What is the proper iptables configuration for Apache Solr on CentOS?
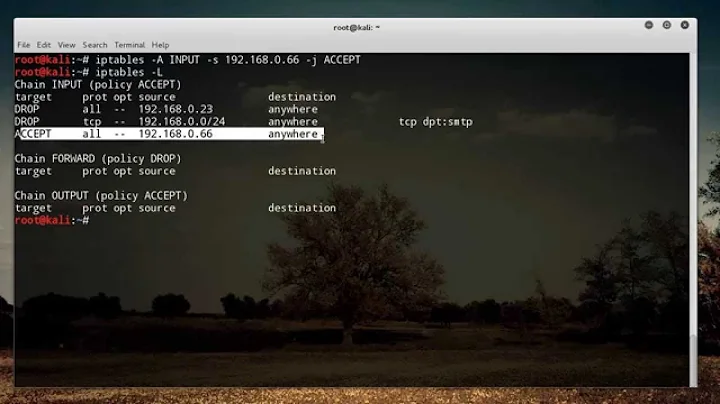
The order of iptables rules is important, as first-match-wins. Red Hat, like most sensible people, usually puts a blanket REJECT at the end of its chain, and adding rules to permit solr traffic - or any other kind of traffic - after that won't help, as the packet will never get that far down the chain.
If this is what's biting you, you need to do an iptables -L -n -v --line-number, find the number of the blanket rule at the end, and use iptables -I RH-Firewall-1-INPUT n ... to insert your ACCEPT at line number n, where n is less than the number of the blanket REJECT.
Edit: thanks for the listing. See that blanket REJECT all -- * * at the end? There's no point adding your ACCEPT after that, as you'll never get that far. Try doing the --line-number listing to find out where you need to insert that line - anywhere before the last line should do - and see if that works.
Edit 2: can you also confirm that netstat -an|grep 8983 on the server returns something sensible?
Edit 3: then your server's not listening on port 8983, which is why you can't connect to it even after opening up the port in the firewall. If you had a listener on that port, you'd see something like
[madhatta@www mail]$ netstat -an|grep 443
tcp 0 0 193.219.118.100:443 0.0.0.0:* LISTEN
The above example being taken from my webserver, which is why it's port 443 not 8983. You're going to need to find out why there's no listener on 8983 before we can make any more progress.
Edit 4: you can't connect to a daemon that's not listening. I know you said that "taking down the firewall fixes everything", and that may have been true when the daemon was listening; but right now I doubt it. If you're willing to repeat the experiment: taking the firewall down, confirming that netstat -an|grep 8983 on the server still returns nothing, and then showing that telnet server 8983 gives a connection, I shall be pleasantly surprised.
Edit 5: glad to help!
Related videos on Youtube
syn4k
Updated on September 18, 2022Comments
-
syn4k almost 2 years
I know for a fact that iptables running is causing my instance of Apache Solr to be inaccessible. How do I know this? Because I ran:
/sbin/service iptables save && /sbin/service iptables stopOnce I did this, everything worked flawlessly.
I would like to continue using my firewall however, adding the necessary rules for it doesn't seem to be working. I have exhausted what I thought would work:
/sbin/service iptables start /sbin/iptables -A RH-Firewall-1-INPUT -p tcp -s 127.0.0.1 --dport 8983 -j ACCEPT /sbin/service iptables saveStill not working
/sbin/iptables -D RH-Firewall-1-INPUT -p tcp -s 127.0.0.1 --dport 8983 -j ACCEPT /sbin/iptables -A RH-Firewall-1-INPUT -p tcp --dport 8983 -j ACCEPT /sbin/service iptables saveStill not working
I even tried doing a general ACCEPT on the 8983 port:
/sbin/iptables -A INPUT -p tcp --dport 8983 -j ACCEPT /sbin/service iptables saveStill not working!
Ideas?
**/sbin/iptables -L -n -v** Chain INPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 215K 50M RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:8983 Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 0 0 RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain OUTPUT (policy ACCEPT 279K packets, 286M bytes) pkts bytes target prot opt in out source destination Chain RH-Firewall-1-INPUT (2 references) pkts bytes target prot opt in out source destination 14286 19M ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0 8 672 ACCEPT icmp -- * * 0.0.0.0/0 0.0.0.0/0 icmp type 255 0 0 ACCEPT esp -- * * 0.0.0.0/0 0.0.0.0/0 0 0 ACCEPT ah -- * * 0.0.0.0/0 0.0.0.0/0 0 0 ACCEPT udp -- * * 0.0.0.0/0 224.0.0.251 udp dpt:5353 0 0 ACCEPT udp -- * * 0.0.0.0/0 0.0.0.0/0 udp dpt:631 0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:631 181K 29M ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 2 164 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:55 148 7676 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:8008 2 120 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22 11208 621K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:80 2202 123K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:443 5372 951K REJECT all -- * * 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibitedUPDATE (added before last rule):
*# /sbin/iptables -L -n -v --line-numbers* Chain INPUT (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination 1 585K 123M RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination 1 0 0 RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain OUTPUT (policy ACCEPT 782K packets, 822M bytes) num pkts bytes target prot opt in out source destination Chain RH-Firewall-1-INPUT (2 references) num pkts bytes target prot opt in out source destination 1 31867 43M ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0 2 27 2232 ACCEPT icmp -- * * 0.0.0.0/0 0.0.0.0/0 icmp type 255 3 0 0 ACCEPT esp -- * * 0.0.0.0/0 0.0.0.0/0 4 0 0 ACCEPT ah -- * * 0.0.0.0/0 0.0.0.0/0 5 0 0 ACCEPT udp -- * * 0.0.0.0/0 224.0.0.251 udp dpt:5353 6 0 0 ACCEPT udp -- * * 0.0.0.0/0 0.0.0.0/0 udp dpt:631 7 0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:631 8 502K 76M ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 9 4 268 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:55 10 189 9780 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:8008 11 8 480 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22 12 29633 1656K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:80 13 6138 345K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:443 14 14841 2635K REJECT all -- * * 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited *# /sbin/iptables --insert RH-Firewall-1-INPUT 14 -p tcp --dport 8983 -j ACCEPT # /sbin/iptables -L -n -v --line-numbers* Chain INPUT (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination 1 599K 127M RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination 1 0 0 RH-Firewall-1-INPUT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain OUTPUT (policy ACCEPT 801K packets, 841M bytes) num pkts bytes target prot opt in out source destination Chain RH-Firewall-1-INPUT (2 references) num pkts bytes target prot opt in out source destination 1 32631 44M ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0 2 27 2232 ACCEPT icmp -- * * 0.0.0.0/0 0.0.0.0/0 icmp type 255 3 0 0 ACCEPT esp -- * * 0.0.0.0/0 0.0.0.0/0 4 0 0 ACCEPT ah -- * * 0.0.0.0/0 0.0.0.0/0 5 0 0 ACCEPT udp -- * * 0.0.0.0/0 224.0.0.251 udp dpt:5353 6 0 0 ACCEPT udp -- * * 0.0.0.0/0 0.0.0.0/0 udp dpt:631 7 0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:631 8 514K 78M ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 9 4 268 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:55 10 292 15136 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:8008 11 8 480 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22 12 30425 1701K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:80 13 6304 355K ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:443 14 0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:8983 15 15130 2690K REJECT all -- * * 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibitedEven though the ACCEPT rule was added before the last line of the RH-Firewall-1-INPUT Chain, it is still not working
-
stew about 12 yearsOne vitally useful piece of information when trying to debug a set of firewall rules, is the actual firewall rules :) can you show us the output of either
iptables-saveoriptables -L -n -v
-
-
syn4k about 12 yearsI added the iptables listing above for debugging.
-
stew about 12 yearsand this confirms that he's on the right track. your current firwall rules say that all INPUT goes to the RH-Firewall-1-INPUT chain, and if nothing matches there, then it tries the one you added to accept 8093, however the last rule of RH-Firewall-1-INPUT always matches, so it never hits your rule. Insert your rule before the last rule of RH-Firewall-1-INPUT or as the first rule of INPUT
-
syn4k about 12 yearsThanks again but adding the rule before the last line of the RH-Firewall-1-INPUT Chain, it is still not working. See above.
-
MadHatter about 12 yearsLet's see your new
iptables -L -n -v, after adding the rule, preferably in your question, above. -
syn4k about 12 yearsI have already provided this above. Look for the line after "/sbin/iptables --insert RH-Firewall-1-INPUT 14 -p tcp --dport 8983 -j ACCEPT" Thanks.
-
syn4k about 12 yearsThe new accept rule I added is on line 14 and the last rule was bumped to line 15
-
MadHatter about 12 yearsOK, sorry, I see it. What happens when, from the client, you do
telnet server 8983? -
syn4k about 12 yearsImmediate, Connection refused
-
MadHatter about 12 yearsCan you tell us if the packet count on the ACCEPT rule you added (column 2 of line 14) has increased from zero?
-
syn4k about 12 yearsYes, it went from 0packets, 0bytes to 3packets 192bytes.
-
syn4k about 12 yearsNothing was returned when running "netstat -an|grep 8983" on the server
-
syn4k about 12 yearsI don't understand how a listener has anything to do with this. Remember, disabling the firewall fixes everything.
-
syn4k about 12 yearsOk, I guess somehow...this is no longer working. Which makes no sense to me. I tried to telnet and it was forcibly rejected even with the firewall off. Nothing was returned when running "netstat -an|grep 8983" on the server, again. Also, "telnet server 8983" returned "Connection refused". The daemon is in fact running. I'll look into it more....