iptables to allow only ssh and https
16,329
Do not block all the outbound rule, it will not choose port 443 as a source to get data from other server. And I think blocking inbound rules are pretty enough to ensure your server security. Rest is all Good. You can use below rules if you want.
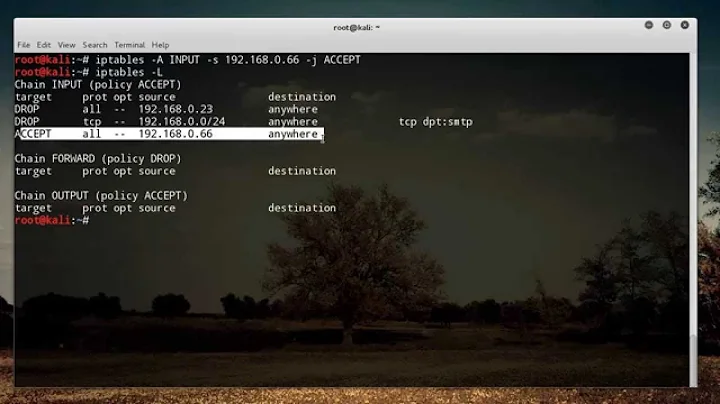
iptables -F
iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -i lo -j ACCEPT
iptables -A INPUT -p tcp --dport 22 -j ACCEPT
iptables -A INPUT -p tcp --dport 443 -j ACCEPT
iptables -A INPUT -p tcp -j DROP
Related videos on Youtube
Author by
wyr0
Updated on September 18, 2022Comments
-
wyr0 over 1 year
I'm trying to configure the iptables on my device in order to allow only SSH and HTTPS traffic. In particular, the HTTPS protocol is used to call some REST API toward a remote server from a java client.
This is my iptables:
iptables -F iptables -P INPUT DROP iptables -P OUTPUT DROP iptables -P FORWARD DROP #SSH iptables -A INPUT -p tcp -m tcp --dport 22 -j ACCEPT iptables -A OUTPUT -p tcp --sport 22 -m state --state ESTABLISHED -j ACCEPT #DNS iptables -A OUTPUT -p udp --dport 53 -j ACCEPT #HTTPS iptables -A OUTPUT -p tcp --sport 443 -j ACCEPT iptables -A INPUT -p tcp -m tcp --dport 443 -j ACCEPTEverything works as expected, except for HTTPS traffic, which is blocked by iptables.
What i made wrong?
-
user9517 about 8 yearsBlocked in or blocked out? The sport of an outbound connection will almost certainly not be 443.
-
 Michael Hampton about 8 yearsDo yourself a favor: 1. Don't write stateless firewalls. 2. If you don't know how to write a firewall from scratch, get a tool to generate it for you.
Michael Hampton about 8 yearsDo yourself a favor: 1. Don't write stateless firewalls. 2. If you don't know how to write a firewall from scratch, get a tool to generate it for you.
-
-
 Dylan Knoll about 8 yearsThis line is what you're missing OP: iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
Dylan Knoll about 8 yearsThis line is what you're missing OP: iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT