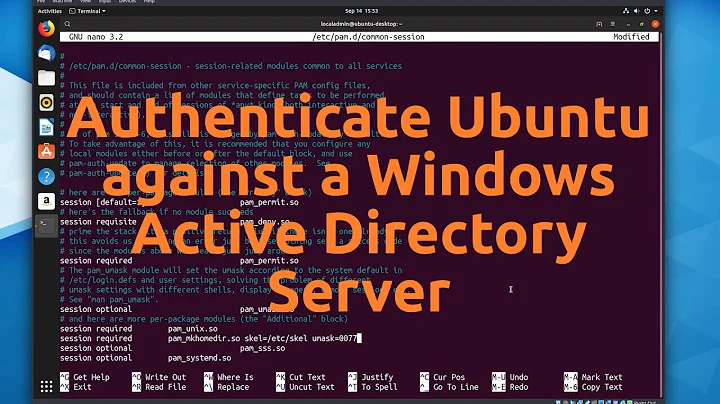
Change local password as root after configuring for MS-AD Kerberos+LDAP
Solution 1
In your /etc/pam.d/common-password , change the minimum_uid in your first line to something bigger than 1000, example:
password [success=3 default=ignore] pam_krb5.so minimum_uid=10000
That worked for me. This is what you should see in /var/log/auth.log after changing the password for that user as root:
Dec 26 12:34:36 3.8.0-29-generic passwd[22667]: pam_unix(passwd:chauthtok): password changed for service1
Solution 2
@Ameer's answer about editing common-password is correct. But: when you edit the uid limits of PAM in general, don't forget to edit all the affected PAM files! If you search for krb5 in /etc/pam.d, you should find all the relevant files:
root@server:/etc/pam.d# grep -R krb5 .
./common-auth:auth [success=2 default=ignore] pam_krb5.so minimum_uid=10000
./common-session-noninteractive:session optional pam_krb5.so minimum_uid=10000
./common-session:session optional pam_krb5.so minimum_uid=10000
./common-account:account required pam_krb5.so minimum_uid=10000
./common-password:password [success=2 default=ignore] pam_krb5.so minimum_uid=10000
If, for example, you've only edited common-auth, but not common-password, authentication works with local accounts, but passwd still asks for the current kerberos password! (Which is exactly the mistake that led me here.)
Solution 3
An indirect way to do it. Use mkpasswd to generate encrypted password:
mkpasswd --method=sha-512
Then use usermod to change the user's password:
usermod -p '<encrypted_password_from_mkpasswd>' <username>
Related videos on Youtube
Daniel C. Lopez
Updated on September 18, 2022Comments
-
Daniel C. Lopez almost 2 years
I have followed this excellent post to configure Kerberos + LDAP:
http://koo.fi/blog/2013/01/06/ubuntu-12-04-active-directory-authentication/However, there are some local users used for services.
When I try to change the password for one of those, as root, it asks forCurrent Kerberos passwordthen exits:passwd service1 Current Kerberos password: (I hit enter) Current Kerberos password: (I hit enter) passwd: Authentication token manipulation error passwd: password unchangedIf I switch to the local user and do
passwd, it asks once for Kerberos then falls back to local:
$ passwd
Current Kerberos password:
Changing password for service1.
(current) UNIX password:My configuration is similar to the site I posted above, and everything works fine, I just can't change the local users' passwords as root.
Thanks in advance for any help.
3.8.0-29-generic #42~precise1-UbuntuUpdate 1 2013-01-31:
# cat /etc/pam.d/common-auth auth [success=3 default=ignore] pam_krb5.so minimum_uid=1000 auth [success=2 default=ignore] pam_unix.so nullok_secure try_first_pass auth [success=1 default=ignore] pam_ldap.so use_first_pass auth requisite pam_deny.so auth required pam_permit.so auth optional pam_cap.so # cat /etc/pam.d/common-password password [success=3 default=ignore] pam_krb5.so minimum_uid=1000 password [success=2 default=ignore] pam_unix.so obscure use_authtok try_first_pass sha512 password [success=1 user_unknown=ignore default=die] pam_ldap.so use_authtok try_first_pass password requisite pam_deny.so password required pam_permit.so password optional pam_gnome_keyring.so-
 Fred the Magic Wonder Dog over 10 yearsWhat is the full path to your passwd command?
Fred the Magic Wonder Dog over 10 yearsWhat is the full path to your passwd command? -
Daniel C. Lopez over 10 years/usr/bin/passwd
-
 Fred the Magic Wonder Dog over 10 yearsThe next thing is to look at the pam config for passwd. What does /etc/pam.d/passwd look like?
Fred the Magic Wonder Dog over 10 yearsThe next thing is to look at the pam config for passwd. What does /etc/pam.d/passwd look like? -
Daniel C. Lopez over 10 years@include common-password
-
Daniel C. Lopez over 10 yearsFound something on the link below. Could something on common-auth be forcing Kerberos instead of allowing local? I'll post the contents. link
-
 Fred the Magic Wonder Dog over 10 yearsIt looks like pam_krb5 is not honoring the minumum_uid for password changes. Or else your local accounts have uid > 1000.
Fred the Magic Wonder Dog over 10 yearsIt looks like pam_krb5 is not honoring the minumum_uid for password changes. Or else your local accounts have uid > 1000. -
Daniel C. Lopez over 10 yearsFred, thank you so much for the help. The users were created without -u setting a lower UID. Cheers!
-
-
jhauris over 8 yearsThis is the correct answer. The line with pam_krb5.so should have minimum_uid of the starting uid of your kerberos users.