Disable password complexity check (PAM)
Solution 1
I found out my system (as most modern Linux) use PAM (Pluggable Authentication Modules) and pam_cracklib module within it. pam_cracklib enforces minimum length of 6 symbols regardless of parameters, so solution is to turn it off.
One link I've read discussed editing password-ac and system-ac files in /etc/pam.d, the contents of both files were same and no explanation was given of their respective roles.
Upon study of PAM docs (The Linux-PAM System Administrators' Guide | linux-pam.org), I learned PAM configs for LINUX services are in that /etc/pam.d directory in separate files. I saw passwd file and it in found only system-ac file mentioned (added by substack keyword), so on my system I needed to edit only system-ac.
Making pam_cracklib optional made no difference (I guess that's because pam_cracklib did not pass entered and rejected pasword to next module in stack - pam_unix) and commenting line with pam_cracklib lead to errors during passwd run. I noted that next line with ordinary pam_unix had option use_authtok (docs: enforce the module to set the new password to the one provided by a previously stacked module). After I deleted that option and commented line with pam_cracklib I now able to set short passwords with passwd.
Solution 2
There are a couple of PAM modules that can do password strength checking. There's at least pam_cracklib that comes with many distributions, and pam_passwdqc from Openwall (packaged in e.g. Debian). Also, some versions of the usual file-based authentication module pam_unix have options that are related to password strength, like minlen for minimum password length, and obscure which makes some tests to compare the new password to the old one. (The name comes from 'the "obscure" checks in the original shadow package'.)
You'll need to check your PAM config for any such modules, and either disable or uninstall them. Look for lines starting with the keyword password for the modules related to password changes. The exact structure of the the configuration may depend on the distribution.
Also, if you have users stored on LDAP or other such network based system, it's not impossible for the server itself to have requirements for the user password. In this case, the PAM configuration on the client would not be relevant. E.g. OpenLDAP has a password policy overlay module.
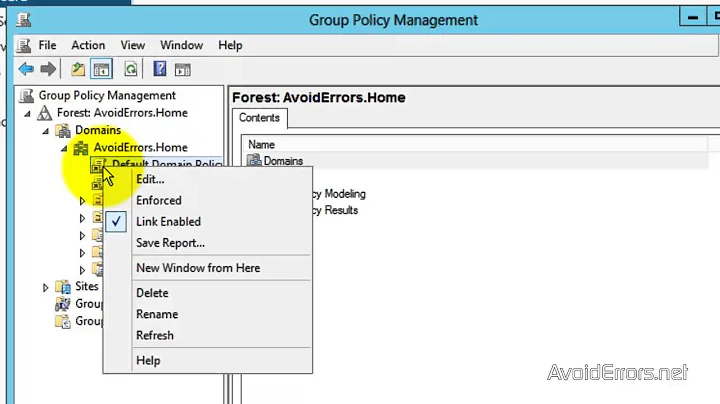
Related videos on Youtube
Alexei Martianov
Updated on September 18, 2022Comments
-
Alexei Martianov over 1 year
I installed a Linux based system with a blank password. I wanted to change password to something simple, but using
passwdand setting the password to something like a single symbol gave an error of “password being a palindrome”.How to disable password complexity checks?
-
 jesse_b over 6 yearsI like this question and your answer, and do not feel they are duplicates as the question is more generic and the answer is detailed. However, I feel I should link two other relevant posts in case someone is looking to bypass without completely disabling: unix.stackexchange.com/questions/324073/… unix.stackexchange.com/questions/139290/…
jesse_b over 6 yearsI like this question and your answer, and do not feel they are duplicates as the question is more generic and the answer is detailed. However, I feel I should link two other relevant posts in case someone is looking to bypass without completely disabling: unix.stackexchange.com/questions/324073/… unix.stackexchange.com/questions/139290/… -
Alexei Martianov over 6 years@Jesse_b Thank you! I did not know about bypass before.
-



![Remove Password Complexity Requirements In Windows 10 Pro [Solution]](https://i.ytimg.com/vi/YSguTPtiWx4/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLA_M13iF-zhIbGxKzewhNjXVhFFmg)