Disable sudo permission to user from command line
Solution 1
The user in question has sudo privileges because it is in the admin group. As wojox commented, you could use visudo and remove sudo privileges from the admin group, but that would remove sudo capabilities from all members of the admin group not just the one user.
Alternatively, you can remove the user from the admin group. If screen oriented vi is considered command line enough, run vigr and delete the username from the appropriate line.
For a "pure" command line solution, try gpasswd, as it administers /etc/group and can add and delete users from groups.
root@toki:~# id -Gn username
username adm dialout cdrom plugdev lpadmin admin sambashare
# ^- the group to remove
root@toki:~# gpasswd -d username admin
Removing user username from group admin
root@toki:~# id -Gn username
username adm dialout cdrom plugdev lpadmin sambashare
# ^- username not a member
root@toki:~# gpasswd -a username admin
Adding user username to group admin
root@toki:~# id -Gn username
username adm dialout cdrom plugdev lpadmin admin sambashare
Below is my first answer before I realized there was a less dumb way to do it.
If you'd like a more complicated way to do this, you can use usermod.
Here's a quote from the usermod man page:
-G, --groups GROUP1[,GROUP2,...[,GROUPN]]]
A list of supplementary groups which the user is also a member of.
Each group is separated from the next by a comma, with no intervening
whitespace. The groups are subject to the same restrictions as the
group given with the -g option.
If the user is currently a member of a group which is not listed, the
user will be removed from the group. This behaviour can be changed via
the -a option, which appends the user to the current supplementary group
list.
So you have to specify all the groups for the user except for admin.
root@toki:~# id username
uid=1000(username) gid=1000(username) groups=1000(username),4(adm),20(dialout),24(cdrom),46(plugdev),111(lpadmin),119(admin),122(sambashare)
root@toki:~# usermod -G 4,20,24,46,111,122 username
root@toki:~# id username
uid=1000(username) gid=1000(username) groups=1000(username),4(adm),20(dialout),24(cdrom),46(plugdev),111(lpadmin),122(sambashare)
Finally, it violates the spirit of the question, but one could type users-admin from the command line to modify users and groups.
Solution 2
Whatever wisdom may be found in the above answers, I've solved the issue of enabling the root account and disabling sudo for a specified user as follows.
First enable the root account:
$ sudo passwd root
More information in the Ubuntu Documentation.
Then:
- become root
- backup and then edit /etc/group
- become user again to test the changes
That is:
$ su
# cp /etc/group /etc/group.bak
# nano /etc/group # find a line like 'sudo:x:27:guest', remove the
# user name (i.c. 'guest') and save the file
# exit,
$ [try any sudo command]
The user 'guest' is now removed from the sudoers file. If all went well any sudo command should return a message the like of this:
guest is not in the sudoers file. This incident will be reported.
A guest logging in on this computer can no longer accidentally or willingly mess with the system, since you need to be root to do so. Of course, if you add a new user, you will need to repeat the editing of /etc/group.
Cheers!
-- linuxrev
(Ubuntu 12.04)
Solution 3
Warning
Carefull, you can lock yourself out of our system this way! Always make sure, that the root-user retains his rights and you can access it. Keep a root terminal open beforehand so you can undo changes. Test settings in another terminal before closing your root-terminal!
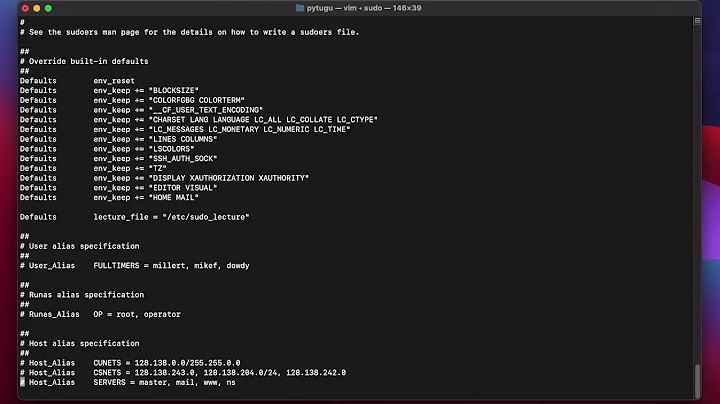
soduers
As described in another answer. Edit /etc/sudoers by invoking visudo in shell:
sudo select-editor # this is optional. it will allow you to select your default editor in shell
sudo visudo
Then change the line that says something similar to this:
# Members of the admin group may gain root privileges
%admin ALL=(ALL) ALL
to this:
# root may gain root privileges
root ALL=(ALL) ALL
Or delete the line, if you're sure, your root user account is enabled.
group
The default user is member of the 'admin' group. If you preferre it, you could just as well revoke the users membership to that group. Do that by following my last link or remove his name from the line admin:x:120:defaultuser in /etc/group file:
cp -n /etc/group /etc/group.bak && \
sed -i 's/\(admin:x.*\)defaultuser\(.*\)/\1\2/g' /etc/group
Related videos on Youtube
sagarchalise
extensive Linux user with python programming and enthusiasm about everything computing.
Updated on September 18, 2022Comments
-
 sagarchalise over 1 year
sagarchalise over 1 yearI have activated root user in ubuntu and want to use ubuntu as server with no DE. For this I want to disable sudo privilege given to first user. How can I do this from command line ? I know I can use a GUI but how to do it from command line ?
-
wojox almost 13 yearsDepending on how you set up your groups, type in visudo
-
-
con-f-use almost 13 years@psusi : No, youre WRONG. He CAN delete it. As he said "I have activated root user in ubuntu" meaning, he can ALWAYS LOGIN AS ROOT USER TO GAIN ACCESS. Please correct your downvote of my post.