Which permissions/policies for IAM role to be used with CloudWatch monitoring script
Solution 1
The Amazon CloudWatch Monitoring Scripts for Linux are comprised of two Perl scripts, both using one Perl module - a short peek into the source reveals the following AWS API actions being used:
-
CloudWatchClient.pm- DescribeTags -
mon-get-instance-stats.pl- GetMetricStatistics, ListMetrics -
mon-put-instance-data.pl- PutMetricData
With this information you can assemble your IAM policy, e.g. via the AWS policy generator - an all encompassing policy would be:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"cloudwatch:GetMetricStatistics",
"cloudwatch:ListMetrics",
"cloudwatch:PutMetricData",
"ec2:DescribeTags"
],
"Effect": "Allow",
"Resource": "*"
}
]
}
Of course you can drop cloudwatch:GetMetricStatistics cloudwatch:ListMetricswhen just using mon-put-instance-data.pl - please note that I haven't actually tested the code though.
Solution 2
There's an Amazon provided IAM policy for CloudWatch. No need to build your own. CloudWatchFullAccess
Solution 3
The above policy gives error asking for version.
The following should work:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Stmt1426849513000",
"Effect": "Allow",
"Action": [
"cloudwatch:GetMetricStatistics",
"cloudwatch:ListMetrics",
"cloudwatch:PutMetricAlarm",
"cloudwatch:PutMetricData",
"cloudwatch:SetAlarmState"
],
"Resource": [
"*"
]
}
]
}
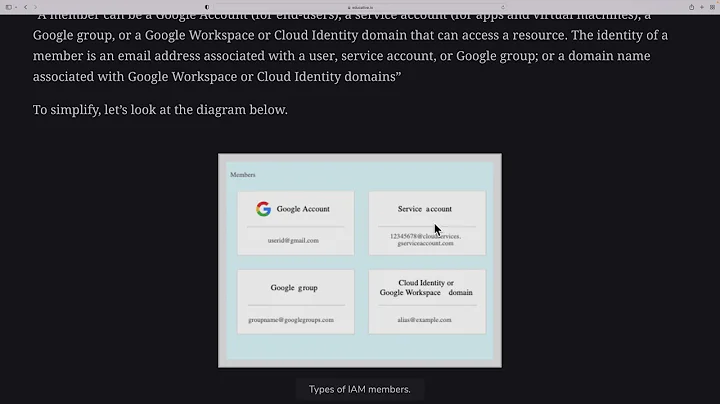
Related videos on Youtube
Céline Aussourd
Updated on September 18, 2022Comments
-
Céline Aussourd over 1 year
With CloudWatch monitoring script (mon-put-instance-data.pl) it's possible to specify a IAM role name to provide AWS credentials (--aws-iam-role=VALUE).
I'm creating a IAM role for this purpose (to run mon-put-instance-data.pl on an AWS instance), but which permissions / policies should I give to this role??
Thank you for your help
-
Céline Aussourd almost 9 yearsThanks for your answer. I didn't want to give full access to CloudWatch though... I don't want to give DeleteAlarms permission for example.
-
htaccess almost 7 yearsThese actions match the actions listed in the documentation at docs.aws.amazon.com/AWSEC2/latest/UserGuide/…
-
sparcboy over 5 yearsFor dynatrace service this is perfect!
-
Ralph Bolton over 5 yearsIMHO, for almost any 'monitoring' use-case, this is too much access. Your monitoring script doesn't need to (say) create or delete metrics or dashboards. The policy adds some fairly safe looking non-cloudwatch permissions, but then adds all of these too: docs.aws.amazon.com/AmazonCloudWatch/latest/monitoring/…. At a rough guess,
CloudWatchReadOnlyAccesswould be a safe 'first try', but even that may be overly generous.