How can I allow one user to su to another without allowing root access?
Solution 1
Yes, this is possible.
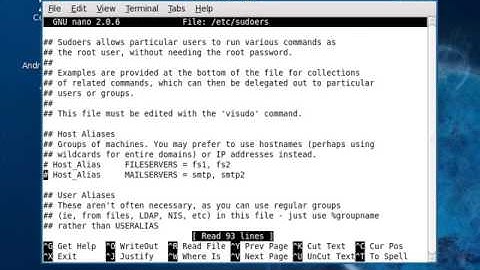
In /etc/sudoers the item immediately following the equals is the user that the command will be allowed to execute as.
tom ALL=(oracle) /bin/chown tom *
The user (tom) can type sudo -u oracle /bin/chown tom /home/oracle/oraclefile
Solution 2
Add to your /etc/sudoers something like
tom ALL=(oracle) ALL
Then user tom should be able to use sudo to run things as user oracle with the -u option, without letting tom
I.e. getting a shell as user oracle (well, given that your sudo is new enough to have the -i option).
sudo -u oracle -i
Solution 3
To ONLY provide the capabilities in the question, add the following to /etc/sudoers:
tom ALL=(oracle) /bin/bash
Then tom can:
sudo -u oracle bash -i
Solution 4
For instance, I'd like to allow Tom the DBA to su to the oracle user, but not to the tomcat user or root.
I needed to do this to a system recently and had a hard time finding my notes on the alternate setup i used years ago that also allowed the syntax su <user>. In my situation I needed to allow multiple users to su to a specific user.
Create a group using addgroup <groupName> that other users will be able to su to without a password. Then add that group to each user that you want to be able to su to that user without a password:
usermod -a -G <groupName> <userName> (or usermod -a -G oracle tom). The group changes might not take affect until next login.
Note: In your case, you already have the group because oracle group would have been created when you made the oracle user with adduser oracle.
Now edit /etc/pam.d/su and under the following:
# This allows root to su without passwords (normal operation)
auth sufficient pam_rootok.so
..add auth rule lines so the section looks like this:
# This allows root to su without passwords (normal operation)
auth sufficient pam_rootok.so
auth [success=ignore default=1] pam_succeed_if.so user = <groupName>
auth sufficient pam_succeed_if.so use_uid user ingroup <groupName>
Replace <groupName> with oracle in this case. This will allow any user that is part of the <groupName> to su <groupName>
Now tom can su oracle and if you need to give other users the same access, add them to oracle group.
similar question here
Related videos on Youtube
Comments
-
gharper over 1 year
I'd like to allow certain users to su to another user account without having to know that account's password, but not allow access to any other user account (i.e. root).
For instance, I'd like to allow Tom the DBA to su to the oracle user, but not to the tomcat user or root.I imagine this could be done with the /etc/sudoers file - is it possible? If so, how?
-
gharper almost 15 yearsThis would allow Tom to run commands as oracle, but not to actually become the oracle user
-
 phirschybar almost 15 yearsWhat about sudo -u oracle su -? That would give him a shell opened as the oracle user. Is that what you want?
phirschybar almost 15 yearsWhat about sudo -u oracle su -? That would give him a shell opened as the oracle user. Is that what you want? -
Annika Backstrom almost 15 years+1 for that last comment, Brent. That would be my answer.
-
gharper almost 15 yearsYup that'll work!
-
Mark almost 15 yearsSomething like the following would work: sudo -u oracle -s or sudo -u oracle -i (-s for shell, -i for login - does a login shell). Unfortunately I don't know offhand what you would use in /etc/sudoers to limit the user, but given that you're allowing them shell access, you probably just want to do tom ALL=(oracle) ALL as someone else mentioned. If they can run a shell, you probably don't care about restriction the commands they can run.
-
Scott Pack almost 15 yearsIdeally, would you not want Tom to run commands as the oracle user, instead of becoming the oracle user? The distinction is slight, but it provides a great audit log without having to futz with using an audit shell.
-
snowindy over 8 yearsI had to use syntax
tom ALL=(oracle)NOPASSWD:ALLto make sudo not to ask password -
JohnDavid over 3 yearssnowindy - It is asking tom for his own password to confirm the sudo not for the oracle password. NOPASSWD makes it easier for scripts, but less secure to another user who happens to be running as tom.