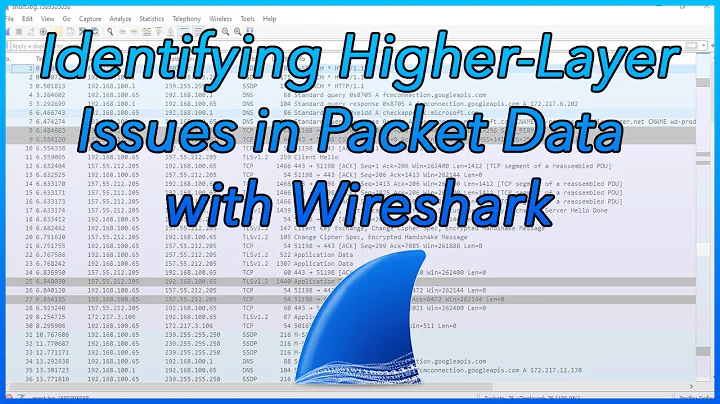
Easiest way to filter the "real" HTTP traffic is to type in to the Wireshark filter box:
http && tcp
And likewise if you wish to view (mostly) SSDP HTTP packets use this for filtering:
http && udp
Solution 2
SSDP is just like HTTP except it works with NOTIFY and M-SEARCH methods. If you use the filter http in Wireshark, you'll still see these packets displayed. This protocol allows you to discover and configure devices using uPnP automatically, this process is referred to as SSDP Discovery. If you're using iChat, I know that application for a fact uses SSDP. Basically it just detects and configures communications with other uPnP devices on the network for you.
Related videos on Youtube
Jimmy Lyke
Updated on September 17, 2022Comments
-
Jimmy Lyke over 1 year
I used to be able to filter my wireshark packets to get useful information from them. However, with my current configuration on OSX, all of the HTTP traffic is coming through as the SSDP protocol and is generally being unhelpful. Why is this?
Actually, it seems that packets on my own system that should be HTTP are coming throuhg as HTTP, but packets from other machines that should be HTTP are coming through as this protocol.
-
Jimmy Lyke about 14 yearsRight. But how can I view these like normal HTTP packets (such as the get and post parameters)?