IPSec tunnel between FortiGate and iPhone / iOS - Works except for DNS / Wins
Solution 1
You need to disable split tunelling for the DNS requests to be internal and not external!
UNSET ipv4-split-include "Dialup_VPN_Networks" will do the trick.
Solution 2
perhaps you need to configure some firewall policies. Source interface should be iPhone_VPN and destination interface is the interface where your DNS and WINS server are connected to. Hope it helps. -Pietro.
Related videos on Youtube
Admin
Updated on September 17, 2022Comments
-
 Admin almost 2 years
Admin almost 2 yearsI have configured my Fortigate with a new VPN IPSec tunnel to allow the iOS Cisco client to connect. That works fine. I can RDP to my servers, browse to my servers via IP address, etc.
But, the iPhone does not resolve my internal IP addresses. I have added the DNS servers that serve addresses for my internal users, as well as the WINS servers, but the iPhone acts like it doesn't see them at all.
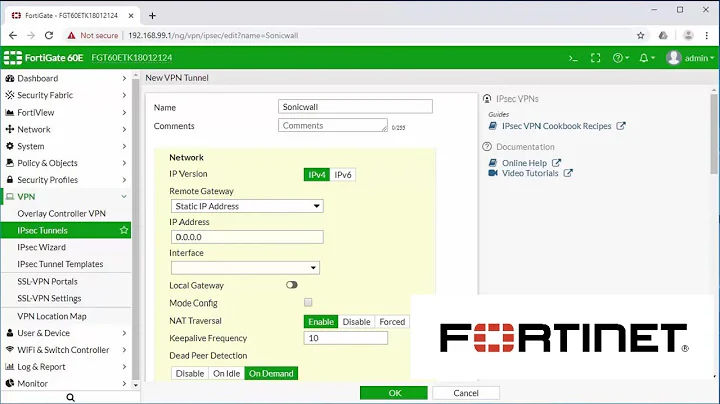
config vpn ipsec phase1-interface edit "iPhone_VPN" set type dynamic set interface "wan1" set dhgrp 2 set proposal 3des-sha1 3des-md5 set xauthtype auto set mode-cfg enable set authusrgrp "iPhone_VPN_Users" set ipv4-start-ip 10.10.99.100 set ipv4-end-ip 10.10.99.199 set ipv4-netmask 255.255.0.0 set ipv4-dns-server1 10.10.2.1 set ipv4-dns-server2 10.22.1.80 set ipv4-wins-server1 10.10.2.1 set ipv4-wins-server2 10.22.1.80 set ipv4-split-include "Dialup_VPN_Networks" set psksecret ENC xxxxx next endFor whatever reason, as far as I can tell, the iPhone does not 'see' the DNS or WINS entries. I don't know how to check it...
-
 Admin over 12 yearsHave you flushed the DNS cache of the iPhone? anyway I don't know that much iOS but you can try to check if there is some command similiar to: HOST DIG in the Unix world
Admin over 12 yearsHave you flushed the DNS cache of the iPhone? anyway I don't know that much iOS but you can try to check if there is some command similiar to: HOST DIG in the Unix world
-