Can't access shared drive when connecting over VPN
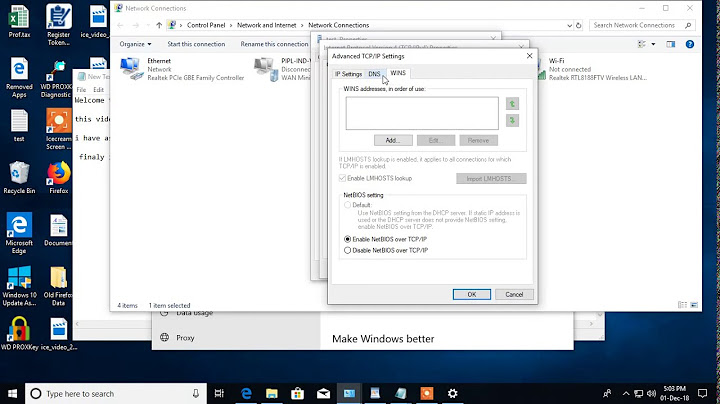
Try setting your VPN NIC as first priority in the network config.
http://theregime.wordpress.com/2008/03/04/how-to-setview-the-nic-bind-order-in-windows/
Related videos on Youtube
evolvd
Updated on September 18, 2022Comments
-
evolvd over 1 year
I can ping all network devices but it doesn't seem that DNS is resolving their hostnames.
ipconfig/ all is showing that I am pointing to the correct dns server.
I can "ping "dnsname"" and it will resolve but it wont resolve any other names.
Split tunnel is set up so outside DNS is resolving fineSo one issue might be DNS but I have the IP address of the server share so I figure I could just get to it that way. example: \10.0.0.1\ well I can't get to it that way either and I get "the specified network name is no longer available" I can ping it but I can't open the share.
Below is the ASA config :
ASA Version 8.2(1) ! hostname KG-ASA domain-name example.com names ! interface Vlan1 nameif inside security-level 100 ip address 10.0.0.253 255.255.255.0 ! interface Vlan2 nameif outside security-level 0 ip address dhcp setroute ! interface Ethernet0/0 switchport access vlan 2 ! interface Ethernet0/1 ! interface Ethernet0/2 ! interface Ethernet0/3 ! interface Ethernet0/4 ! interface Ethernet0/5 ! interface Ethernet0/6 ! interface Ethernet0/7 ! ftp mode passive clock timezone EST -5 clock summer-time EDT recurring dns domain-lookup outside dns server-group DefaultDNS name-server 10.0.0.101 domain-name blah.com access-list OUTSIDE_IN extended permit tcp any host 10.0.0.253 eq 10000 access-list OUTSIDE_IN extended permit tcp any host 10.0.0.253 eq 8333 access-list OUTSIDE_IN extended permit tcp any host 10.0.0.253 eq 902 access-list SPLIT-TUNNEL-VPN standard permit 10.0.0.0 255.0.0.0 access-list NONAT extended permit ip 10.0.0.0 255.255.255.0 10.0.1.0 255.255.255.0 pager lines 24 logging asdm informational mtu inside 1500 mtu outside 1500 ip local pool IPSECVPN-POOL 10.0.1.2-10.0.1.50 mask 255.255.255.0 icmp unreachable rate-limit 1 burst-size 1 asdm image disk0:/asdm-621.bin no asdm history enable arp timeout 14400 global (outside) 1 interface nat (inside) 0 access-list NONAT nat (inside) 1 0.0.0.0 0.0.0.0 static (inside,outside) tcp interface 10000 10.0.0.101 10000 netmask 255.255.255.255 static (inside,outside) tcp interface 8333 10.0.0.101 8333 netmask 255.255.255.255 static (inside,outside) tcp interface 902 10.0.0.101 902 netmask 255.255.255.255 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:01:00 dynamic-access-policy-record DfltAccessPolicy aaa authentication enable console LOCAL aaa authentication http console LOCAL aaa authentication serial console LOCAL aaa authentication ssh console LOCAL aaa authentication telnet console LOCAL http server enable http 10.0.0.0 255.255.0.0 inside http 0.0.0.0 0.0.0.0 outside no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart crypto ipsec transform-set myset esp-aes esp-sha-hmac crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac crypto ipsec security-association lifetime seconds 28800 crypto ipsec security-association lifetime kilobytes 4608000 crypto dynamic-map dynmap 1 set transform-set myset crypto dynamic-map dynmap 1 set reverse-route crypto map IPSEC-MAP 65535 ipsec-isakmp dynamic dynmap crypto map IPSEC-MAP interface outside crypto isakmp enable outside crypto isakmp policy 10 authentication pre-share encryption 3des hash sha group 2 lifetime 86400 crypto isakmp policy 65535 authentication pre-share encryption aes hash sha group 2 lifetime 86400 telnet 0.0.0.0 0.0.0.0 inside telnet timeout 5 ssh 0.0.0.0 0.0.0.0 inside ssh 70.60.228.0 255.255.255.0 outside ssh 74.102.150.0 255.255.254.0 outside ssh 74.122.164.0 255.255.252.0 outside ssh timeout 5 console timeout 0 dhcpd dns 10.0.0.101 dhcpd lease 7200 dhcpd domain blah.com ! dhcpd address 10.0.0.110-10.0.0.170 inside dhcpd enable inside ! threat-detection basic-threat threat-detection statistics access-list no threat-detection statistics tcp-intercept ntp server 63.111.165.21 webvpn enable outside svc image disk0:/anyconnect-win-2.4.1012-k9.pkg 1 svc enable group-policy EASYVPN internal group-policy EASYVPN attributes dns-server value 10.0.0.101 vpn-tunnel-protocol IPSec l2tp-ipsec svc webvpn split-tunnel-policy tunnelspecified split-tunnel-network-list value SPLIT-TUNNEL-VPN ! tunnel-group client type remote-access tunnel-group client general-attributes address-pool (inside) IPSECVPN-POOL address-pool IPSECVPN-POOL default-group-policy EASYVPN dhcp-server 10.0.0.253 tunnel-group client ipsec-attributes pre-shared-key * tunnel-group CLIENTVPN type ipsec-l2l tunnel-group CLIENTVPN ipsec-attributes pre-shared-key * ! class-map inspection_default match default-inspection-traffic ! ! policy-map global_policy class inspection_default inspect icmp ! service-policy global_policy global prompt hostname contextI'm not sure where I should go next with troubleshooting
nslookup result: Default Server: blahname.blah.lan Address: 10.0.0.101
-
Jason Axelson about 13 yearsSo does
ipconfig /allshow the VPN'd DNS or the general DNS? Also, what doesnslookup networkdevicenameshow? -
evolvd about 13 yearsipconfig/all shows VPN DNS under the cisco int and also my local dns under LAN int and nslookup shows the correct address. Is networkdevicename a linux command? I'm testing this on win 7.
-
Jason Axelson about 13 years@evolvd the
nslookup networkdevicenamewas meant to be all one command. So use nslookup to try to lookup the name of one of your network devices (you didn't give any examples). -
evolvd about 13 yearsnslookup brings up: Default Server: blah.blah.lan Address: 10.0.0.101 - so then I typed in sharename and I got this response *** sharename.blah.lan can't find sharename: Query refused
-
Holocryptic about 13 yearsAre you sure that folder is shared out? Can you access C$ on the server?
-
evolvd about 13 yearsat this point im not trying to get to a specific folder. If I was in this clients office I could type \\servername and the shares for the server would come up. I can't do that when I VPN in. I thought I could just \\server IP address and it would bypass the DNS issue but that wont work either... so there seems to be two problems.
-
Holocryptic about 13 yearsI was thinking about this some more, and should have said something sooner. Have you tried running wireshark?
-
evolvd about 13 yearsRun it where and look for what?
-
Holocryptic about 13 yearsRun it on your machine and attach to the VPN client NIC, and look for anything funky while trying to access the server.
-
evolvd about 13 yearsAnything funky..? So much data gets captured it would be helpful to know maybe some filters I could apply. I don't think this a vpn issue any more so I'm going to accept an answer and open a new question dealing with the fileshare. Thanks for the help.
-
C1sc0M4n over 11 yearsI was gonna say, your config looks good (EXCEPT TELNET! shame on you lol). What protocols have you thrown at your share to try and verify connectivity, i.e. ICMP, FTP, HTTP, EIEIO, etc.
-
-
evolvd about 13 yearsThe cisco vpn client is already top on the list
-
Holocryptic about 13 yearshmmm, sorry then. I knew the cisco clients used to have a problem with DNS that setting the binding order fixed. Can you access any share? Or other hosts via the hostname?
-
evolvd about 13 yearsThere is only this one share and I can't access it via IP or hostname. Thanks for sending the link though, at least I know about it.