id command is not showing secondary groups
Solution 1
I'm confused, your groups use "memberuid: $username", which is RFC2307, so why dooes your config specify rfc2307bis and uniqueMember?
I would propose to use rfc2307 (which is the default) and if that doesn't work, crank up the debugging and see what queries are made towards the LDAP server.
Solution 2
When you replace the default:
ldap_schema = rfc2307
with
ldap_schema = rfc2307bis
in your sssd.conf file you need to follow the instructions from the SSSD FAQ:
SSSD supports three LDAP schema types: RFC 2307, RFC 2307bis and IPA (the last being an extension of RFC 2307bis including memberOf backlinks).
By default, SSSD will use the more common RFC 2307 schema. The difference between RFC 2307 and RFC 2307bis is the way which group membership is stored in the LDAP server. In an RFC 2307 server, group members are stored as the multi-valued attribute
memberuidwhich contains the name of the users that are members. In an RFC2307bis server, group members are stored as the multi-valued attribute member (or sometimesuniqueMember) which contains the DN of the user or group that is a member of this group. RFC2307bis allows nested groups to be maintained as well.So the first thing to try when you hit this situation is to try setting
ldap_schema = rfc2307bis, deleting/var/lib/sss/db/cache_DOMAINNAME.ldband restarting SSSD. If that still doesn't work, addldap_group_member = uniqueMember, delete the cache and restart once more. If that still doesn't work, it's time to file a bug.
Related videos on Youtube
ITPro Guy
Passionate about IT. Intoducing myself to the development world. Learning everyday.
Updated on September 18, 2022Comments
-
ITPro Guy almost 2 years
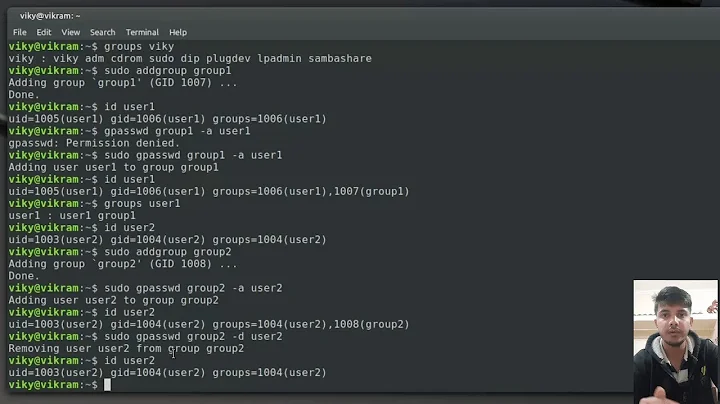
During some days I've been working on a LDAP integration. Now, after configure almost everything that I needed, I came up with this last wall: The need of use secondary groups which are taken from the LDAP server.
Behaviour:
[root@sr-servicesLin ~]# id hmr uid=2956(hmr) gid=10000(ldapusers) groups=10000(ldapusers) [root@sr-servicesLin ~]# getent group repo repo:*:25958: [root@sr-servicesLin ~]# groups hmr hmr : ldapusersContent of repo group (it's a LDAP group):
[root@sr-dns ~]# ldapsearch -x -H ldaps://ldap.eibind.iss -b "dc=eibind,dc=iss" "(&(objectclass=posixGroup)(cn=repo)(gidNumber=*))" # extended LDIF # # LDAPv3 # base <dc=eibind,dc=iss> with scope subtree # filter: (&(objectclass=posixGroup)(cn=repo)(gidNumber=*)) # requesting: ALL # # repo, Groups, eibind.iss dn: cn=repo,ou=Groups,dc=eibind,dc=iss objectClass: posixGroup objectClass: top cn: repo memberUid: hmr memberUid: jcontreras memberUid: hectoriss gidNumber: 25958 # search result search: 2 result: 0 SuccessThe scenario:
OS: Centos 6.7
Packages:
· ldap running with ssl
· sssd installed
· nss-pam-ldapdThe problem is:
When I use
idcommand I'm not getting the secondary groups of every user, just the principal one (which comes from LDAP, so there is a connection).I'm going to paste the main config files, I think that I put everything in the correct place. Surfing between sites, I read that is not recommended to have sssd and nsswitch configured at the same time, like configure
ldapandsssfor "parse" all the desired data from the server, that it could be a mess for the server or something like that. Despite of this, I wrote ldap and sss as a data sources.nsswitch.conf
# # /etc/nsswitch.conf # passwd: files ldap sss shadow: files ldap sss group: files ldap sss #hosts: db files nisplus nis dns hosts: files dns bootparams: nisplus [NOTFOUND=return] files ethers: files netmasks: files networks: files protocols: files rpc: files services: files ldap sss netgroup: files ldap sss publickey: nisplus automount: files ldap sss aliases: files ldap nisplusAs you can see, I'm asking to ldap and sss (sssd) about the passwd, shadow and groups. Combined with this config, I also have the sssd.conf file, which is the following:
sssd.conf
[sssd] config_file_version = 2 services = nss, pam, autofs domains = default [nss] filter_users = root,ldap,named,avahi,haldaemon,dbus,radiusd,news,nscd [pam] [domain/default] ldap_tls_reqcert = allow auth_provider = ldap ldap_schema = rfc2307bis krb5_realm = eibind.iss ldap_search_base = dc=eibind,dc=iss ldap_group_member = uniqueMember id_provider = ldap ldap_id_use_start_tls = True chpass_provider = ldap ldap_uri = ldaps://ldap.eibind.iss/ #ldap_user_object_class = user #ldap_group_object_class = group #ldap_group_search_base = OU=Groups,DC=eibind,DC=iss #ldap_group_search_scope = one #ldap_group_object_class = group ldap_chpass_uri = ldaps://ldap.eibind.iss/ krb5_kdcip = ldap.eibind.iss cache_credentials = True ldap_tls_cacertdir = /etc/openldap/cacerts entry_cache_timeout = 600 ldap_network_timeout = 3 krb5_server = ldap.eibind.iss autofs_provider = ldap [autofs]Here we can see that I'm using
ldap_schema = rfc2307bisandldap_group_member = uniqueMember.I say that because I found over the net that I should change
ldap_schema = rfc2307bistoldap_schema = rfc2307but it still does not work.Also, there are some commented lines which I previously tried but without success.
To finish, I'm going to paste the nslcd.conf. In here I just followed this tutorial: https://arthurdejong.org/nss-pam-ldapd/setup , so my config file is as it comes plus these following lines:
# This comment prevents repeated auto-migration of settings. uri ldap://ldap.eibind.iss/ base dc=eibind,dc=iss uid nslcd gid nslcdI have to be missing something, some value, some stupid config. Probably I spend around 3-4 days looking at this, so any help with be very grateful.
Thanks in advance.
-
user9517 about 8 yearsHe lives Whoop :)
-
ITPro Guy about 8 yearsNo, it doesn't work. I already tried before post this question.
-
dawud about 8 yearsPlease check my last edit.
-
ITPro Guy about 8 yearsBy default is
ldap_scheme= rfc2307bis. I also deleted caches after modifications but it still not working properly. Btw, thank you very much for your dedication. @dawud -
ITPro Guy about 8 yearsOh man, you really save my time. It was too obvious. Thank you all very much, especially to @jhrozek


![How To Manage Local Groups & Users For Windows From CMD[Command Prompt]](https://i.ytimg.com/vi/WSTlArxx0J8/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLDkf-z6-jmDK_lqG0P_5ls9kKDEfQ)