CentOS 7 LDAP SSH Error "cannot find name for group ID"
make sure you ldap_search_base's value in sssd.conf contains your group dn.
Related videos on Youtube
Richard Wymarc
Updated on September 18, 2022Comments
-
Richard Wymarc almost 2 years
I'm running a CentOS 7 VirtualBox instance. I have LDAP authentication set up through our company Active Directory server.
Note: The AD server DOES NOT have Unix extensions installed.
What I'm seeing is this: When I log in via SSH I get an error:
$ ssh [email protected]@linuxboxip [email protected]@linuxboxip's password: /usr/bin/id: cannot find name for group ID 1316I can log in, and the error does not seem to cause a problem, but is annoying
group ID 1316 refers to the numberical ID assigned to my AD user:
$ getent passwd [email protected] [email protected]:*:1316:1316:First Last:/home/[email protected]:/bin/bashHowever:
$ getent group 1316returns nothing
If added manually, the error goes away:
sudo groupadd -g 1316 1316 sudo usermod -a -G 1316 1316There has to be a setting or process I'm missing that maps the generated Group IDs or creates the new groups, But I'm not finding it.
Thoughts?
Setup:
I'm running
CentOS 7-1611(64bit)fromosboxes.orgI have nss-pam-ldapd installed The nslcd and nscd services are set to run at startup
/etc/nsswitch.conf has been edited to add ldap:
passwd: files ldap sss shadow: files ldap sss group: files ldap sss hosts: files ldap dns myhostname bootparams: nisplus [NOTFOUND=return] files ldap ethers: files ldap netmasks: files ldap networks: files ldap protocols: files ldap rpc: files ldap services: files ldap sss netgroup: files ldap sss automount: files ldap sss aliases: files ldap nisplus/etc/pam.d/password-auth edited like so:
auth required pam_env.so auth sufficient pam_unix.so nullok try_first_pass auth sufficient pam_ldap.so minimum_uid=1000 use_first_pass auth requisite pam_succeed_if.so uid >= 1000 quiet_success auth required pam_deny.so account required pam_unix.so account sufficient pam_ldap.so minimum_uid=1000 account sufficient pam_localuser.so account sufficient pam_succeed_if.so uid < 1000 quiet account required pam_permit.so password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type= password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok password sufficient pam_ldap.so minimum_uid=1000 try_first_pass password required pam_deny.so session optional pam_keyinit.so revoke session required pam_limits.so -session optional pam_systemd.so session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid session required pam_unix.so session optional pam_ldap.so minimum_uid=1000 session required pam_mkhomedir.so skel=/etc/skel umask=0022/etc/pam.d/system-auth edited like so:
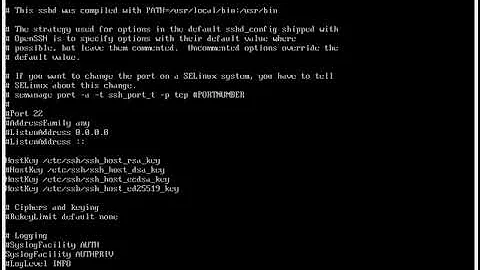
auth required pam_env.so auth sufficient pam_fprintd.so auth sufficient pam_unix.so nullok try_first_pass auth sufficient pam_ldap.so minimum_uid=1000 use_first_pass auth requisite pam_succeed_if.so uid >= 1000 quiet_success auth required pam_deny.so account required pam_unix.so account sufficient pam_ldap.so minimum_uid=1000 account sufficient pam_localuser.so account sufficient pam_succeed_if.so uid < 1000 quiet account required pam_permit.so password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type= password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok password sufficient pam_ldap.so minimum_uid=1000 try_first_pass password required pam_deny.so session optional pam_keyinit.so revoke session required pam_limits.so -session optional pam_systemd.so session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid session required pam_unix.so session optional pam_ldap.so minimum_uid=1000/etc/nslcd.conf edited:
uid nslcd gid nslcd uri ldap://myserver.com/ base dc=myserver,dc=com binddn CN=My Name,OU=Users,OU=DV,DC=myserver,DC=com bindpw PASSWORDHERE # Alternative mappings for Active Directory pagesize 1000 referrals off idle_timelimit 800 filter passwd (&(objectClass=user)(!(objectClass=computer))) map passwd uid userPrincipalName map passwd uidNumber objectSid:CorrectSID map passwd gidNumber objectSid:CorrectSID map passwd homeDirectory "/home/$userPrincipalName" map passwd gecos displayName map passwd loginShell "/bin/bash" filter group (objectClass=group) map group gidNumber objectSid:CorrectSID ssl no/etc/openldap/ldap.conf edited to add:
URI ldap://myserver.com/ BASE dc=myserver,dc=com