How can I limit ssh *remote* port forwarding?
Solution 1
This has been implemented in OpenSSH 7.8p1, which was released 2018-08-24. Quote from the release notes:
add a PermitListen directive to sshd_config(5) and a corresponding permitlisten= authorized_keys option that control which listen addresses and port numbers may be used by remote forwarding (ssh -R ...).
Solution 2
There's an option no-port-forwarding that you can use, that prevents all port forwarding. Present at least as of OpenSSH 4.3p2 (CentOS 5.3 - oldest machine I have access to). Put it in the same place that you would have put permitopen.
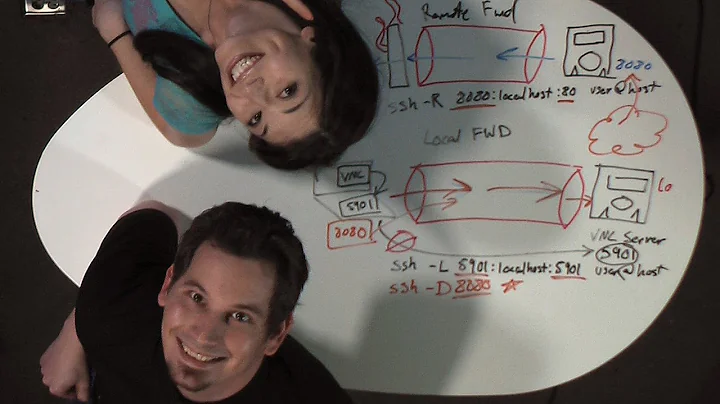
Related videos on Youtube
Lluís
Updated on September 18, 2022Comments
-
 Lluís over 1 year
Lluís over 1 yearI need to limit which ports can be remotely '
ssh -R' forwarded by an user.I know about
permitopenoption on authorized_keys, but as it says on man page it only limits local 'ssh -L' port forwardingAs discussed here a user would get the same with
netcator similar, but in this case user has no shell accessI also found this thread that talks about using selinux or
LD_PRELOAD, but I never configured selinux before and can't find info on how to do that withLD_PRELOAD.maybe someone have made a patch for openssh to implement that?
EDIT: I've found this bug report so I guess it's not yet implemented
-
alex88 over 7 yearsHave you found a solution for this?
-
 Lluís over 7 yearsI didn't, I guess it can't be done until the above bug is closed or someone writes a patch to implement this
Lluís over 7 yearsI didn't, I guess it can't be done until the above bug is closed or someone writes a patch to implement this
-
-
gertvdijk over 11 yearsCompletely disabling port forwarding seems overkill and not fit for the question. I assume OP wants to limit it, yet allowing some specific remote port forwardings.
-
 Lluís over 11 yearsYes, I need to allow some ports forwarding
Lluís over 11 yearsYes, I need to allow some ports forwarding -
 davesave over 7 yearsWill there ever be a solution to this (beside iptables)?
davesave over 7 yearsWill there ever be a solution to this (beside iptables)?