Windows 10 connection to strongswan ipsec server fails with "IKE authentication credentials are unacceptable
Turns out that the problem was with the intermediate Let's Encrypt certificate, despite it being included in my server's cert file. Putting it in /etc/ipsec.d/cacerts solved the problem.
Related videos on Youtube
Kayson
Updated on September 18, 2022Comments
-
Kayson over 1 year
I'm trying to get a simple IPSEC/IKEv2 server set up with username/password (for now) on Ubuntu 18.04.
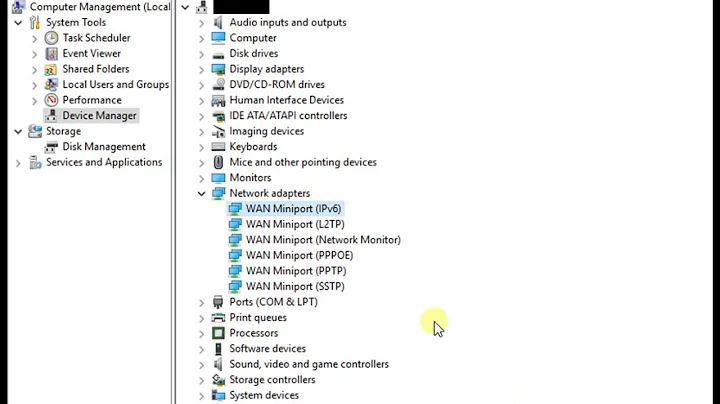
I'm using Windows 10 Pro built in client, and the connection fails complaining about the IKE authentication credentials. The event log shows error 13801, which according to https://blogs.technet.microsoft.com/rrasblog/2009/08/12/troubleshooting-common-vpn-related-errors/ could be any one of
- The machine certificate used for IKEv2 validation on RAS Server does not have 'Server Authentication' as the EKU (Enhanced Key Usage).
- The machine certificate on RAS server has expired.
- The root certificate to validate the RAS server certificate is not present on the client.
- VPN Server Name as given on client doesn’t match with the subjectName of the server certificate.
I'm using a full chain certificate from letsencrypt. I'm not sure how to check the certificate received on the windows side, but I exported the certificate via firefox (I'm using the same cert for an apache2 webserver) to take a look. In
Enhanced Key Usage, I haveServer Authentication (1.3.6.1.5.5.7.3.1). TheSubjectisCN = domain.comwhich is the same domain I'm connecting to (i.e. no subdomains). The cert chain goes to the rootDST Root CA X3, which is in my Trusted Root Certification Authorities Store.My ipsec.conf is as follows:
# ipsec.conf - strongSwan IPsec configuration file config setup charondebug="cfg 2" conn ikev2-vpn auto=add compress=no type=tunnel keyexchange=ikev2 fragmentation=yes forceencaps=yes ike=aes256-sha1-modp1024,3des-sha1-modp1024! esp=aes256-sha1,3des-sha1! dpdaction=clear dpddelay=300s rekey=no left=%any [email protected] leftauth=pubkey leftcert=/etc/ssl/certs/domain.com.pem leftsendcert=always leftsubnet=0.0.0.0/0 right=%any rightid=%any rightauth=eap-mschapv2 rightdns=192.168.1.1 rightsourceip=10.11.12.0/24 rightsendcert=never eap_identity=%identityThe log for this connection is as follows:
Wed, 2018-07-04 17:20 00[DMN] Starting IKE charon daemon (strongSwan 5.6.2, Linux 4.15.0-23-generic, x86_64) Wed, 2018-07-04 17:20 00[LIB] plugin 'aesni': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'aes': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'rc2': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'sha2': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'sha1': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'md4': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'md5': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'mgf1': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'random': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'nonce': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'x509': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'revocation': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'constraints': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pubkey': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pkcs1': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pkcs7': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pkcs8': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pkcs12': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pgp': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'dnskey': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'sshkey': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'pem': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'openssl': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'fips-prf': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'gmp': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'agent': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'xcbc': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'hmac': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'gcm': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'attr': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'kernel-netlink': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'resolve': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'socket-default': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'connmark': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'stroke': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'updown': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'eap-mschapv2': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'xauth-generic': loaded successfully Wed, 2018-07-04 17:20 00[LIB] plugin 'counters': loaded successfully Wed, 2018-07-04 17:20 00[KNL] known interfaces and IP addresses: Wed, 2018-07-04 17:20 00[KNL] lo Wed, 2018-07-04 17:20 00[KNL] 127.0.0.1 Wed, 2018-07-04 17:20 00[KNL] ::1 Wed, 2018-07-04 17:20 00[KNL] enp1s0 Wed, 2018-07-04 17:20 00[KNL] 192.168.1.2 Wed, 2018-07-04 17:20 00[KNL] fe80::428d:5cff:fe05:6216 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY:ED25519 in plugin 'pem' has unmet dependency: PUBKEY:ED25519 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY:BLISS in plugin 'pem' has unmet dependency: PUBKEY:BLISS Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY:DSA in plugin 'pem' has unmet dependency: PUBKEY:DSA Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY:DSA in plugin 'pem' has unmet dependency: PRIVKEY:DSA Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY:BLISS in plugin 'pem' has unmet dependency: PRIVKEY:BLISS Wed, 2018-07-04 17:20 00[LIB] feature CERT_DECODE:OCSP_REQUEST in plugin 'pem' has unmet dependency: CERT_DECODE:OCSP_REQUEST Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY_SIGN:RSA_EMSA_PKCS1_SHA3_224 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_224 Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY_SIGN:RSA_EMSA_PKCS1_SHA3_256 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_256 Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY_SIGN:RSA_EMSA_PKCS1_SHA3_384 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_384 Wed, 2018-07-04 17:20 00[LIB] feature PRIVKEY_SIGN:RSA_EMSA_PKCS1_SHA3_512 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_512 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY_VERIFY:RSA_EMSA_PKCS1_SHA3_224 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_224 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY_VERIFY:RSA_EMSA_PKCS1_SHA3_256 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_256 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY_VERIFY:RSA_EMSA_PKCS1_SHA3_384 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_384 Wed, 2018-07-04 17:20 00[LIB] feature PUBKEY_VERIFY:RSA_EMSA_PKCS1_SHA3_512 in plugin 'gmp' has unmet dependency: HASHER:HASH_SHA3_512 Wed, 2018-07-04 17:20 00[CFG] loading ca certificates from '/etc/ipsec.d/cacerts' Wed, 2018-07-04 17:20 00[CFG] loading aa certificates from '/etc/ipsec.d/aacerts' Wed, 2018-07-04 17:20 00[CFG] loading ocsp signer certificates from '/etc/ipsec.d/ocspcerts' Wed, 2018-07-04 17:20 00[CFG] loading attribute certificates from '/etc/ipsec.d/acerts' Wed, 2018-07-04 17:20 00[CFG] loading crls from '/etc/ipsec.d/crls' Wed, 2018-07-04 17:20 00[CFG] loading secrets from '/etc/ipsec.secrets' Wed, 2018-07-04 17:20 00[CFG] loaded RSA private key from '/etc/ssl/private/strongswan.key' Wed, 2018-07-04 17:20 00[CFG] loaded EAP secret for aram %any% Wed, 2018-07-04 17:20 00[LIB] loaded plugins: charon aesni aes rc2 sha2 sha1 md4 md5 mgf1 random nonce x509 revocation constraints pubkey pkcs1 pkcs7 pkcs8 pkcs12 pgp dnskey sshkey pem openssl fips-prf gmp agent xcbc hmac gcm attr kernel-netlink resolve socket-default connmark stroke updown eap-mschapv2 xauth-generic counters Wed, 2018-07-04 17:20 00[LIB] unable to load 14 plugin features (14 due to unmet dependencies) Wed, 2018-07-04 17:20 00[LIB] dropped capabilities, running as uid 0, gid 0 Wed, 2018-07-04 17:20 00[JOB] spawning 16 worker threads Wed, 2018-07-04 17:20 01[LIB] created thread 01 [24678] Wed, 2018-07-04 17:20 04[LIB] created thread 04 [24680] Wed, 2018-07-04 17:20 06[LIB] created thread 06 [24681] Wed, 2018-07-04 17:20 11[LIB] created thread 11 [24686] Wed, 2018-07-04 17:20 12[LIB] created thread 12 [24688] Wed, 2018-07-04 17:20 13[LIB] created thread 13 [24687] Wed, 2018-07-04 17:20 05[LIB] created thread 05 [24683] Wed, 2018-07-04 17:20 14[LIB] created thread 14 [24689] Wed, 2018-07-04 17:20 08[LIB] created thread 08 [24684] Wed, 2018-07-04 17:20 16[LIB] created thread 16 [24691] Wed, 2018-07-04 17:20 10[LIB] created thread 10 [24685] Wed, 2018-07-04 17:20 02[LIB] created thread 02 [24676] Wed, 2018-07-04 17:20 07[LIB] created thread 07 [24679] Wed, 2018-07-04 17:20 03[LIB] created thread 03 [24677] Wed, 2018-07-04 17:20 09[LIB] created thread 09 [24682] Wed, 2018-07-04 17:20 15[LIB] created thread 15 [24690] Wed, 2018-07-04 17:20 03[CFG] received stroke: add connection 'ikev2-vpn' Wed, 2018-07-04 17:20 03[CFG] conn ikev2-vpn Wed, 2018-07-04 17:20 03[CFG] left=%any Wed, 2018-07-04 17:20 03[CFG] leftsubnet=0.0.0.0/0 Wed, 2018-07-04 17:20 03[CFG] leftauth=pubkey Wed, 2018-07-04 17:20 03[CFG] [email protected] Wed, 2018-07-04 17:20 03[CFG] leftcert=/etc/ssl/certs/domain.com.pem Wed, 2018-07-04 17:20 03[CFG] right=%any Wed, 2018-07-04 17:20 03[CFG] rightsourceip=10.11.12.0/24 Wed, 2018-07-04 17:20 03[CFG] rightdns=192.168.1.1 Wed, 2018-07-04 17:20 03[CFG] rightauth=eap-mschapv2 Wed, 2018-07-04 17:20 03[CFG] rightid=%any Wed, 2018-07-04 17:20 03[CFG] eap_identity=%identity Wed, 2018-07-04 17:20 03[CFG] ike=aes256-sha1-modp1024,3des-sha1-modp1024! Wed, 2018-07-04 17:20 03[CFG] esp=aes256-sha1,3des-sha1! Wed, 2018-07-04 17:20 03[CFG] dpddelay=300 Wed, 2018-07-04 17:20 03[CFG] dpdtimeout=150 Wed, 2018-07-04 17:20 03[CFG] dpdaction=1 Wed, 2018-07-04 17:20 03[CFG] sha256_96=no Wed, 2018-07-04 17:20 03[CFG] mediation=no Wed, 2018-07-04 17:20 03[CFG] keyexchange=ikev2 Wed, 2018-07-04 17:20 03[CFG] adding virtual IP address pool 10.11.12.0/24 Wed, 2018-07-04 17:20 03[CFG] loaded certificate "CN=domain.com" from '/etc/ssl/certs/domain.com.pem' Wed, 2018-07-04 17:20 03[CFG] added configuration 'ikev2-vpn' Wed, 2018-07-04 17:20 02[NET] <1> received packet: from 142.68.61.15[500] to 192.168.1.2[500] (616 bytes) Wed, 2018-07-04 17:20 02[ENC] <1> parsed IKE_SA_INIT request 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) V V V V ] Wed, 2018-07-04 17:20 02[CFG] <1> looking for an ike config for 192.168.1.2...142.68.61.15 Wed, 2018-07-04 17:20 02[CFG] <1> candidate: %any...%any, prio 28 Wed, 2018-07-04 17:20 02[CFG] <1> found matching ike config: %any...%any with prio 28 Wed, 2018-07-04 17:20 02[IKE] <1> received MS NT5 ISAKMPOAKLEY v9 vendor ID Wed, 2018-07-04 17:20 02[IKE] <1> received MS-Negotiation Discovery Capable vendor ID Wed, 2018-07-04 17:20 02[IKE] <1> received Vid-Initial-Contact vendor ID Wed, 2018-07-04 17:20 02[ENC] <1> received unknown vendor ID: 01:52:8b:bb:c0:06:96:12:18:49:ab:9a:1c:5b:2a:51:00:00:00:02 Wed, 2018-07-04 17:20 02[IKE] <1> 142.68.61.15 is initiating an IKE_SA Wed, 2018-07-04 17:20 02[IKE] <1> IKE_SA (unnamed)[1] state change: CREATED => CONNECTING Wed, 2018-07-04 17:20 02[CFG] <1> selecting proposal: Wed, 2018-07-04 17:20 02[CFG] <1> no acceptable ENCRYPTION_ALGORITHM found Wed, 2018-07-04 17:20 02[CFG] <1> selecting proposal: Wed, 2018-07-04 17:20 02[CFG] <1> proposal matches Wed, 2018-07-04 17:20 02[CFG] <1> received proposals: IKE:3DES_CBC/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024, IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024, IKE:3DES_CBC/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_1024, IKE:AES_CBC_256/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_1024, IKE:3DES_CBC/HMAC_SHA2_384_192/PRF_HMAC_SHA2_384/MODP_1024, IKE:AES_CBC_256/HMAC_SHA2_384_192/PRF_HMAC_SHA2_384/MODP_1024 Wed, 2018-07-04 17:20 02[CFG] <1> configured proposals: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024, IKE:3DES_CBC/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024 Wed, 2018-07-04 17:20 02[CFG] <1> selected proposal: IKE:AES_CBC_256/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024 Wed, 2018-07-04 17:20 02[LIB] <1> size of DH secret exponent: 1023 bits Wed, 2018-07-04 17:20 02[IKE] <1> local host is behind NAT, sending keep alives Wed, 2018-07-04 17:20 02[IKE] <1> remote host is behind NAT Wed, 2018-07-04 17:20 02[ENC] <1> generating IKE_SA_INIT response 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) N(MULT_AUTH) ] Wed, 2018-07-04 17:20 02[NET] <1> sending packet: from 192.168.1.2[500] to 142.68.61.15[500] (312 bytes) Wed, 2018-07-04 17:20 13[NET] <1> received packet: from 142.68.61.15[4500] to 192.168.1.2[4500] (1452 bytes) Wed, 2018-07-04 17:20 13[ENC] <1> parsed IKE_AUTH request 1 [ IDi CERTREQ N(MOBIKE_SUP) CPRQ(ADDR DNS NBNS SRV ADDR6 DNS6 SRV6) SA TSi TSr ] Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 73:68:b1:9a:19:83:cc:4b:37:b3:45:44:5d:ef:a5:45:46:ee:ff:a4 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 0e:ac:82:60:40:56:27:97:e5:25:13:fc:2a:e1:0a:53:95:59:e4:a4 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid f8:16:51:3c:fd:1b:44:9f:2e:6b:28:a1:97:22:1f:b8:1f:51:4e:3c Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid dd:bc:bd:86:9c:3f:07:ed:40:e3:1b:08:ef:ce:c4:d1:88:cd:3b:15 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 4a:5c:75:22:aa:46:bf:a4:08:9d:39:97:4e:bd:b4:a3:60:f7:a0:1d Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 5c:b8:69:fe:8d:ef:c1:ed:66:27:ee:b2:12:0f:72:1b:b8:0a:0e:04 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 6a:47:a2:67:c9:2e:2f:19:68:8b:9b:86:61:66:95:ed:c1:2c:13:00 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 01:f0:33:4c:1a:a1:d9:ee:5b:7b:a9:de:43:bc:02:7d:57:09:33:fb Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid b7:95:e9:ff:7d:9c:f0:b1:62:4f:a1:c8:f6:0b:e6:37:20:12:b9:e5 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 1b:e3:ae:ad:0f:c1:1d:d0:15:5b:2d:1d:c5:19:13:71:a4:63:95:5b Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 3c:a2:80:2a:31:80:fd:5b:a6:12:86:fb:55:3a:77:ba:e8:0c:12:ad Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 88:a9:5a:ef:c0:84:fc:13:74:41:6b:b1:63:32:c2:cf:92:59:bb:3b Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 34:4f:30:2d:25:69:31:91:ea:f7:73:5c:ab:f5:86:8d:37:82:40:ec Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 3e:df:29:0c:c1:f5:cc:73:2c:eb:3d:24:e1:7e:52:da:bd:27:e2:f0 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid ab:76:88:f4:e5:e1:38:c9:e9:50:17:cd:cd:b3:18:17:b3:3e:8c:f5 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid da:ed:64:74:14:9c:14:3c:ab:dd:99:a9:bd:5b:28:4d:8b:3c:c9:d8 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 5e:8c:53:18:22:60:1d:56:71:d6:6a:a0:cc:64:a0:60:07:43:d5:a8 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 86:26:cb:1b:c5:54:b3:9f:bd:6b:ed:63:7f:b9:89:a9:80:f1:f4:8a Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid c0:7a:98:68:8d:89:fb:ab:05:64:0c:11:7d:aa:7d:65:b8:ca:cc:4e Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid a8:e3:02:96:70:a6:8b:57:eb:ec:ef:cc:29:4e:91:74:9a:d4:92:38 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid b5:99:33:43:ac:a2:17:c5:08:ba:88:8c:a6:92:7e:26:b3:0f:87:a9 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid f7:93:19:ef:df:c1:f5:20:fb:ac:85:55:2c:f2:d2:8f:5a:b9:ca:0b Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 30:a4:e6:4f:de:76:8a:fc:ed:5a:90:84:28:30:46:79:2c:29:15:70 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 48:e6:68:f9:2b:d2:b2:95:d7:47:d8:23:20:10:4f:33:98:90:9f:d4 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 73:97:82:ea:b4:04:16:6e:25:d4:82:3c:37:db:f8:a8:12:fb:cf:26 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 69:9f:1b:7a:e9:b8:da:18:49:6c:60:8b:ce:4f:4e:aa:f9:f0:b7:aa Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 69:c4:27:db:59:69:68:18:47:e2:52:17:0a:e0:e5:7f:ab:9d:ef:0f Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid ba:42:b0:81:88:53:88:1d:86:63:bd:4c:c0:5e:08:fe:ea:6e:bb:77 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 87:db:d4:5f:b0:92:8d:4e:1d:f8:15:67:e7:f2:ab:af:d6:2b:67:75 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 6e:58:4e:33:75:bd:57:f6:d5:42:1b:16:01:c2:d8:c0:f5:3a:9f:6e Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 4a:81:0c:de:f0:c0:90:0f:19:06:42:31:35:a2:a2:8d:d3:44:fd:08 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid d5:2e:13:c1:ab:e3:49:da:e8:b4:95:94:ef:7c:38:43:60:64:66:bd Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 59:79:12:de:61:75:d6:6f:c4:23:b7:77:13:74:c7:96:de:6f:88:72 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 6c:ca:bd:7d:b4:7e:94:a5:75:99:01:b6:a7:df:d4:5d:1c:09:1c:cc Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid ab:30:d3:af:4b:d8:f1:6b:58:69:ee:45:69:29:da:84:b8:73:94:88 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 42:32:b6:16:fa:04:fd:fe:5d:4b:7a:c3:fd:f7:4c:40:1d:5a:43:af Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid a5:06:8a:78:cf:84:bd:74:32:dd:58:f9:65:eb:3a:55:e7:c7:80:dc Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid e2:7f:7b:d8:77:d5:df:9e:0a:3f:9e:b4:cb:0e:2e:a9:ef:db:69:77 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 5f:f3:24:6c:8f:91:24:af:9b:5f:3e:b0:34:6a:f4:2d:5c:a8:5d:cc Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 6d:aa:9b:09:87:c4:d0:d4:22:ed:40:07:37:4d:19:f1:91:ff:de:d3 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 83:31:7e:62:85:42:53:d6:d7:78:31:90:ec:91:90:56:e9:91:b9:e3 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 7e:95:9f:ed:82:8e:2a:ed:c3:7c:0d:05:46:31:ef:53:97:cd:48:49 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 39:e8:80:35:f8:a2:05:a0:08:b4:cd:e9:d8:ca:67:29:22:2e:7e:9b Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 3e:22:d4:2c:1f:02:44:b8:04:10:65:61:7c:c7:6b:ae:da:87:29:9c Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 55:e4:81:d1:11:80:be:d8:89:b9:08:a3:31:f9:a1:24:09:16:b9:70 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid b1:81:08:1a:19:a4:c0:94:1f:fa:e8:95:28:c1:24:c9:9b:34:ac:c7 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 21:0f:2c:89:f7:c4:cd:5d:1b:82:5e:38:d6:c6:59:3b:a6:93:75:ae Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 23:4b:71:25:56:13:e1:30:dd:e3:42:69:c9:cc:30:d4:6f:08:41:e0 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid bb:c2:3e:29:0b:b3:28:77:1d:ad:3e:a2:4d:bd:f4:23:bd:06:b0:3d Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid b0:19:89:e7:ef:fb:4a:af:cb:14:8f:58:46:39:76:22:41:50:e1:ba Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid ee:e5:9f:1e:2a:a5:44:c3:cb:25:43:a6:9a:5b:d4:6a:25:bc:bb:8e Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 67:ec:9f:90:2d:cd:64:ae:fe:7e:bc:cd:f8:8c:51:28:f1:93:2c:12 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 17:4a:b8:2b:5f:fb:05:67:75:27:ad:49:5a:4a:5d:c4:22:cc:ea:4e Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 68:33:0e:61:35:85:21:59:29:83:a3:c8:d2:d2:e1:40:6e:7a:b3:c1 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 9c:a9:8d:00:af:74:0d:dd:81:80:d2:13:45:a5:8b:8f:2e:94:38:d6 Wed, 2018-07-04 17:20 13[IKE] <1> received cert request for unknown ca with keyid 4f:9c:7d:21:79:9c:ad:0e:d8:b9:0c:57:9f:1a:02:99:e7:90:f3:87 Wed, 2018-07-04 17:20 13[IKE] <1> received 56 cert requests for an unknown ca Wed, 2018-07-04 17:20 13[CFG] <1> looking for peer configs matching 192.168.1.2[%any]...142.68.61.15[192.168.1.133] Wed, 2018-07-04 17:20 13[CFG] <1> candidate "ikev2-vpn", match: 1/1/28 (me/other/ike) Wed, 2018-07-04 17:20 13[CFG] <ikev2-vpn|1> selected peer config 'ikev2-vpn' Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> EAP-Identity request configured, but not supported Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> initiating EAP_MSCHAPV2 method (id 0x52) Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP4_ADDRESS attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP4_DNS attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP4_NBNS attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP4_SERVER attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP6_ADDRESS attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP6_DNS attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> processing INTERNAL_IP6_SERVER attribute Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> peer supports MOBIKE Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> authentication of 'domain.com' (myself) with RSA signature successful Wed, 2018-07-04 17:20 13[IKE] <ikev2-vpn|1> sending end entity cert "CN=domain.com" Wed, 2018-07-04 17:20 13[ENC] <ikev2-vpn|1> generating IKE_AUTH response 1 [ IDr CERT AUTH EAP/REQ/MSCHAPV2 ] Wed, 2018-07-04 17:20 13[NET] <ikev2-vpn|1> sending packet: from 192.168.1.2[4500] to 142.68.61.15[4500] (2460 bytes) Wed, 2018-07-04 17:20 05[IKE] <ikev2-vpn|1> sending keep alive to 142.68.61.15[4500] Wed, 2018-07-04 17:20 14[JOB] <ikev2-vpn|1> deleting half open IKE_SA with 142.68.61.15 after timeout Wed, 2018-07-04 17:20 14[IKE] <ikev2-vpn|1> IKE_SA ikev2-vpn[1] state change: CONNECTING => DESTROYINGAny help would be greatly appreciated!
-
 Zalán Meggyesi over 5 yearsHow did you reach this conclusion? I'm getting the same error in a similar setup, but with the intermediate already in place, and I want to debug it, but I can't get usable debug output from Windows...
Zalán Meggyesi over 5 yearsHow did you reach this conclusion? I'm getting the same error in a similar setup, but with the intermediate already in place, and I want to debug it, but I can't get usable debug output from Windows... -
Kayson over 5 yearsI think I used the strongswan app on android which has more useful logging. I believe it said something in the logs