Block all internet connections unless connected to OpenVPN server
First Allow your local connection and your RELATED, ESTABLISHED connections protocols.
$ sudo iptables -A INPUT -p tcp -s 127.0.0.1 -j ACCEPT
$ sudo iptables -A INPUT -p tcp -m state --state RELATED,ESTABLISHED -j ACCEPT
$ sudo iptables -A INPUT -p udp -m state --state RELATED,ESTABLISHED -j ACCEPT
$ sudo iptables -A INPUT -p icmp -m state --state RELATED,ESTABLISHED -j ACCEPT
This will allow the internet connection.
Set default chain policies
$ sudo iptables -P INPUT DROP
$ sudp iptables -P OUTPUT DROP
This will deny all kind of inbound/outbound traffic.
Allow your VPN connection
$ sudo iptables -A INPUT -s [VPN ip connection] -j ACCEPT
$ sudo iptables -A OUPUT -d [VPN ip connection] -j ACCEPT
This will allow the VPN connection.
IF YOU ARE CONNECTED BY SSH YOU MUST ALLOW YOUR IP ADDRESS ALSO AS YOUR LOCALHOST
UPDATE:
For other connections rules, just allow them.
HTTP for example:
$ sudo iptables -A INPUT -p tcp --dport 80 -j ACCEPT
$ sudo iptables -A OUTPUT -p tcp --dport 80 -j ACCEPT
PERSONAL RECOMMENDATION
What I do is to backup my iptables rules with $ sudo iptables-save > iptables_backup, then for any change I edit the rules with vim and restore the iptables with $ sudo iptables-restore < iptables_backup. This is only a personal practice to avoid duplicating rules.
Related videos on Youtube
boolean.is.null
Updated on September 18, 2022Comments
-
 boolean.is.null over 1 year
boolean.is.null over 1 yearI want to block all internet connections unless I'm connected to my OpenVPN. Now of course, I need to allow connection to the VPN server.
Can this be done, by allowing out/in traffic to/from the VPN server ip, but have a drop all rule afterwards with
iptables?I tried to solution proposed by @tachomi, but I don't have internet connection, when the
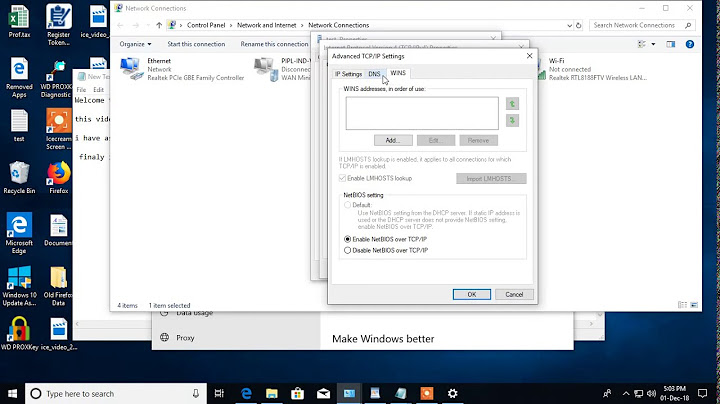
iptablesrules are set.iptables-savestates:# Generated by iptables-save v1.6.0 on Wed Feb 3 00:53:32 2016 *filter :INPUT DROP [247:40343] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [153:25961] -A INPUT -s 127.0.0.1/32 -p tcp -j ACCEPT -A INPUT -s 127.0.0.1/32 -p tcp -j ACCEPT -A INPUT -s 127.0.0.1/32 -p udp -j ACCEPT -A INPUT -s 127.0.0.1/32 -p udp -j ACCEPT -A INPUT -s <VPN_SERVER_IP>/32 -p tcp -j ACCEPT -A INPUT -s <VPN_SERVER_IP>/32 -p udp -j ACCEPT -A OUTPUT -d <VPN_SERVER_IP>/32 -p tcp -j ACCEPT -A OUTPUT -d <VPN_SERVER_IP>/32 -p udp -j ACCEPT COMMIT # Completed on Wed Feb 3 00:53:32 2016 -
Michael Mrozek over 8 yearsThis conversation has been moved to chat.
-
mpen over 3 yearsHow can we allow all SSH connections on the local network? And can
[VPN ip connection]be a hostname?