Cisco ASA 5505 - NAT or Port Forward for SIP / VoIP ver 8.4
You don't have to explicitly forward RTP ports (>1024) as you have sip inspect turned on. When a SIP INVITE comes through, the router will open the appropriate RTP ports for the duration of the call.
As far as NATing SIP, you are missing the NAT command, and the access-list entry:
! this should be tightened to allow traffic only from your telephone company, or
! people with bad intent will happily place international calls on your account
access-list outside_access_in extended permit udp any host 192.168.3.150 eq 5060
! nat 5060 to 5060
object network NEC_DSX
nat (inside,outside) static interface service udp 5060 5060
Though it is not needed, the proper syntax to forward a range is:
object service rtp-1024-1215
service udp source range 1024 1215
object network NEC_DSX_RTP
host 192.168.3.150
nat (inside,outside) static interface service rtp-1024-1215 rtp-1024-1215
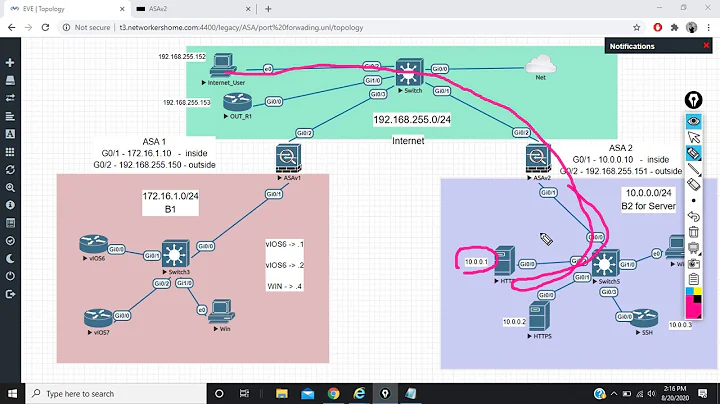
Related videos on Youtube
user72593
Updated on September 18, 2022Comments
-
user72593 over 1 year
I just had an NEC PBX installed that lets me use SIP trunks for VoIP services, My gateway is a Cisco ASA 5505 running 8.4 and I only have one public/static IP Addresses.
So far, my trunks are registering and I can make outgoing calls and everything works, but incoming calls are silent (both ways). I'm assuming its because the UDP ports 1024-1215 are not forwarded and neither is SIP (5060).
What I need to do is forward the UDP port range of 1024-1215, however it seems I can't create a port map for UDP, or define a range of ports for UDP in a static Route. Any help in the right direction would be appreciated !!! (I was told ASA 8.4 would allow forwarding of a range of ports so I upgraded and now I'm a bit lost with the new commands)
Using the ASDM I gave it a few tries but here were my results:
[OK] object network NEC_DSX object network NEC_DSX [ERROR] nat (inside,outside) static interface service udp 1024-1215 1024-1215 nat (inside,outside) static interface service udp 1024-1215 1024-1215 ^ ERROR: % Invalid input detected at '^' marker. I also tried: [OK] object network NEC_DSX object network NEC_DSX [ERROR] nat (inside,outside) static interface service udp 1024 1024 NAT unable to reserve ports. ------------------------ Here is my current config : ASA Version 8.4(4) ! hostname ciscoasa enable password 8Ry2YjIyt7RRXU24 encrypted passwd 2KFQnbNIdI.2KYOU encrypted names name 24.173.xxx.xxx StaticOutside description WAN IP ! interface Ethernet0/0 switchport access vlan 2 ! interface Ethernet0/1 ! interface Ethernet0/2 ! interface Ethernet0/3 ! interface Ethernet0/4 ! interface Ethernet0/5 ! interface Ethernet0/6 ! interface Ethernet0/7 ! interface Vlan1 nameif inside security-level 100 ip address 192.168.3.1 255.255.255.0 ! interface Vlan2 nameif outside security-level 0 ip address StaticOutside 255.255.255.252 ! boot system disk0:/asa844-k8.bin boot system disk0:/asa832-k8.bin ftp mode passive object network obj-192.168.3.5 host 192.168.3.5 object network obj_any subnet 0.0.0.0 0.0.0.0 object network NEC_DSX host 192.168.3.150 description NEC DSX SYSTEM access-list outside_access_in extended permit tcp any host 192.168.3.5 eq 3389 log disable pager lines 24 logging asdm informational mtu inside 1500 mtu outside 1500 icmp unreachable rate-limit 1 burst-size 1 asdm image disk0:/asdm-649-103.bin no asdm history enable arp timeout 14400 ! object network obj-192.168.3.5 nat (inside,outside) static interface service tcp 3389 3389 object network obj_any nat (inside,outside) dynamic interface access-group outside_access_in in interface outside route outside 0.0.0.0 0.0.0.0 24.173.100.85 1 timeout xlate 3:00:00 timeout pat-xlate 0:00:30 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute timeout tcp-proxy-reassembly 0:01:00 timeout floating-conn 0:00:00 dynamic-access-policy-record DfltAccessPolicy user-identity default-domain LOCAL http server enable http 192.168.3.0 255.255.255.0 inside no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5 ssh timeout 5 ssh key-exchange group dh-group1-sha1 console timeout 0 dhcpd auto_config outside ! dhcpd address 192.168.3.10-192.168.3.38 inside dhcpd dns 4.2.2.1 4.2.2.2 interface inside dhcpd enable inside ! threat-detection basic-threat threat-detection statistics host threat-detection statistics access-list no threat-detection statistics tcp-intercept webvpn ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map parameters message-length maximum client auto message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect ip-options class class-default user-statistics accounting ! service-policy global_policy global prompt hostname context no call-home reporting anonymous Cryptochecksum:85d3bff9e7eb561bf8ee4f27b11a6cf4 : end -
user72593 over 10 yearsI see, the RTP being controlled by sip inspect does make sense. The nat however, still doesn't seem to work. Result of the command: "nat (inside,outside) static interface service udp 5060 5060" ERROR: NAT unable to reserve ports.
-
user72593 over 10 yearsWell I went ahead and ran your commands. I think something did get stuck in there, so I did a "clean xlate" and then I WAS able to run the command. Still one-sided audio. Then I went in and added TCP port 5060 into the NAT as well. I also tried to forward the range of ports like you displayed but it didn't like your command so I forwarded a dozen ports from 1024+. Eventually I did a "clear local" and then when I ran "show sip" it started showing me counters and traffic. So it looks like I've got two-way audio now ! Thanks for the help Mitch !