Debian eth0 to wlan0 forwarding, with openvpn
I had the same problem setting up openvpn over wifi on my raspberrypi. It turned out, that the flaw was wpa-roam.
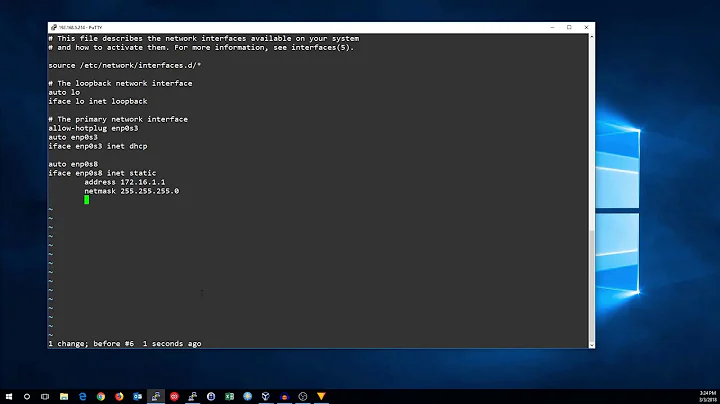
The wlan0 section in /etc/network/interfaces had to be changed to:
allow-hotplug wlan0
iface wlan0 inet dhcp
wpa-conf /etc/wpa_supplicant/wpa_supplicant.conf
The important part was replacing wpa-roam by wpa-conf.
Background
In my /var/log/daemon.log I found the following entry after enabling openvpn:
Jan 13 22:40:19 raspberrypi ifplugd(tun0)[28971]: Executing '/etc/ifplugd/ifplugd.action tun0 up'.
which was followd by
Jan 13 22:40:19 raspberrypi wpa_supplicant[3177]: wlan0: CTRL-EVENT-DISCONNECTED bssid=00:00:00:00:00:00 reason=0
...
Jan 13 22:40:20 raspberrypi ifplugd(wlan0)[3108]: Link beat lost.
...
Jan 13 22:40:30 raspberrypi ifplugd(wlan0)[3108]: Executing '/etc/ifplugd/ifplugd.action wlan0 down'.
Jan 13 22:40:30 raspberrypi ifplugd(wlan0)[3108]: client: /sbin/ifdown: interface wlan0 not configured
Jan 13 22:40:30 raspberrypi ifplugd(wlan0)[3108]: Program executed successfully.
So it had to be somewhat related to the creation of the new network device.
Analyzing /etc/ifplugd/ifplugd.action tun0 up returned, that
/etc/ifplugd/action.d/action_wpa is executed.
/etc/ifplugd/action.d/action_wpa
#!/bin/sh
# Action script to enable/disable wpa-roam interfaces in reaction to
# ifplugd events.
#
# Copyright: Copyright (c) 2008-2010, Kel Modderman <[email protected]>
# License: GPL-2
#
PATH=/sbin:/usr/sbin:/bin:/usr/bin
if [ ! -x /sbin/wpa_action ]; then
exit 0
fi
# ifplugd(8) - <iface> <action>
#
# If an ifplugd managed interface is brought up, disconnect any
# wpa-roam managed interfaces so that only one "roaming" interface
# remains active on the system.
IFPLUGD_IFACE="${1}"
case "${2}" in
up)
COMMAND=disconnect
;;
down)
COMMAND=reconnect
;;
*)
echo "$0: unknown arguments: ${@}" >&2
exit 1
;;
esac
for CTRL in /var/run/wpa_supplicant/*; do
[ -S "${CTRL}" ] || continue
IFACE="${CTRL#/var/run/wpa_supplicant/}"
# skip if ifplugd is managing this interface
if [ "${IFPLUGD_IFACE}" = "${IFACE}" ]; then
continue
fi
if wpa_action "${IFACE}" check; then
wpa_cli -i "${IFACE}" "${COMMAND}"
fi
done
So in order to save maybe roaming-costs all roaming devices are deactivated, if an other network device is available. May it be a real device or just virtual.
I only had access to the pi over ssh over wifi. Killed remotely and had to wait to come back home for hard reboot ;-)
Possible other way
An other way could be, to configure the tun0 device in /etc/network/interfaces so that it doesn't call /etc/ifplugd/action.d/action_wpa. That way roaming would still work.
Related videos on Youtube
Sameer Dhar
Updated on September 18, 2022Comments
-
Sameer Dhar over 1 year
I'm using "raspian" (Debian for the raspberry pi), and would like the raspberry-pi to serve internet access through eth0, using wlan0. The catch here is that while wlan0 is connected to my router, I'd like it to route the traffic through an openvpn network.
Might be difficult to understand, so here's a diagram:PC connected to ethernet port of raspberry pi --> [eth0 on raspberry pi -> through openvpn tunnel using wlan0] --> my router --> openvpn server --> internet
The bridge(?) is done through this:
echo 1 > /proc/sys/net/ipv4/ip_forward
iptables -A FORWARD --in-interface eth0 -j ACCEPT
iptables --table nat -A POSTROUTING --out-interface wlan0 -j MASQUERADEThe only problem I have now is that the wlan interface goes down when I start the openvpn service? Of course, openvpn looses connection after this also, since there is no internet connection anymore. I then try using "wpa_cli reconnect" to re-enable the wlan interface, but then I get "TLS Error: local/remote TLS keys are out of sync: [AF_INET]$MY_OPENVPN_SERVER_IP:1194 [0]"
(Note, that the openvpn connection was established previously, so it's not a clock issue, I believe?)Maybe relevant config files:
/etc/openvpn/client.conf
client dev tun proto udpremote $MY_OPENVPN_SERVER_IP resolv-retry infinite persist-key persist-tun ca ca.crt cert raspberry.crt key raspberry.key comp-lzo keepalive 10 60 verb 3/etc/dhcp/dhcpd.conf
# The ddns-updates-style parameter controls whether or not the server will # attempt to do a DNS update when a lease is confirmed. We default to the # behavior of the version 2 packages ('none', since DHCP v2 didn't # have support for DDNS.) ddns-update-style none; # option definitions common to all supported networks... option domain-name "example.org"; option domain-name-servers ns1.example.org, ns2.example.org; default-lease-time 600; max-lease-time 7200; log-facility local7; subnet 10.42.0.0 netmask 255.255.255.0 { range 10.42.0.10 10.42.0.100; option domain-name-servers 8.8.8.8; option domain-name "internal.raspi.org"; option routers 10.42.0.2; option broadcast-address 10.42.0.255; default-lease-time 600; max-lease-time 7200; }/etc/network/interfaces
auto lo iface lo inet loopback #iface eth0 inet dhcp allow-hotplug wlan0 iface wlan0 inet manual wpa-roam /etc/wpa_supplicant/wpa_supplicant.conf iface default inet dhcp auto eth0 iface eth0 inet static address 10.42.0.2 netmask 255.255.255.0 broadcast 10.42.0.255ifconfig output before openvpn is enabled:
eth0 Link encap:Ethernet HWaddr b8:27:eb:ea:ea:45 inet addr:10.42.0.2 Bcast:10.42.0.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:14955 errors:0 dropped:0 overruns:0 frame:0 TX packets:22413 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:3217763 (3.0 MiB) TX bytes:28150535 (26.8 MiB) lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:8 errors:0 dropped:0 overruns:0 frame:0 TX packets:8 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:1104 (1.0 KiB) TX bytes:1104 (1.0 KiB) wlan0 Link encap:Ethernet HWaddr b0:48:7a:91:ca:2c inet addr:192.168.2.110 Bcast:192.168.2.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:23742 errors:0 dropped:0 overruns:0 frame:0 TX packets:14611 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:28174574 (26.8 MiB) TX bytes:3627713 (3.4 MiB)ifconfig output after openvpn is enabled:
eth0 Link encap:Ethernet HWaddr b8:27:eb:ea:ea:45 inet addr:10.42.0.2 Bcast:10.42.0.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:15144 errors:0 dropped:0 overruns:0 frame:0 TX packets:22580 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:3234735 (3.0 MiB) TX bytes:28178133 (26.8 MiB) lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:8 errors:0 dropped:0 overruns:0 frame:0 TX packets:8 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:1104 (1.0 KiB) TX bytes:1104 (1.0 KiB) tun0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 inet addr:10.8.0.22 P-t-P:10.8.0.21 Mask:255.255.255.255 UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:1356 errors:0 dropped:84 overruns:0 carrier:0 collisions:0 txqueuelen:100 RX bytes:0 (0.0 B) TX bytes:894869 (873.8 KiB) wlan0 Link encap:Ethernet HWaddr b0:48:7a:91:ca:2c UP BROADCAST MULTICAST MTU:1500 Metric:1 RX packets:23950 errors:0 dropped:0 overruns:0 frame:0 TX packets:14759 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:28204123 (26.8 MiB) TX bytes:3648458 (3.4 MiB)syslog, shortly after enabling openvpn:
Dec 1 17:21:23 raspberrypi ovpn-client[2301]: OpenVPN 2.2.1 arm-linux-gnueabihf [SSL] [LZO2] [EPOLL] [PKCS11] [eurephia] [MH] [PF_INET6] [IPv6 payload 20110424-2 (2.2RC2)] built on Apr 28 2012 Dec 1 17:21:23 raspberrypi ovpn-client[2301]: IMPORTANT: OpenVPN's default port number is now 1194, based on an official port number assignment by IANA. OpenVPN 2.0-beta16 and earlier used 5000 as the default port. Dec 1 17:21:23 raspberrypi ovpn-client[2301]: WARNING: No server certificate verification method has been enabled. See http://openvpn.net/howto.html#mitm for more info. Dec 1 17:21:23 raspberrypi ovpn-client[2301]: NOTE: OpenVPN 2.1 requires '--script-security 2' or higher to call user-defined scripts or executables Dec 1 17:21:23 raspberrypi ovpn-client[2301]: LZO compression initialized Dec 1 17:21:23 raspberrypi ovpn-client[2301]: Control Channel MTU parms [ L:1542 D:138 EF:38 EB:0 ET:0 EL:0 ] Dec 1 17:21:23 raspberrypi ovpn-client[2301]: Socket Buffers: R=[163840->131072] S=[163840->131072] Dec 1 17:21:23 raspberrypi ovpn-client[2301]: Data Channel MTU parms [ L:1542 D:1450 EF:42 EB:135 ET:0 EL:0 AF:3/1 ] Dec 1 17:21:23 raspberrypi ovpn-client[2301]: Local Options hash (VER=V4): '41690919' Dec 1 17:21:23 raspberrypi ovpn-client[2301]: Expected Remote Options hash (VER=V4): '530fdded' Dec 1 17:21:23 raspberrypi ovpn-client[2302]: UDPv4 link local (bound): [undef] Dec 1 17:21:23 raspberrypi ovpn-client[2302]: UDPv4 link remote: [AF_INET]$MY_OPENVPN_SERVER_IP:1194 Dec 1 17:21:23 raspberrypi ovpn-client[2302]: TLS: Initial packet from [AF_INET]$MY_OPENVPN_SERVER_IP:1194, sid=28e45b1e 0782389c Dec 1 17:21:24 raspberrypi ovpn-client[2302]: VERIFY OK: depth=1, /C=US/ST=SECRET/L=Evilston/O=SecretLair/CN=SecretLair_CA/emailAddress=compendium@starstrider Dec 1 17:21:24 raspberrypi ovpn-client[2302]: VERIFY OK: depth=0, /C=US/ST=SECRET/L=Evilston/O=SecretLair/CN=server/emailAddress=compendium@starstrider Dec 1 17:21:26 raspberrypi ovpn-client[2302]: Data Channel Encrypt: Cipher 'BF-CBC' initialized with 128 bit key Dec 1 17:21:26 raspberrypi ovpn-client[2302]: Data Channel Encrypt: Using 160 bit message hash 'SHA1' for HMAC authentication Dec 1 17:21:26 raspberrypi ovpn-client[2302]: Data Channel Decrypt: Cipher 'BF-CBC' initialized with 128 bit key Dec 1 17:21:26 raspberrypi ovpn-client[2302]: Data Channel Decrypt: Using 160 bit message hash 'SHA1' for HMAC authentication Dec 1 17:21:26 raspberrypi ovpn-client[2302]: Control Channel: TLSv1, cipher TLSv1/SSLv3 DHE-RSA-AES256-SHA, 1024 bit RSA Dec 1 17:21:26 raspberrypi ovpn-client[2302]: [server] Peer Connection Initiated with [AF_INET]$MY_OPENVPN_SERVER_IP:1194 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: SENT CONTROL [server]: 'PUSH_REQUEST' (status=1) Dec 1 17:21:28 raspberrypi ovpn-client[2302]: PUSH: Received control message: 'PUSH_REPLY,redirect-gateway def1,dhcp-option DNS 8.8.8.8,dhcp-option DNS 4.2.2.4,route 10.8.0.1,topology net30,ping 10,ping-restart 120,ifconfig 10.8.0.22 10.8.0.21' Dec 1 17:21:28 raspberrypi ovpn-client[2302]: OPTIONS IMPORT: timers and/or timeouts modified Dec 1 17:21:28 raspberrypi ovpn-client[2302]: OPTIONS IMPORT: --ifconfig/up options modified Dec 1 17:21:28 raspberrypi ovpn-client[2302]: OPTIONS IMPORT: route options modified Dec 1 17:21:28 raspberrypi ovpn-client[2302]: OPTIONS IMPORT: --ip-win32 and/or --dhcp-option options modified Dec 1 17:21:28 raspberrypi ovpn-client[2302]: ROUTE default_gateway=192.168.2.1 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: TUN/TAP device tun0 opened Dec 1 17:21:28 raspberrypi kernel: [ 1305.253893] tun: Universal TUN/TAP device driver, 1.6 Dec 1 17:21:28 raspberrypi kernel: [ 1305.253924] tun: (C) 1999-2004 Max Krasnyansky <[email protected]> Dec 1 17:21:28 raspberrypi ovpn-client[2302]: TUN/TAP TX queue length set to 100 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: do_ifconfig, tt->ipv6=0, tt->did_ifconfig_ipv6_setup=0 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: /sbin/ifconfig tun0 10.8.0.22 pointopoint 10.8.0.21 mtu 1500 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: /sbin/route add -net $MY_OPENVPN_SERVER_IP netmask 255.255.255.255 gw 192.168.2.1 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: /sbin/route add -net 0.0.0.0 netmask 128.0.0.0 gw 10.8.0.21 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: /sbin/route add -net 128.0.0.0 netmask 128.0.0.0 gw 10.8.0.21 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: /sbin/route add -net 10.8.0.1 netmask 255.255.255.255 gw 10.8.0.21 Dec 1 17:21:28 raspberrypi ovpn-client[2302]: Initialization Sequence Completed Dec 1 17:21:28 raspberrypi ifplugd(tun0)[2342]: ifplugd 0.28 initializing. Dec 1 17:21:28 raspberrypi ifplugd(tun0)[2342]: Using interface tun0/00:00:00:00:00:00 with driver <tun> (version: 1.6) Dec 1 17:21:28 raspberrypi ifplugd(tun0)[2342]: Using detection mode: SIOCETHTOOL Dec 1 17:21:28 raspberrypi ifplugd(tun0)[2342]: Initialization complete, link beat detected. Dec 1 17:21:28 raspberrypi ifplugd(tun0)[2342]: Executing '/etc/ifplugd/ifplugd.action tun0 up'. Dec 1 17:21:29 raspberrypi kernel: [ 1305.603457] wlan0: deauthenticating from 88:25:2c:32:a1:10 by local choice (reason=3) Dec 1 17:21:29 raspberrypi kernel: [ 1305.694379] cfg80211: Calling CRDA for country: CN Dec 1 17:21:29 raspberrypi ifplugd(wlan0)[1449]: Link beat lost. Dec 1 17:21:29 raspberrypi ifplugd(tun0)[2342]: client: OK Dec 1 17:21:29 raspberrypi wpa_supplicant[1532]: wlan0: CTRL-EVENT-DISCONNECTED bssid=00:00:00:00:00:00 reason=3 Dec 1 17:21:29 raspberrypi ifplugd(tun0)[2342]: client: Ignoring unknown interface tun0=tun0. Dec 1 17:21:29 raspberrypi wpa_action: WPA_IFACE=wlan0 WPA_ACTION=DISCONNECTED Dec 1 17:21:29 raspberrypi wpa_action: WPA_ID=0 WPA_ID_STR= WPA_CTRL_DIR=/var/run/wpa_supplicant Dec 1 17:21:29 raspberrypi wpa_action: ifdown wlan0 Dec 1 17:21:29 raspberrypi ifplugd(tun0)[2342]: Program executed successfully. Dec 1 17:21:29 raspberrypi dhclient: Internet Systems Consortium DHCP Client 4.2.2 Dec 1 17:21:29 raspberrypi dhclient: Copyright 2004-2011 Internet Systems Consortium. Dec 1 17:21:29 raspberrypi dhclient: All rights reserved. Dec 1 17:21:29 raspberrypi dhclient: For info, please visit https://www.isc.org/software/dhcp/ Dec 1 17:21:29 raspberrypi dhclient: Dec 1 17:21:29 raspberrypi dhclient: Listening on LPF/wlan0/b0:48:7a:91:ca:2c Dec 1 17:21:29 raspberrypi dhclient: Sending on LPF/wlan0/b0:48:7a:91:ca:2c Dec 1 17:21:29 raspberrypi dhclient: Sending on Socket/fallback Dec 1 17:21:29 raspberrypi dhclient: DHCPRELEASE on wlan0 to 192.168.2.1 port 67 Dec 1 17:21:29 raspberrypi wpa_action: removing sendsigs omission pidfile: /run/sendsigs.omit.d/wpasupplicant.wpa_supplicant.wlan0.pid Dec 1 17:21:31 raspberrypi ntpd[1924]: Listen normally on 4 tun0 10.8.0.22 UDP 123 Dec 1 17:21:31 raspberrypi ntpd[1924]: Deleting interface #3 wlan0, 192.168.2.110#123, interface stats: received=54, sent=54, dropped=0, active_time=1279 secs Dec 1 17:21:31 raspberrypi ntpd[1924]: 178.63.212.146 interface 192.168.2.110 -> (none) Dec 1 17:21:31 raspberrypi ntpd[1924]: 85.214.240.100 interface 192.168.2.110 -> (none) Dec 1 17:21:31 raspberrypi ntpd[1924]: 195.71.86.233 interface 10.42.0.2 -> 10.8.0.22 Dec 1 17:21:31 raspberrypi ntpd[1924]: 212.85.158.10 interface 10.42.0.2 -> 10.8.0.22 Dec 1 17:21:31 raspberrypi ntpd[1924]: peers refreshed Dec 1 17:21:39 raspberrypi ifplugd(wlan0)[1449]: Executing '/etc/ifplugd/ifplugd.action wlan0 down'. Dec 1 17:21:39 raspberrypi ifplugd(wlan0)[1449]: client: /sbin/ifdown: interface wlan0 not configured Dec 1 17:21:39 raspberrypi ifplugd(wlan0)[1449]: Program executed successfully. -
Sameer Dhar over 11 yearsThanks you so much for the solution, and the awesome explanation!