TCP connect: No route to host
Fedora is using firewalld service for port blocking/allowing
Use this command to find your active zone(s):
firewall-cmd --get-active-zones
It will say either public, dmz, or something else. You should only apply to the zones required.
In the case of public try:
firewall-cmd --zone=public --add-port=8000/tcp
if you want to make it permanent, try:
firewall-cmd --zone=public --add-port=8000/tcp --permanent
Otherwise, substitute dmz for your zone, for example, if your zone is public:
firewall-cmd --zone=public --add-port=2888/tcp --permanent
Then remember to reload the firewall for changes to take effect.
firewall-cmd --reload
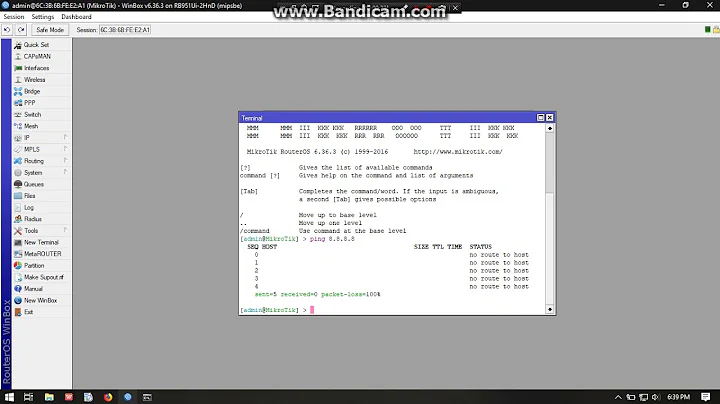
Related videos on Youtube
lily
Updated on September 18, 2022Comments
-
lily over 1 year
I started a tcp server on a host A and then start a tcp client on another host B.
Both hosts are in the same LAN via the wireless router at home. the tcp client tries to connect to tcp server on port 8000. but it failed due to " No route to host"
I can ping successfully the server host from the client host, and actually I'm ssh'ed into the server from the client now
If I swap the two hosts, namely I started the tcp server on the host B and then start the tcp client on the host A. then the TCP connection is successful
What is wrong with the server host A? the following link shows the results of iptables -L -n, ss -tlnp and netstat -lnp
http://paste.ubuntu.com/12785409/
and routing table on A:
# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.0.1 0.0.0.0 UG 0 0 0 wlan0 192.168.0.0 0.0.0.0 255.255.255.0 U 9 0 0 wlan0routing table on B:
# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.0.1 0.0.0.0 UG 0 0 0 wlan0 192.168.0.0 0.0.0.0 255.255.255.0 U 9 0 0 wlan0The related tcp client and server are: https://www.cs.cmu.edu/afs/cs/academic/class/15213-f99/www/class26/tcpserver.c
http://www.cs.cmu.edu/afs/cs/academic/class/15213-f99/www/class26/tcpclient.c
I tried
kill vpnagent process
# ps ax | grep vpnagent 1291 ? S 0:00 /opt/cisco/vpn/bin/vpnagentd 4202 pts/2 S+ 0:00 grep --color=auto vpnagent #sudo kill -9 1291and then
# service vpnagentd stop # sudo systemctl stop vpnagentdand I don't know is it due to this, last day, the connection suddenly become OK. But after I reboot, run the above commands to stop vpnagent service, the "No route to host" problem is still there
-
 teikjoon over 8 yearsIsn't port 8000 being blocked by the firewall rules? SSH is being allowed because there is a rule for it (port 22).
teikjoon over 8 yearsIsn't port 8000 being blocked by the firewall rules? SSH is being allowed because there is a rule for it (port 22). -
lily over 8 years@teikjoon wher e is blocking 8000? and how can I make it not block 8000?
-
lily over 8 years@MariusMatutiae ah, I have modified the links and you can check them now. they are source codes, not routing tables. what any other info should I provide to trouble-shoot the problem? thanks
-
lily over 8 years@ MariusMatutiae I have updated the routing table, is it right? thanks
-
-
balupton about 6 yearsWhat if
firewall-cmd --get-active-zonesreturns nothing? What to do?

![Zabbix agent Get value from agent failed cannot connect to [[IP]:10050]: [113]No route to host](https://i.ytimg.com/vi/q8yfMYVWt_Y/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBbWg8zhXnr7sCWyaNErjviTVPxpA)