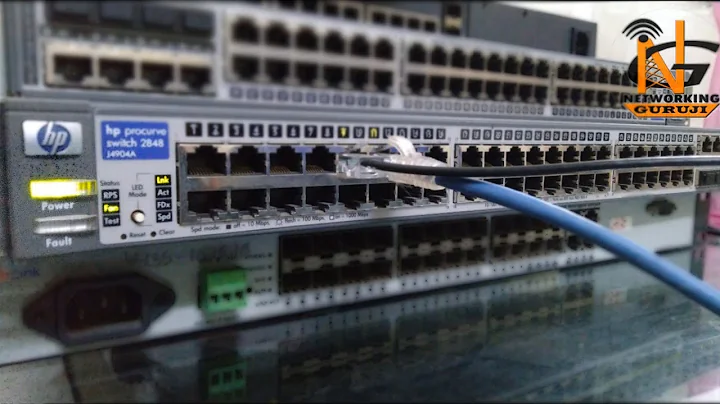
HP ProCurve Preventing Loops and Users Plugging in Unauthorized Switches/Access-Points
In the end I used a combination of spanning-tree commands and HP loop-protect:
loop-protect 1-44
spanning-tree
spanning-tree bpdu-protection-timeout 600 priority 1
spanning-tree 1-44 admin-edge-port
spanning-tree 1-44 bpdu-protection
I only did this for the edge ports, anything connected to other switches (in my case on ports 45-48) were left as default (without spanning tree or loop protect commands).
Related videos on Youtube
morleyc
Updated on September 18, 2022Comments
-
morleyc almost 2 years
We have a
HP ProCurve 2530-24-PoE (J9773A)switch, recently I had a user who plugged in an Apple wireless hardware device to the network - whenever it was connected I got a ton of broadcast warnings from the switch, intermittent bouts of packet loss and switch CPU usage went through the roof.I removed his device and all is fine... given the entire office went down and no body could work every time it was plugged in I wasn't able to find the root cause other than something to do with the Apple hardware config. I can only assume he has setup as a client bridge to connect to the WiFi and caused a loop back via the Apple Ethernet port!
I have spanning-tree enabled on the HP ProCurve, but this didn't stop the network going down.
I am looking at stopping this happening again (and further more lock users from connecting their own unauthorized access-points/switches to the network) and seen the following recommended commands to harden against loops here https://cs.uwaterloo.ca/cscf/reports/CNAG/2009/ProCurve%20Best%20Practices.pdf:
loop-protect 1-24 spanning-tree 1-24 root-guard spanning-tree 1-24 bpdu-protection spanning-tree 1-24 admin-edge-port loop-protect 1-24Question 1 - Can one sleep easy at night with those commands or anything I should be aware with the above?
Question 2 - Will the above commands stop people messing with the network and connecting their own hardware, or are any other commands needed?
Question 3 - If we have our own authorized wireless devices, would
bpdu-protectionstop the bridging of clients on the wireless access point, and should we leave this off on the ports that are connected to our wireless access points?Question 4 - We have a voice VLAN setup and specified as voice:
vlan 69 name "DATA_VLAN" untagged 1-24 no ip address exit vlan 70 name "VOICE_VLAN" tagged 1-24 no ip address qos dscp 101110 voice exitThe phones plug in to the switch, and computers to the back of the phone. Similair to question 3, how will
bpdu-protectionaffect the fact I have a PC behind each phone (so essentially 2 MAC addresses per port). Does the fact thevoiceis specified in the voice vlan 70 allow for and take care of this?-
 ewwhite about 9 yearsDo you want to share the actual model of your HP Switch?
ewwhite about 9 yearsDo you want to share the actual model of your HP Switch? -
morleyc about 9 yearsThanks for the quick reply it's a 2530-24-PoE, I have updated the question with this info
-
Brian about 9 yearsCan also start using Web and MAC Authentication to provide port based security to deny or give limited access to unknown devices.
-