OpenVPN routing between different subnets
Made it work :)
Seems you not only need the route, but also a client directive on the OpenVPN server which pushes an internal route to OpenVPN (iroute)
Replace with the common name in the certificate of the client and enable client directives in the server.conf of the OpenVPN server).
/etc/openvpn/ccd/
Content
ifconfig 192.168.200.7 255.255.255.0 #always configure client with static address
iroute 192.168.170.0 255.255.255.0 #behind this client is the subnet
See http://backreference.org/2009/11/15/openvpn-and-iroute/ :)
Related videos on Youtube
MMF
Updated on September 18, 2022Comments
-
MMF over 1 year
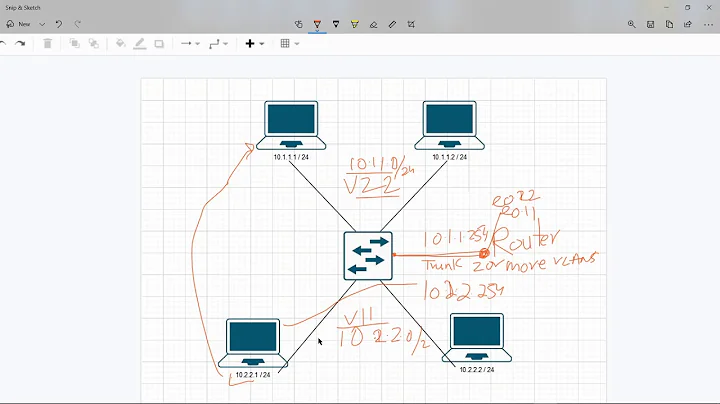
I have an issue with a complicated setup and I cannot wrap my head around it.
Please take a look at the drawing, it shows all involved components. Basically I am trying to NAT over two routers and one direction works, one doesn't.
Router 1 is an OpenWRT with two interfaces (lan and vpn) and Router 2 is a Ubuntu box.Architecture
Router 1 is an OpenVPN client and connects to Router 2 (OpenVPN server). The OpenVPN subnet is 192.168.200.0/24, the internal LAN on the left side 192.168.170.0/24 and 10.0.0.10/24 on the other side. Router 2 is also dual-homed, the second interface exposes the OpenVPN server (10.10.0.1).
The OpenWRT forwards in both zones and also masquerades in both directions.
config defaults option input 'ACCEPT' option output 'ACCEPT' option forward 'ACCEPT' config zone option name 'lan' option input 'ACCEPT' option output 'ACCEPT' option forward 'ACCEPT' option masq '1' option mtu_fix '1' option network 'lan' config include option path '/etc/firewall.user' config rule option target 'ACCEPT' option name 'Any - Any - All' option src '*' option dest '*' option proto 'all' config zone option name 'vpn' option output 'ACCEPT' option input 'ACCEPT' option forward 'ACCEPT' option masq '1' option mtu_fix '1' option network 'OpenVPN' config forwarding option dest 'lan' option src 'vpn' config forwarding option dest 'vpn' option src 'lan'The iptables config of Router 2 is as follows:
iptables -F iptables -X iptables -t nat -F iptables -A FORWARD -i eth1 -o eth0 -m conntrack --ctstate NEW -j ACCEPT iptables -A FORWARD -i eth1 -o tun0 -m conntrack --ctstate NEW -j ACCEPT iptables -A FORWARD -i tun0 -o eth1 -m conntrack --ctstate NEW -j ACCEPT iptables -A FORWARD -i tun0 -o eth0 -m conntrack --ctstate NEW -j ACCEPT iptables -A FORWARD -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPTAnd it also routes:
net.ipv4.ip_forward=1I am pushing the route to the network 192.168.170./24 on Router2.
route add -net 192.168.170./24 dev tun0The outcome:
The left server 192.168.170.10 can ping the right server 10.0.0.10 and I have full connectivity from left to right.
Router 2 (192.168.200.1) can ping Router 1's VPN IP 192.168.200.7 and vice versa. The right server 10.0.0.10 cannot ping the left one 192.168.170.10 and I have no connectivity from right to left - but I can ping Router 1's VPN IP 192.168.200.7.
And that's my problem. I need transparent masquerading in both directions. And I am not sure, where my problem is :(
Thanks!
-
MMF over 7 yearsI already tried that, but I cannot even route to the network :( 192.168.170.0 192.168.200.1 255.255.255.0 UG 0 0 0 tun0
-
 Ipor Sircer over 7 yearsI think your 10.0.0.10 machine doesn't have
Ipor Sircer over 7 yearsI think your 10.0.0.10 machine doesn't havetun0interface. Add routing on that machine. ( Usetcpdumporwiresharkto solve the problem. ) -
MMF over 7 yearsYes, the 10.0.0.10 has no tun0, and it only routes to its default gateway. The router should take care of this (Linux box). Thanks for your help! I will tcpdump this on both routers.