Failed Authentication Against Windows Server 2012 R2 RADIUS Using PAP
For anybody who stumbles on this and for which this may be helpful...
It turns out the problem was in my network policy. An optional part of creating a network policy is, on the "Conditions" tab, creating a "Client Friendly Name" that matches a RADIUS client you've set up (which, along with the network policy, is also done under "Network Policy Service"). You are allowed to use wildcard characters so that a "Client Friendly Name" can be made to match several RADIUS clients.
However, it seems you can use the wildcard character "*" only at the end of the "Client Friendly Name".
As an example, assume I have two RADIUS clients set up: Dave-Desktop-Home and Dave-Laptop-Home. If in my network policy I specify a "Client Friendly Name" of "Dave-*-Home", Windows Server 2012 will create an event log saying I successfully authenticated but will actually send me a RADIUS access-reject message.
On the other hand, specifying a "Client Friendly Name" of "Dave-*" works just fine to match both RADIUS clients. Both can perform a successful RADIUS authentication.
Related videos on Youtube
Dave
Updated on September 18, 2022Comments
-
Dave over 1 year
I am trying (unsuccessfully) to remotely authenticate onto a Linux-based network switch against Windows Server 2012 R2 RADIUS using PAP. The following event logs appear:
Event 1
The audit log was cleared. Subject: Security ID: <account domain>\<account name> Account Name: <account name> Domain Name: <account domain> Logon ID: 0x67364F48Event 2
The computer attempted to validate the credentials for an account. Authentication Package: MICROSOFT_AUTHENTICATION_PACKAGE_V1_0 Logon Account: <account name> Source Workstation: Error Code: 0x0Event 3
A logon was attempted using explicit credentials. Subject: Security ID: SYSTEM Account Name: AuthenticationServer$ Account Domain: <account domain> Logon ID: 0x3E7 Logon GUID: {00000000-0000-0000-0000-000000000000} Account Whose Credentials Were Used: Account Name: <account name> Account Domain: <account domain> Logon GUID: {00000000-0000-0000-0000-000000000000} Target Server: Target Server Name: localhost Additional Information: localhost Process Information: Process ID: 0x3e4 Process Name: C:\Windows\System32\svchost.exe Network Information: Network Address: - Port: - This event is generated when a process attempts to log on an account by explicitly specifying that account’s credentials. This most commonly occurs in batch-type configurations such as scheduled tasks, or when using the RUNAS command.Event 4
An account was successfully logged on. Subject: Security ID: SYSTEM Account Name: AuthenticationServer$ Account Domain: <account domain> Logon ID: 0x3E7 Logon Type: 3 Impersonation Level: Impersonation New Logon: Security ID: <account domain>\<account name> Account Name: <account name> Account Domain: <account domain> Logon ID: 0x675FF2EE Logon GUID: {00000000-0000-0000-0000-000000000000} Process Information: Process ID: 0x3e4 Process Name: C:\Windows\System32\svchost.exe Network Information: Workstation Name: Source Network Address: - Source Port: - Detailed Authentication Information: Logon Process: IAS Authentication Package: MICROSOFT_AUTHENTICATION_PACKAGE_V1_0 Transited Services: - Package Name (NTLM only): - Key Length: 0 This event is generated when a logon session is created. It is generated on the computer that was accessed. The subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe. The logon type field indicates the kind of logon that occurred. The most common types are 2 (interactive) and 3 (network). The New Logon fields indicate the account for whom the new logon was created, i.e. the account that was logged on. The network fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases. The impersonation level field indicates the extent to which a process in the logon session can impersonate. The authentication information fields provide detailed information about this specific logon request. - Logon GUID is a unique identifier that can be used to correlate this event with a KDC event. - Transited services indicate which intermediate services have participated in this logon request. - Package name indicates which sub-protocol was used among the NTLM protocols. - Key length indicates the length of the generated session key. This will be 0 if no session key was requested.Event 5
Special privileges assigned to new logon. Subject: Security ID: <account domain>\<account name> Account Name: <account name> Account Domain: <account domain> Logon ID: 0x675FF2EE Privileges: SeSecurityPrivilege SeTakeOwnershipPrivilege SeLoadDriverPrivilege SeBackupPrivilege SeRestorePrivilege SeDebugPrivilege SeSystemEnvironmentPrivilege SeEnableDelegationPrivilege SeImpersonatePrivilegeEvent 6
An account was logged off. Subject: Security ID: <account domain>\<account name> Account Name: <account name> Account Domain: <account domain> Logon ID: 0x675FF2EE Logon Type: 3 This event is generated when a logon session is destroyed. It may be positively correlated with a logon event using the Logon ID value. Logon IDs are only unique between reboots on the same computer.These log entries seem to indicate the authentication request was successful. However, a Wireshark capture indicates the opposite:
Here are the Access-Request (Code 1) Attribute Value Pairs with a few actual values replaced with placeholders:
t=User-Name(1): <user name> t=User-Password(2): Decrypted: <password> t=NAS-IP-Address(4): 192.168.1.1 t=NAS-Identifier(32): <hostname> t=Calling-Station-Id(31): 192.168.1.2 t=NAS-Port(5): 5451 t=NAS-Port-Type(61): virtual(5)In response, I get an Access-Reject (Code 3).
Only these two RADIUS packets are exchanged. I would expect to see an Access-Accept that provides the Vendor Specific Attributes I have configured.
In "Active Directory Users and Computers", I have created a role of "Global" Group scope and of "Security" Group type. This role has a member of the appropriate type.
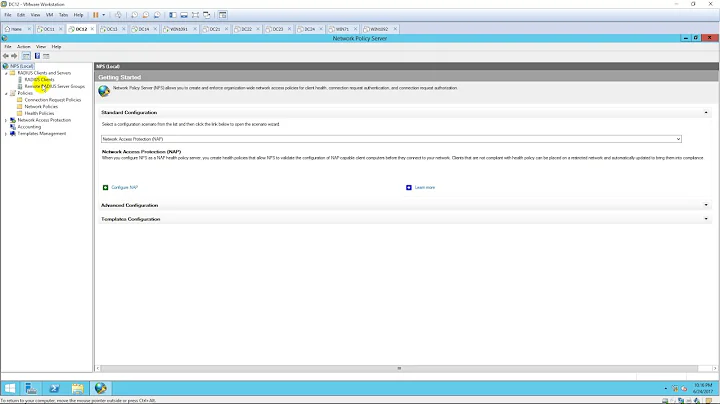
In "Network Policy Server", I have created and enabled a RADIUS client that does not use a shared secret template, and I have manually configured the shared secret. The vendor name is of type "RADIUS Standard".
In "Network Policy Server", I have created an enabled network policy with these attributes:
- Grant access - Type of network access server: Unspecified - A condition specifying the connecting user is a member of a Windows Group (which it is) - Authentication Methods: PAP - Standard RADIUS attribute FramedProtocol=PPP - Vendor-Specific RADIUS attributes: As appropriate for the device - NAP Enforcement: Allow full network access - Multilink and Bandwidth Allocation Protocol: Server settings determine Multilink usage - Encryption (all choices selected): "Basic encryption (MPPE 40-bit)", "Strong encryption (MPPE 56-bit)", "Strongest encryption (MPPE 128-bit)", "No encryption" - IP Settings: Server settings determine IP address assignmentDoes anybody have suggestions on how I can go about isolating the problem?
Thank you in advance!