How do I install a PFX certificate file into Ubuntu so Curl trusts it?
Solution 1
You can use the openssl command to convert nearly any certificate format to another. PFX is another name for a pkcs12 container.
If you can extract the cert in PEM format curl should be able to use it.
openssl pkcs12 -in cert.pfx -clcerts -out cert.pem
This may ask you for a password which will be the one used to secure the PKCS12 file
You want to use the output cert.pem file with the --cacert curl command line option not -k
Solution 2
Under the Debian family the distribution way of handling a trust certificate is as follows (reverse engineered by looking at update-ca-certificates):
I will use myca as a standin name for your ca (or self-signed) cert and myca.crt as the file with the certificate (DER or PEM). The .crt is mandatory.
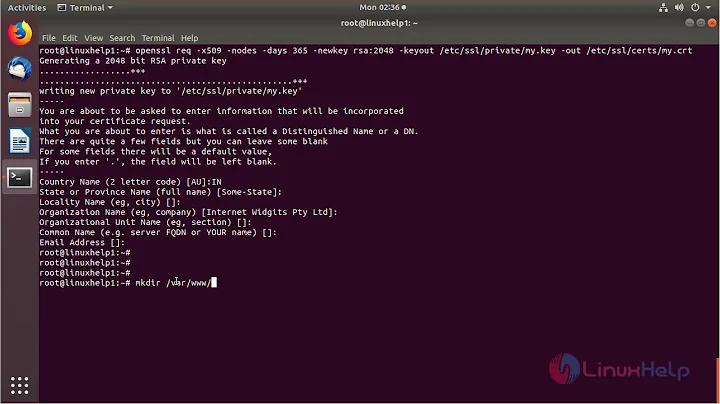
- Make directory under /usr/share/ca-certificates
mkdir /usr/share/ca-certificates/myca
- Put the ca.crt in it
cp ./ca.crt /usr/share/ca-certificates/myca/
- Run dpkg-reconfigure ca-certificates, choose ask to selectively add new trust anchors and select in the second screen your new myca/myca.crt and press OK
dpkg-reconfigure ca-certificates
To do it more programmatically
After you made the directory and put your cert in:
echo myca/myca.crt >> /etc/ca-certificates.conf
/usr/sbin/update-ca-certificates
This last method does not record the configure setting in /var/cache/debconf/config.dat so if you run dpkg-reconfigure ca-certificates or update the ca-certificates package, your new trust anchor may disappear again. Running update-ca-certificates is safe.
To get only the certificate from a pfx with self-signed certificate:
openssl pkcs12 -in my.pfx -nokeys -out myca.crt
And enter the password to open the pfx.
Adding a self-signed certificate to the root level central trust repository does mean that everyone who possesses its private key gets ways to do MITM attacks on your server.
Related videos on Youtube
Luke Puplett
Updated on September 18, 2022Comments
-
Luke Puplett over 1 year
I'm running Ubuntu 18.04 on Windows Subsystem for Linux 2. I am making a
curlrequest to a web service running on the Windows side using a self-signed certificate. I receive this error:curl: (60) SSL certificate problem: unable to get local issuer certificate
I'd like to add the cert to the local store. I have a
.pfxfile available. I know I can use-kbut I want to use other command line tools against this server.How do I do this?
My own trials
openssl s_client -showcerts -servername server -connect server:443 > foo.pem openssl x509 -in foo.pem -inform PEM -out foo.crt sudo cp foo.crt /usr/local/share/ca-certificates/ sudo update-ca-certificatesThis looks plausible but didn't work,
curlstill has the same complaint.I also tried to use a
DERversion.sudo rm /usr/local/share/ca-certificates/windows_cert.crt openssl x509 -in windows_cert.pem -inform PEM -out windows_cert_der.crt -outform DER sudo cp windows_cert_der.crt /usr/local/share/ca-certificates/ sudo update-ca-certificatesGive up
Don't worry, I started following some of the replies here.
https://askubuntu.com/questions/73287/how-do-i-install-a-root-certificate
But got nowhere, its obviously a very hard problem in the world of computing.
I've found that a few months back they added a switch to the command line tool I need to use that ignores certificate problems.
-
Luke Puplett about 4 yearsWonderful, thanks. Can you elaborate on "installing" the certificate into a store so its trusted by any client tool?
-
hardillb about 4 yearsYou might want to try putting the DER encoded file in
/usr/share/ca-certificatesrather than in/usr/local... -
Gerrit about 4 yearsThe
-clcertsoption is for client certificates. Didn't you guys mean-cacerts? By the way, not every pfx contains the certificate chain, unless of course the certificate is self-signed. -
Luke Puplett about 4 yearsI don't really know what I mean, I don't know about certificates, I just want tools running on Ubuntu to trust my development HTTPS website with a self-signed certificate. I literally don't care how its done, I just need my life back.
-
hardillb about 4 yearsI'm suggesting that the
update-ca-certificatetool is not looking in the/usr/local/share/ca-certificatedirectory and you should put your cert into/usr/share/ca-certificatefor it to be added to the trusted set -
hardillb about 4 years@user188737 no, the OP said it was a self signed cert it shouldn't matter which you use, but using the client cert covers the situation you mentioned of not having a CA chain.
-
Psijic over 2 yearsHello, I converted my .pfx certificate this way but after opening it in KDE GUI, I can't unlock the new .pem cert because it said - password is wrong. I used same password/passphrase everywhere pasting it, so not sure what password is needed.