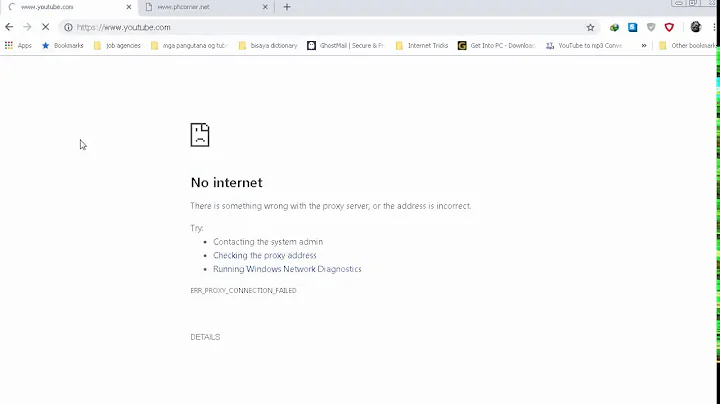
Openvpn connects and responds to ping but no internet access
5,023
Solution 1
OK, I solved the problem. There was a problem in the rules in iptables. I removed the first rule in the FORWARD chain and then I could ping external IP:s. I also changed the DNS server in server.conf to an external DNS-server and after that everything was working fine.
Solution 2
- Check routing on client, especially default route.
- if routing is correct, check (with
tcpdump,wiresharkor some other packet capture program) where packets are actually sent (check on both interfaces). - if packets are sent/received correctly - check if DNS is working (what DNS server client is trying to use and does DNS query/responese packets pass).
Related videos on Youtube
Author by
joakimb
Updated on September 18, 2022Comments
-
joakimb over 1 year
I have an openvpn server running on raspian and a tunnelblick client on osx. I can connect to the VPN just fine but I have no intenet access. The server responds to ping just fine and the port is open in the router. Does anyone know what might be wrong?
here is the client log: http://pastebin.com/zvBXPv4D
here is the server log: http://pastebin.com/bBsaRK6c
client config:
client dev tun proto udp remote <server external ip> 1194 #change this resolv-retry infinite nobind persist-key persist-tun mute-replay-warnings ns-cert-type server key-direction 1 cipher AES-128-CBC comp-lzo verb 1 mute 20 ca /Users/user1/vpn/ca.crt #change this cert /Users/user1/vpn/client1.crt #change this key /Users/user1/vpn/client1.key #change this <tls-auth> # # 2048 bit OpenVPN static key # -----BEGIN OpenVPN Static key V1----- #removed for pastebin -----END OpenVPN Static key V1----- </tls-auth>server config:
dev tun proto udp port 1194 ca /etc/openvpn/easy-rsa/keys/ca.crt cert /etc/openvpn/easy-rsa/keys/server.crt # SWAP WITH YOUR CRT NAME key /etc/openvpn/easy-rsa/keys/server.key # SWAP WITH YOUR KEY NAME dh /etc/openvpn/easy-rsa/keys/dh1024.pem # If you kept 1024, change it to dh1024.pem server 10.8.0.0 255.255.255.0 tls-auth /etc/openvpn/easy-rsa/keys/ta.key 0 # server and remote endpoints ifconfig 10.8.0.1 10.8.0.2 # Add route to Client routing table for the OpenVPN Server push "route 10.8.0.1 255.255.255.255" # Add route to Client routing table for the OpenVPN Subnet push "route 10.8.0.0 255.255.255.0" # your local subnet push "route 10.0.1.2 255.255.255.0" # Enter PI LAN PI # Set primary domain name server address to the SOHO Router # If your router does not do DNS, you can use Google DNS 8.8.8.8 push "dhcp-option DNS 10.8.0.1" # Override the Client default gateway by using 0.0.0.0/1 and # 128.0.0.0/1 rather than 0.0.0.0/0. This has the benefit of # overriding but not wiping out the original default gateway. push "redirect-gateway def1" client-to-client duplicate-cn keepalive 10 120 cipher AES-128-CBC comp-lzo user nobody group nogroup persist-key persist-tun status /var/log/openvpn-status.log 20 log /var/log/openvpn.log verb 5sysctl net.ipv4.ip_forward gives:
net.ipv4.ip_forward = 1ip route show gives:
default via 10.0.1.1 dev eth0 10.0.1.0/24 dev eth0 proto kernel scope link src 10.0.1.2 10.8.0.0/24 via 10.8.0.2 dev tun0 10.8.0.2 dev tun0 proto kernel scope link src 10.8.0.1iptables -L -v gives:
Chain INPUT (policy ACCEPT 15492 packets, 1793K bytes) pkts bytes target prot opt in out source destination 88 5861 ACCEPT all -- tun+ any anywhere anywhere 1 70 ACCEPT udp -- eth0 any anywhere anywhere state NEW udp dpt:openvpn Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 0 0 ACCEPT all -- tun0 eth0 10.8.0.0/24 10.0.1.0/24 ctstate NEW 13 948 ACCEPT all -- tun+ any anywhere anywhere 0 0 ACCEPT all -- tun+ eth0 anywhere anywhere state RELATED,ESTABLISHED 4 776 ACCEPT all -- eth0 tun+ anywhere anywhere state RELATED,ESTABLISHED Chain OUTPUT (policy ACCEPT 18526 packets, 3880K bytes) pkts bytes target prot opt in out source destination 27 2584 ACCEPT all -- any tun+ anywhere anywhere