FTP and iptables. Connection fails but ports are open
Solution 1
This was the solution. I don't know why other configs did not work!
# allowing active/passive FTP
iptables -A OUTPUT -p tcp --sport 21 -m state --state ESTABLISHED -j ACCEPT
iptables -A OUTPUT -p tcp --sport 20 -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A OUTPUT -p tcp --sport 1024: --dport 1024: -m state --state ESTABLISHED -j ACCEPT
iptables -A INPUT -p tcp --dport 21 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A INPUT -p tcp --dport 20 -m state --state ESTABLISHED -j ACCEPT
iptables -A INPUT -p tcp --sport 1024: --dport 1024: -m state --state ESTABLISHED,RELATED,NEW -j ACCEPT
Solution 2
Did you start proftp? There are 2 things that you need to do when setting up a service. You've got the first thing done, with the firewall allowing the ports to be opened. But the telnet would seem to be indicating that nothing is listening on ports 20 & 21.
You can use netstat and nmap to confirm.
netstat
$ sudo netstat -tapn -4 | grep -E ':20 |:21 '
I don't have FTP running so I'm going to use sshd as a stand-in for my example.
$ sudo netstat -tapn | grep -E ':20 |:21 |:22 '
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 894/sshd
tcp 0 0 192.168.1.20:51560 67.253.170.83:22 ESTABLISHED 5892/ssh
tcp 0 0 192.168.1.20:39411 192.168.1.109:22 ESTABLISHED 21079/ssh
tcp6 0 0 :::22 :::* LISTEN 894/sshd
tcp6 0 0 ::1:48375 ::1:22 ESTABLISHED 27962/ssh
tcp6 0 0 ::1:22 ::1:48375 ESTABLISHED 27963/sshd: saml [p
Here we can see the process ID for sshd, 894, which is the main sshd server on my system.
nmap
Nmap is a tool for scanning to see if ports are open on a system, and if something is listening. Where netstat works from the "inside", nmap works from the outside looking in.
$ sudo nmap -sS -P0 192.168.1.20
Starting Nmap 6.40 ( http://nmap.org ) at 2014-01-19 11:08 EST
Nmap scan report for 192.168.1.20
Host is up (0.000013s latency).
Not shown: 998 closed ports
PORT STATE SERVICE
22/tcp open ssh
111/tcp open rpcbind
Nmap done: 1 IP address (1 host up) scanned in 11.44 seconds
Here we can see that only sshd and rpcbind are allowed access from the external LAN.
iptable rules
Given you're able to connect via FTP when the firewall is down, this would seem to indicate an issue with your rules. Try these instead.
allow port 21 in/out
$ sudo iptables -A INPUT -p tcp -m tcp --dport 21 -m conntrack --ctstate ESTABLISHED -j ACCEPT -m comment --comment "Allow ftp connections on port 21"
$ sudo iptables -A OUTPUT -p tcp -m tcp --dport 21 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -m comment --comment "Allow ftp connections on port 21"
allow port 20 in/out - active
$ sudo iptables -A INPUT -p tcp -m tcp --dport 20 -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT -m comment --comment "Allow ftp connections on port 20"
$ sudo iptables -A OUTPUT -p tcp -m tcp --dport 20 -m conntrack --ctstate ESTABLISHED -j ACCEPT -m comment --comment "Allow ftp connections on port 20"
allow port 20 in/out - passive
$ sudo iptables -A INPUT -p tcp -m tcp --sport 1024: --dport 1024: -m conntrack --ctstate ESTABLISHED -j ACCEPT -m comment --comment "Allow passive inbound connections"
$ sudo iptables -A OUTPUT -p tcp -m tcp --sport 1024: --dport 1024: -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT -m comment --comment "Allow passive inbound connections"
Source: Iptables to allow incoming FTP
Related videos on Youtube
Skip
Updated on September 18, 2022Comments
-
Skip over 1 year
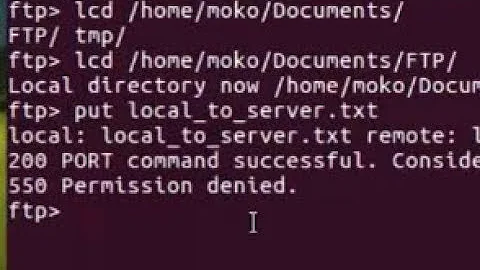
I installed proftp on my machine.
With iptables disabled I can connect to the machine, using ftp-client or telnet.
With iptables connection fails - telnet says "Connection failed"# works telnet 192.10.10.11 22 # connection failed telnet 192.19.10.11 20 telnet 192.19.10.11 21I found this topic, but it did not help.
Since I do open the Ports 22 and 21,20 the same way they should all be accessable through telnet? But 22 works and 21,20 fail. Any ideas why this happens?
sudo iptables -L -vChain INPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 0 0 ACCEPT all -- lo any anywhere anywhere 100 7136 ACCEPT tcp -- any any anywhere anywhere tcp dpt:ssh 3 152 ACCEPT tcp -- any any anywhere anywhere tcp dpt:ftp 0 0 ACCEPT tcp -- any any anywhere anywhere tcp dpts:1010:1012 586 78898 ACCEPT udp -- eth0 any anywhere anywhere udp dpt:openvpn 0 0 ACCEPT all -- tun+ any anywhere anywhere 348 22567 ACCEPT all -- tap+ any anywhere anywhere 69 10294 DROP all -- any any anywhere anywhere Chain FORWARD (policy DROP 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 0 0 ACCEPT all -- any lo anywhere anywhere 95 11028 ACCEPT tcp -- any any anywhere anywhere tcp spt:ssh 0 0 ACCEPT tcp -- any any anywhere anywhere tcp spt:ftp-data 354 55626 ACCEPT udp -- any eth0 anywhere anywhere udp dpt:openvpn 0 0 ACCEPT all -- any tun+ anywhere anywhere 353 26295 ACCEPT all -- any tap+ anywhere anywhere 4 392 DROP all -- any any anywhere anywhereiptables configurations:#!/bin/sh # Flushing all rules iptables -F iptables -X # Setting default filter policy iptables -P INPUT DROP iptables -P OUTPUT DROP iptables -P FORWARD DROP # Allow unlimited traffic on loopback iptables -A INPUT -i lo -j ACCEPT iptables -A OUTPUT -o lo -j ACCEPT # Allow ssh on Port 22 iptables -A INPUT -p tcp --dport 22 -j ACCEPT iptables -A OUTPUT -p tcp --sport 22 -j ACCEPT # Ports for FTP #Allowing FTP Connections, including passive ports. (proftpd) sudo iptables -A INPUT -p tcp --dport 21 -j ACCEPT # Allowing FTP Connections in active mode, where Data are passed through Port 20 sudo iptables -A OUTPUT -p tcp --sport 20 -j ACCEPT # Allowing Ports for Passive Mode connection, where Data is passed through ports sudo iptables -A INPUT -p tcp --dport 1010:1012 -j ACCEPT # allow connection via 1194 so that openVpn can use the network adapter iptables -A INPUT -i eth0 -p udp --dport 1194 -j ACCEPT iptables -A OUTPUT -o eth0 -p udp --dport 1194 -j ACCEPT # allow connections via openVPN tun and tap interfaces iptables -A INPUT -i tun+ -j ACCEPT iptables -A OUTPUT -o tun+ -j ACCEPT iptables -A INPUT -i tap+ -j ACCEPT iptables -A OUTPUT -o tap+ -j ACCEPT # make sure nothing else comes or goes out of this box iptables -A INPUT -j DROP iptables -A OUTPUT -j DROP-
 Steffen Ullrich over 10 yearsThis is a duplicate to stackoverflow.com/questions/21218563/… und you'll find the answer there.
Steffen Ullrich over 10 yearsThis is a duplicate to stackoverflow.com/questions/21218563/… und you'll find the answer there. -
Skip over 10 yearsThe post is about to be closed. Ane there are no right answers yet.
-
 slm over 10 yearsSkip, please do not cross-post the same Q's on the different SE sites. That's a close reason on most of them. Delete that other SO Q and we can leave this one here.
slm over 10 yearsSkip, please do not cross-post the same Q's on the different SE sites. That's a close reason on most of them. Delete that other SO Q and we can leave this one here.
-
-
Skip over 10 yearsI added your rules for ports 21, 20 - still cant telnet..
-
 slm over 10 years@Skip - Is proftp listening on the external IP interface or the 127.0.0.1 i/f? Output of
slm over 10 years@Skip - Is proftp listening on the external IP interface or the 127.0.0.1 i/f? Output ofnetstat -tapn -4 | grep ":21 "will reveal this. -
Skip over 10 yearsThe answer was: tcp 0 0 0.0.0.0:21 0.0.0.0:* LISTEN 2217/proftpd: (acce
-
Skip over 10 yearsIts Raspbian. Consider that the connection with iptables rules flushed - works. With rules listed above it doesn't. Looks for me, as if some cache is not cleared and ports remain blocked as soon as the default policy is configured to block everything
-
 slm over 10 years@Skip - it's likely the new & established states of the connection. Is this kernel module installed?
slm over 10 years@Skip - it's likely the new & established states of the connection. Is this kernel module installed?modprobe ip_conntrack_ftp -
Skip over 10 yearsnope. somehow I found at least a configuration, which allowed me to telnet on port 21, see my post below. Thnx for help!
-
 slm over 10 yearsSomething else must be at play here, I've found the example on dozens of sites and the order doesn't seem to be a factor, for eg: tuxradar.com/answers/80, has it similar to my A too.
slm over 10 yearsSomething else must be at play here, I've found the example on dozens of sites and the order doesn't seem to be a factor, for eg: tuxradar.com/answers/80, has it similar to my A too. -
 slm over 10 yearsWhat FTP client are you using to test this?
slm over 10 yearsWhat FTP client are you using to test this? -
Skip over 10 yearsFilezilla, Windows Explorer, XBMC, telnet, Chrome