Using AWS Secrets Manager with Python (Lambda Console)
Solution 1
update the last part of get_secret() to:
else:
# Decrypts secret using the associated KMS CMK.
# Depending on whether the secret is a string or binary, one of these fields will be populated.
if 'SecretString' in get_secret_value_response:
secret = get_secret_value_response['SecretString']
else:
secret = base64.b64decode(get_secret_value_response['SecretBinary'])
return json.loads(secret) # returns the secret as dictionary
This will return a dictionary where you'll have the keys you specified in AWS Secret Manager console.
Solution 2
- Here is how i have used it using arn, following this bloc hope that helps you.
- Worth checking what you have used to store and accordingly use one
SecretStringorSecretBinary
secrets_client = boto3.client('secretsmanager')
secret_arn = 'arn:aws:secretsmanager:eu-west-2:xxxxxxxxxxxx:secret:dashboard/auth_token'
auth_token = secrets_client.get_secret_value(SecretId=secret_arn).get('SecretString')
- boto3 docs
-
get_secret_value Retrieves the contents of the encrypted fields
SecretStringorSecretBinaryfrom the specified version of a secret, whichever contains content. - Your lambda role should have the following permissions depending on what is used
secretsmanager:GetSecretValue-
kms:Decryptrequired only if you use a customer-managed AWS KMS key to encrypt the secret. You do not need this permission to use the account's default AWS managed CMK for Secrets Manager.
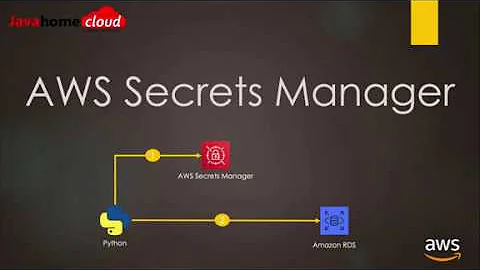
Related videos on Youtube
jeff
Updated on July 09, 2022Comments
-
jeff almost 2 years
I am attempting to use Secrets Manager a Lambda function in AWS. Secrets a manager is used to store database credentials to Snowflake (username, password).
I managed to set up a secret in Secrets Manager which contains several key/value pairs (e.g. one for username, another for password).
Now I am trying to refer to these values in my Python function code. AWS documentation kindly provides the following snippet:
import boto3 import base64 from botocore.exceptions import ClientError def get_secret(): secret_name = "MY/SECRET/NAME" region_name = "us-west-2" # Create a Secrets Manager client session = boto3.session.Session() client = session.client( service_name='secretsmanager', region_name=region_name ) # In this sample we only handle the specific exceptions for the 'GetSecretValue' API. # See https://docs.aws.amazon.com/secretsmanager/latest/apireference/API_GetSecretValue.html # We rethrow the exception by default. try: get_secret_value_response = client.get_secret_value( SecretId=secret_name ) except ClientError as e: if e.response['Error']['Code'] == 'DecryptionFailureException': # Secrets Manager can't decrypt the protected secret text using the provided KMS key. # Deal with the exception here, and/or rethrow at your discretion. raise e elif e.response['Error']['Code'] == 'InternalServiceErrorException': # An error occurred on the server side. # Deal with the exception here, and/or rethrow at your discretion. raise e elif e.response['Error']['Code'] == 'InvalidParameterException': # You provided an invalid value for a parameter. # Deal with the exception here, and/or rethrow at your discretion. raise e elif e.response['Error']['Code'] == 'InvalidRequestException': # You provided a parameter value that is not valid for the current state of the resource. # Deal with the exception here, and/or rethrow at your discretion. raise e elif e.response['Error']['Code'] == 'ResourceNotFoundException': # We can't find the resource that you asked for. # Deal with the exception here, and/or rethrow at your discretion. raise e else: # Decrypts secret using the associated KMS CMK. # Depending on whether the secret is a string or binary, one of these fields will be populated. if 'SecretString' in get_secret_value_response: secret = get_secret_value_response['SecretString'] else: decoded_binary_secret = base64.b64decode(get_secret_value_response['SecretBinary']) # Your code goes here.Later in my
def lambda_handler(event, context)function, I have the following snippet to establish a connection to my database:conn = snowflake.connector.connect( user=USERNAME, password=PASSWORD, account=ACCOUNT, warehouse=WAREHOUSE, role=ROLE )However, I am unable to figure out how to use the
get_secret()function to return values for parameters likeUSERNAMEorPASSWORD.How can this be accomplished? Thank you for the help!
-
Munavir Chavody over 4 yearsCalling the function inside the handler function isn't working?
-
-
Prashanth kumar over 4 yearsreturning the secret as json helped me. +1, Thanks
-
django-unchained about 4 years@Prashanthkumar Did you get dictionary just by adding the
return? I am struggling to get my credentials. -
Prashanth kumar about 4 years@django-unchained, hope you got it covered already, but otherwise, I just enclosed the
base64.b64decode(get_secret_value_response['SecretBinary'])insidejson.loadswhen assinging it to variable "secret", after that I could access the credentials assecret["username"]secret["password"], or whatever your variables are inside the secrets manager secret. -
Denise over 3 yearscan u provide your code ? im stuck in this situation for days
-
 Sarde about 2 yearsI am getting following error [ERROR] UnboundLocalError: local variable 'secret' referenced before assignment
Sarde about 2 yearsI am getting following error [ERROR] UnboundLocalError: local variable 'secret' referenced before assignment