Check a range of IP addresses to see if a host is active
Solution 1
This should get you started.
#!/bin/bash
for i in `seq ${2} ${3}`
do
ping -c 1 ${1}.${i} > /dev/null 2>&1
if [ $? -eq 0 ]; then
echo "${1}.${i} responded."
else
echo "${1}.${i} did not respond."
fi
done
Sample output:
xxxx@xxxxxx:~$ bash test.sh 10.140.0 100 103
10.140.0.100 responded.
10.140.0.101 did not respond.
10.140.0.102 did not respond.
10.140.0.103 did not respond.
The bash manual can probably handle anything else you need.
Solution 2
Use nmap. It's the standard tool for the job.
Since you just want to know which hosts are online (and responding), run a “ping scan”: nmap -sP.
If you don't care about the formatting of the output, your script can be written this way:
#!/bin/sh
nmap -sP "$1.$2-$3"
Related videos on Youtube
Gilles 'SO- stop being evil'
Updated on September 18, 2022Comments
-
 Gilles 'SO- stop being evil' over 1 year
Gilles 'SO- stop being evil' over 1 yearI need to write a bash shell script that will check a range of IP addresses to see if a host is “alive” at that address.I also need to list the IP numbers of those that are “alive”, and provide a summary showing the number of “alive” and “not alive” IP addresses. The range of addresses will all be in a “Class C” network. I'm having problems figuring out how to pass through each arg and get it pinging each individual address within the range.
Below is a sample run of the script I intend to create.
$ programName 192.168.42 18 22 Checking: 192.168.42.18 19 20 21 22 Live hosts: 192.168.42.21 192.168.42.22 There were: 2 alive hosts 3 not alive hosts found through the use of 'ping'.-
 xrfang over 10 yearsNote that ping gives only the most rudimentary indication of 'aliveness'. Which is why things like Nagios exist, to allow you to check specific services or the running state on the machine. A ping check is a bit like checking a person is breathing; they could nevertheless be in a coma and not able to perform any function. It is entirely possible for a server to respond to pings and be otherwise totally unresponsive.
xrfang over 10 yearsNote that ping gives only the most rudimentary indication of 'aliveness'. Which is why things like Nagios exist, to allow you to check specific services or the running state on the machine. A ping check is a bit like checking a person is breathing; they could nevertheless be in a coma and not able to perform any function. It is entirely possible for a server to respond to pings and be otherwise totally unresponsive. -
Sean C. over 10 yearsUpvoting @Caleb for
nmap. If systems are filtering ICMP and not responding, you'd never know if there was a system at the address you're trying to ping. However, if you're on the same subnet, when you ping the address your system will also leverage ARP. This will cause it to cache the MAC address in the ARP table which is visible withip neigh show. So even if it doesn't respond to aping, you'll still know if something is there because you'll get it's MAC address in your ARP cache. -
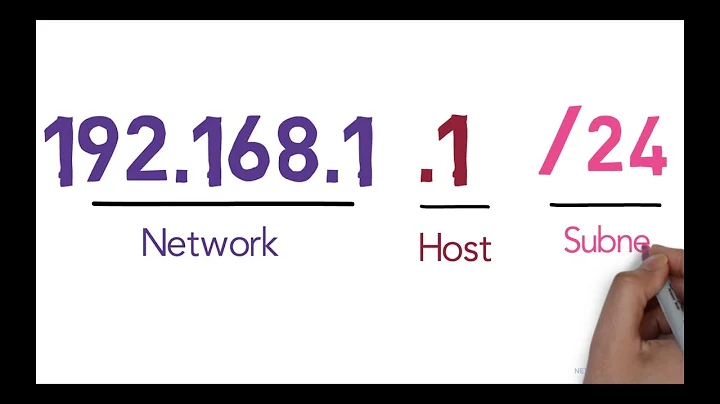
Jpark822 over 10 yearsJust to add a note: Your example seems to assume a /24 subnet (which used to be called class C, but in the last decades we changed to CIDR). Thus your example will not allow you to test a /25, a /23 or any other subnet which netmask is not a multiple of 8. That might suffice for you, but it really is something you need to be aware off.
-
-
Sean C. over 10 years@ChrisDown I'd love to concoct some great logic behind why I chose to evaluate the full path to the binary in a sub shell and start an enthusiastic discussion. I'd just be trolling at that point though. For now I'll just say that I threw that in there because I wanted the person asking the question, who obviously didn't even bother to look at any documentation, to question its function and maybe read a manual. I'll go ahead and remove the unnecessary sub shell for you.