Authenticated Users and Group Policies
Solution 1
The "group" (really a Security Principal) Authenticated Users is a collection of users and computers which authenticate to the domain. From "Well-known security identifiers in Windows operating systems":
SID: S-1-5-11
Name: Authenticated Users
Description: A group that includes all users whose identities were authenticated when they logged on. Membership is controlled by the operating system.
Security filtering can be used to apply [or prevent application of] policies to specific groups of users/computers. Typically you link a GPO within an OU and the policy applies to all users/computers within this OU. With filtering you can say: "apply this policy to only users in these groups within this OU".
When a policy's Security Filter is Authenticated Users is means the policy will apply to all users/computers which have authenticated to the domain. Of course, barring loop-back processing enabled, Computer Configuration settings will only apply to computer objects and User Configuration settings will only apply to user objects.
Solution 2
Computers have accounts in AD which they use for their own authentication and access to objects, so you can lock things down so that only 'known' AD users, including computers, can access an object. This does make sense with GPOs if you think about it.
Related videos on Youtube
Kyle Brandt
Updated on September 17, 2022Comments
-
 Kyle Brandt over 1 year
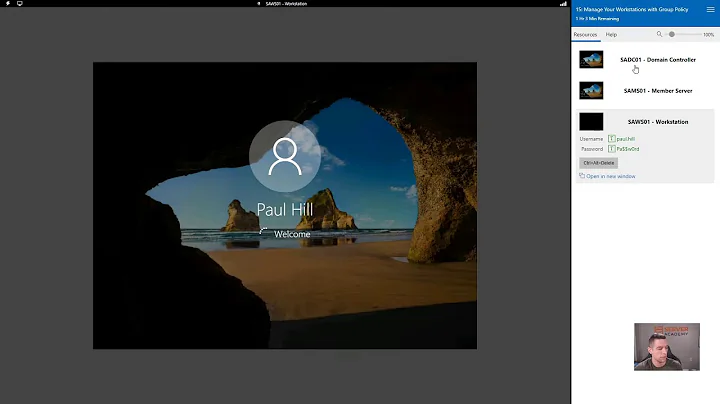
Kyle Brandt over 1 yearI don't fully understand the default Authenticated Users security filtering for group policies in Windows. When I set up WSUS I left this even though that falls under "Computer Configuration" and is only attached to Computer Objects.
Should this basically always be left in place, if so, what is the exact purpose?
The particular use case this time around is for a software install that is being placed under Computer Configuration.