How to configure OpenVPN multiple authentication method?
OpenVPN 2.0 and later include a feature that allows the OpenVPN server to securely obtain a username and password from a connecting client, and to use that information as a basis for authenticating the client.
To use this authentication method, first add the auth-user-pass directive to the client configuration. It will direct the OpenVPN client to query the user for a username/password, passing it on to the server over the secure TLS channel.
Next, configure the server to use an authentication plugin, which may be a script, shared object, or DLL. The OpenVPN server will call the plugin every time a VPN client tries to connect, passing it the username/password entered on the client. The authentication plugin can control whether or not the OpenVPN server allows the client to connect by returning a failure (1) or success (0) value.
Using Script Plugins
Script plugins can be used by adding the auth-user-pass-verify directive to the server-side configuration file. For example:
auth-user-pass-verify auth-pam.pl via-file
will use the auth-pam.pl perl script to authenticate the username/password of connecting clients. See the description of auth-user-pass-verify in the manual page for more information.
The auth-pam.pl script is included in the OpenVPN source file distribution in the sample-scripts subdirectory. It will authenticate users on a Linux server using a PAM authentication module, which could in turn implement shadow password, RADIUS, or LDAP authentication. auth-pam.pl is primarily intended for demonstration purposes. For real-world PAM authentication, use the openvpn-auth-pam shared object plugin described below.
Using Shared Object or DLL Plugins
Shared object or DLL plugins are usually compiled C modules which are loaded by the OpenVPN server at run time. For example if you are using an RPM-based OpenVPN package on Linux, the openvpn-auth-pam plugin should be already built. To use it, add this to the server-side config file:
plugin /usr/share/openvpn/plugin/lib/openvpn-auth-pam.so login
This will tell the OpenVPN server to validate the username/password entered by clients using the login PAM module.
For real-world production use, it's better to use the openvpn-auth-pam plugin, because it has several advantages over the auth-pam.pl script:
The shared object openvpn-auth-pam plugin uses a split-privilege execution model for better security. This means that the OpenVPN server can run with reduced privileges by using the directives user nobody, group nobody, and chroot, and will still be able to authenticate against the root-readable-only shadow password file. OpenVPN can pass the username/password to a plugin via virtual memory, rather than via a file or the environment, which is better for local security on the server machine. C-compiled plugin modules generally run faster than scripts. If you would like more information on developing your own plugins for use with OpenVPN, see the README files in the plugin subdirectory of the OpenVPN source distribution.
To build the openvpn-auth-pam plugin on Linux, cd to the plugin/auth-pam directory in the OpenVPN source distribution and run make.
Using username/password authentication as the only form of client authentication
By default, using auth-user-pass-verify or a username/password-checking plugin on the server will enable dual authentication, requiring that both client-certificate and username/password authentication succeed in order for the client to be authenticated.
While it is discouraged from a security perspective, it is also possible to disable the use of client certificates, and force username/password authentication only. On the server:
client-cert-not-required
Such configurations should usually also set:
username-as-common-name
which will tell the server to use the username for indexing purposes as it would use the Common Name of a client which was authenticating via a client certificate.
Note that client-cert-not-required will not obviate the need for a server certificate, so a client connecting to a server which uses client-cert-not-required may remove the cert and key directives from the client configuration file, but not the ca directive, because it is necessary for the client to verify the server certificate.
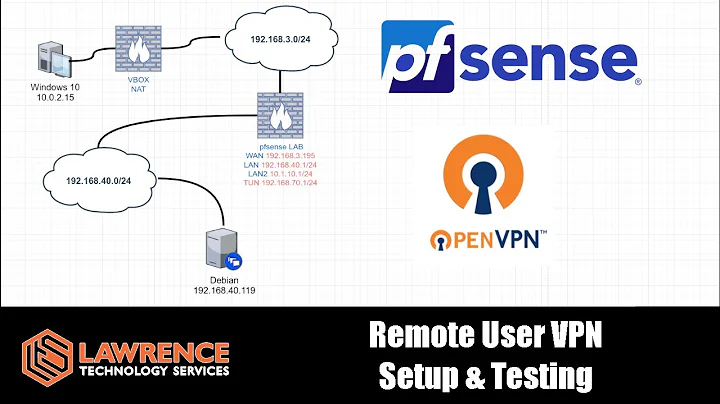
Related videos on Youtube
salman.isha
Updated on September 18, 2022Comments
-
salman.isha over 1 year
I use mfa to connect to OpenVPN. There is now a client requirement that they want to connect to OpenVPN through a click with a .bat or .cmd file. I found a solution to auto connect to OpenVPN with the username and password. However to do this I had to disable mfa in the pam config file.
Is there any way to keep both authentication methods? Can a specific user have the auto login profile, while other users would still need to use mfa to login?
My configuration is below:
client dev tun proto udp remote xx.xx.xx.xxx Protocol nobind resolv-retry infinite persist-key persist-tun auth-user-pass pass.txt auth-nocache ca ca.crt cert user.crt key user.key comp-lzo verb 4 tls-auth ta.key 1 cipher AES-256-CBC remote-cert-tls server keepalive 5 300 reneg-sec 36000And server.conf:
port 1194 proto udp dev tun ca /etc/openvpn/easy-rsa/2.0/keys/xxxx.crt cert /etc/openvpn/easy-rsa/2.0/keys/xxxx.crt key /etc/openvpn/easy-rsa/2.0/keys/xxxx.key # This file should be kept secret dh /etc/openvpn/easy-rsa/2.0/keys/xxxx.pem server xx.xx.xx.xx 255.255.255.0 ifconfig-pool-persist ipp.txt push "route 192.16.5.0 255.255.255.0" push "route 192.16.6.0 255.255.255.0" push "route 192.16.7.0 255.255.255.0" push "route 192.16.8.0 255.255.255.0" push "dhcp-option DNS 132.196.243.9" push "dhcp-option DNS 8.8.8.8" keepalive 5 300 reneg-sec 36000 tls-auth /etc/openvpn/easy-rsa/2.0/keys/xxxx.key 0 # This file is secret cipher AES-256-CBC # AES comp-lzo user nobody group nobody persist-key persist-tun status openvpn-status.log log-append /var/log/openvpn.log verb 5 plugin /usr/lib64/openvpn/plugins/openvpn-plugin-auth-pam.so openvpn # This is my authentication plugin. I want to use another one along with it. -
salman.isha over 8 yearsHi Manjesh thank you for your reply. I have read the procedures you said however, my problem is i want to keep two authentication plugin. For example: plugin /usr/lib64/openvpn/plugins/openvpn-plugin-auth-pam.so login plugin /usr/lib64/openvpn/plugins/openvpn-plugin-auth-pam.so openvpn above the problem is although two plugins are active but it only authenticates with openvpn plugin. But i want to use one special user who can authenticate only with login plugin. Other users will use openvpn plugin. is it possible ?
-
 manjesh23 over 8 yearsAre you looking for dual/two factor authentication?
manjesh23 over 8 yearsAre you looking for dual/two factor authentication? -
 manjesh23 over 8 years
manjesh23 over 8 years -
salman.isha over 8 yearsmy openvpn plugin has two factor authentication. where we use local user password and google authenticator code. I just want to create another user in linux who can login openvpn only with user password by login plugin.
-
 manjesh23 over 8 yearsI don't think this will be an open for you, once you have the two-factor auth configured, you will lose the basic auth functionality.
manjesh23 over 8 yearsI don't think this will be an open for you, once you have the two-factor auth configured, you will lose the basic auth functionality. -
salman.isha over 8 yearsi see.. but is there any way ? changing any configuration file or something ? btw thanks for your prompt reply.
-
 manjesh23 over 8 yearsIf this answers your question, please click on accept button --> right next to my answer
manjesh23 over 8 yearsIf this answers your question, please click on accept button --> right next to my answer -
 Mokubai over 8 yearsPlease don't beg for accepts or upvotes. If you get the accept then cool, but it is up to OP who they reward.
Mokubai over 8 yearsPlease don't beg for accepts or upvotes. If you get the accept then cool, but it is up to OP who they reward. -
 manjesh23 over 8 years@Mokubai, yeah I agree accept button not only give rep but also helpful for other users to identify the correct answer if one question has multiple answer. Hence requested.
manjesh23 over 8 years@Mokubai, yeah I agree accept button not only give rep but also helpful for other users to identify the correct answer if one question has multiple answer. Hence requested. -
 Mokubai over 8 yearsAdditionally if you are copying a significant amount of text from external sites then you should blockquote the text section and provide a link to the site you got it from. A large portion of this is copied from openvpn.net/index.php/open-source/documentation/howto.html please read How to reference material written by others. You should be able to edit your answers to provide the correct attribution.
Mokubai over 8 yearsAdditionally if you are copying a significant amount of text from external sites then you should blockquote the text section and provide a link to the site you got it from. A large portion of this is copied from openvpn.net/index.php/open-source/documentation/howto.html please read How to reference material written by others. You should be able to edit your answers to provide the correct attribution. -
maxadamo over 4 yearsyou did copy & paste from openVPN website. There is no need for that. You should have briefly explained, and then linked the source. openvpn.net/community-resources/how-to/…