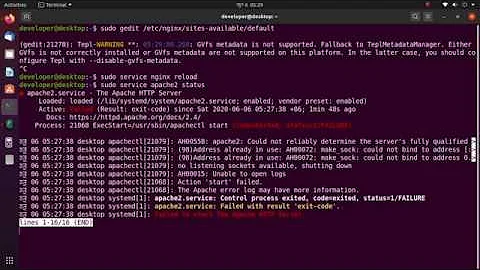
Address already in use, could not bind to address [::]:443
Solution 1
Use the 'netstat' utility to identify the process that is listening on tcp port 443. You can then uninstall the other process or reconfigure it to use a different port.
Steps:
- Login as root
- run 'netstat -napt' to list all processes using tcp, their ports and the pid/process name
root@xbuntu:~# netstat -napt Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 0.0.0.0:139 0.0.0.0:* LISTEN 1441/smbd tcp 0 0 127.0.1.1:53 0.0.0.0:* LISTEN 1251/dnsmasq tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1100/sshd tcp 0 0 127.0.0.1:631 0.0.0.0:* LISTEN 4527/cupsd tcp 0 0 0.0.0.0:445 0.0.0.0:* LISTEN 1441/smbd tcp 0 0 192.168.230.130:22 192.168.230.1:49679 ESTABLISHED 2089/sshd: raja [pr tcp 0 0 192.168.230.130:46890 91.189.88.162:80 TIME_WAIT - tcp6 0 0 :::139 :::* LISTEN 1441/smbd tcp6 0 0 :::80 :::* LISTEN 4828/apache2 tcp6 0 0 :::443 :::* LISTEN 4828/apache2 tcp6 0 0 :::22 :::* LISTEN 1100/sshd tcp6 0 0 ::1:631 :::* LISTEN 4527/cupsd tcp6 0 0 :::445 :::* LISTEN 1441/smbd root@xbuntu:~#
- Look for :443 in the 'local address' column (see bold line above).
- Identify pid and process in 'PID/Program name' column.
- You can then either reconfigure or kill the identified process. If the process is started as a service, you'll need to use the 'service' command to stop it (since killing it will automatically restart it).
Solution 2
You screenshot says the, have another service using the listener in port number 443 (HTTPS), use the command bellow for check name of service
sudo netstat -ntupl | grep :443
If this command says in "PID/Program name" colum "apache2", try restart, and not start apache2 with command
sudo service apache2 restart
For check you apache2 configuration use
sudo apachectl configtest
Related videos on Youtube
sasuke_X220
Updated on September 18, 2022Comments
-
sasuke_X220 over 1 year
I am trying to set up SSL within my ubuntu 14.04 server. After generating my self-signed RSA certificate and setting up all necessary configuration, my server failed to start. All my
/var/log/apache2/error.log,/var/log/apache2/access.logand/var/log/apache2/other_vhosts_access.logare empty however I am getting this message from the console :My
/etc/apache2directory tree :/etc/apache2 |---> ... other files |---> ssl |---> server.key |---> server.crt |---> ports.conf |---> sites-available | |---> default-ssl.conf |---> sites-enabled | |---> default-ssl.confChecking if the the default configuration is enabled :
$sudo a2ensite default-ssl.conf Site default-ssl already enabledThe content of
default-ssl.conf:$cat default-ssl.conf <IfModule mod_ssl.c> <VirtualHost _default_:443> ServerAdmin webmaster@localhost ServerName NetSec DocumentRoot /var/www/html # Available loglevels: trace8, ..., trace1, debug, info, notice, warn, # error, crit, alert, emerg. # It is also possible to configure the loglevel for particular # modules, e.g. #LogLevel info ssl:warn ErrorLog ${APACHE_LOG_DIR}/error.log CustomLog ${APACHE_LOG_DIR}/access.log combined # For most configuration files from conf-available/, which are # enabled or disabled at a global level, it is possible to # include a line for only one particular virtual host. For example the # following line enables the CGI configuration for this host only # after it has been globally disabled with "a2disconf". #Include conf-available/serve-cgi-bin.conf # SSL Engine Switch: # Enable/Disable SSL for this virtual host. SSLEngine on # A self-signed (snakeoil) certificate can be created by installing # the ssl-cert package. See # /usr/share/doc/apache2/README.Debian.gz for more info. # If both key and certificate are stored in the same file, only the # SSLCertificateFile directive is needed. #SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem SSLCertificateKeyFile /etc/apache2/ssl/server.key # Server Certificate Chain: # Point SSLCertificateChainFile at a file containing the # concatenation of PEM encoded CA certificates which form the # certificate chain for the server certificate. Alternatively # the referenced file can be the same as SSLCertificateFile # when the CA certificates are directly appended to the server # certificate for convinience. SSLCertificateChainFile /etc/apache2/ssl/server.crt # Certificate Authority (CA): # Set the CA certificate verification path where to find CA # certificates for client authentication or alternatively one # huge file containing all of them (file must be PEM encoded) # Note: Inside SSLCACertificatePath you need hash symlinks # to point to the certificate files. Use the provided # Makefile to update the hash symlinks after changes. #SSLCACertificatePath /etc/ssl/certs/ #SSLCACertificateFile /etc/apache2/ssl.crt/ca-bundle.crt # Certificate Revocation Lists (CRL): # Set the CA revocation path where to find CA CRLs for client # authentication or alternatively one huge file containing all # of them (file must be PEM encoded) # Note: Inside SSLCARevocationPath you need hash symlinks # to point to the certificate files. Use the provided # Makefile to update the hash symlinks after changes. #SSLCARevocationPath /etc/apache2/ssl.crl/ #SSLCARevocationFile /etc/apache2/ssl.crl/ca-bundle.crl # Client Authentication (Type): # Client certificate verification type and depth. Types are # none, optional, require and optional_no_ca. Depth is a # number which specifies how deeply to verify the certificate # issuer chain before deciding the certificate is not valid. #SSLVerifyClient require #SSLVerifyDepth 10 # SSL Engine Options: # Set various options for the SSL engine. # o FakeBasicAuth: # Translate the client X.509 into a Basic Authorisation. This means that # the standard Auth/DBMAuth methods can be used for access control. The # user name is the `one line' version of the client's X.509 certificate. # Note that no password is obtained from the user. Every entry in the user # file needs this password: `xxj31ZMTZzkVA'. # o ExportCertData: # This exports two additional environment variables: SSL_CLIENT_CERT and # SSL_SERVER_CERT. These contain the PEM-encoded certificates of the # server (always existing) and the client (only existing when client # authentication is used). This can be used to import the certificates # into CGI scripts. # o StdEnvVars: # This exports the standard SSL/TLS related `SSL_*' environment variables. # Per default this exportation is switched off for performance reasons, # because the extraction step is an expensive operation and is usually # useless for serving static content. So one usually enables the # exportation for CGI and SSI requests only. # o OptRenegotiate: # This enables optimized SSL connection renegotiation handling when SSL # directives are used in per-directory context. #SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire <FilesMatch "\.(cgi|shtml|phtml|php)$"> SSLOptions +StdEnvVars </FilesMatch> <Directory /usr/lib/cgi-bin> SSLOptions +StdEnvVars </Directory> # SSL Protocol Adjustments: # The safe and default but still SSL/TLS standard compliant shutdown # approach is that mod_ssl sends the close notify alert but doesn't wait for # the close notify alert from client. When you need a different shutdown # approach you can use one of the following variables: # o ssl-unclean-shutdown: # This forces an unclean shutdown when the connection is closed, i.e. no # SSL close notify alert is send or allowed to received. This violates # the SSL/TLS standard but is needed for some brain-dead browsers. Use # this when you receive I/O errors because of the standard approach where # mod_ssl sends the close notify alert. # o ssl-accurate-shutdown: # This forces an accurate shutdown when the connection is closed, i.e. a # SSL close notify alert is send and mod_ssl waits for the close notify # alert of the client. This is 100% SSL/TLS standard compliant, but in # practice often causes hanging connections with brain-dead browsers. Use # this only for browsers where you know that their SSL implementation # works correctly. # Notice: Most problems of broken clients are also related to the HTTP # keep-alive facility, so you usually additionally want to disable # keep-alive for those clients, too. Use variable "nokeepalive" for this. # Similarly, one has to force some clients to use HTTP/1.0 to workaround # their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and # "force-response-1.0" for this. BrowserMatch "MSIE [2-6]" \ nokeepalive ssl-unclean-shutdown \ downgrade-1.0 force-response-1.0 # MSIE 7 and newer should be able to use keepalive BrowserMatch "MSIE [17-9]" ssl-unclean-shutdown </VirtualHost> </IfModule>The content of
ports.conffile :$cat /etc/apache2/ports.conf Listen 80 Listen 443 <ifModule ssl_module> Listen 443 </ifModule> <ifModule mod_gnutls.c> Listen 443 <ifModule>The symbol link pointing to
default-ssl.confis well established :$ls -l /etc/apache2/sites-enabled/default-ssl.conf lrwxrwxrwx 1 root root 35 Jun 25 15:42 default-ssl.conf -> ../sites-available/default-ssl.confAt the end I would like to stress that I have checked the completeness of my private key/certificate and the check does hold. I have followed actually the steps mentioned in this tutorial in order to generate my self-signed server certificate.
Any help will be more than appreciated. Thank you.
-
David Schwartz almost 7 yearsYou have three
Listen 443statements. If more than one of them activates, you'll have a problem.
-


![Getting "(98)Address already in use: make_sock: could not bind to address [::]:443" when...](https://i.ytimg.com/vi/up-kDcZHAaA/hqdefault.jpg?sqp=-oaymwEcCOADEI4CSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBFjbhcU4wFNuz0nhl-S2d-hBbbyw)

![DevOps & SysAdmins: Address already in use, could not bind to address [::]:443 (2 Solutions!!)](https://i.ytimg.com/vi/5c8Samfeyrc/hqdefault.jpg?sqp=-oaymwEcCOADEI4CSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLA6ByimS0fyBxVPZWktlZO7qLqx5Q)