PAM / LDAP authentication with Ubuntu 10.04
Solution 1
Restore you pam files to the original versions. Install the libnss-ldap package which will integrate ldap access into pam. You may also want to install nscd.
Configure your server in /etc/ldap.conf.
Edit /etc/nsswitch.conf adding ldap to the end of the lines for passwd group and shadow.
passwd: compat ldap group: compat ldap shadow: compat ldap
Check to see if 'sudo getent shadow' is working for ldap entries. Check that you can get an authenticated connection using ldap-search from ldap-utils using your /etc/ldap.conf connection data.
Depending on your configuration you will also have to configure ssl values in /etc/ldap.conf.
Solution 2
- Firstly, you'll need to open up your favourite package manager and install libpam-ldap
- Once the packages start being unpacked you'll be hit up for a few questions about:
. IP address/hostname of the LDAP server
. The search base of your LDAP domain etc... - Now you need to customise PAM to make it use LDAP for authentication:
sudo vi /etc/pam.d/login - you need to add one line above the existing line:
- Once the packages start being unpacked you'll be hit up for a few questions about:
auth sufficient pam_ldap.so
auth required pam_unix.so try_first_pass
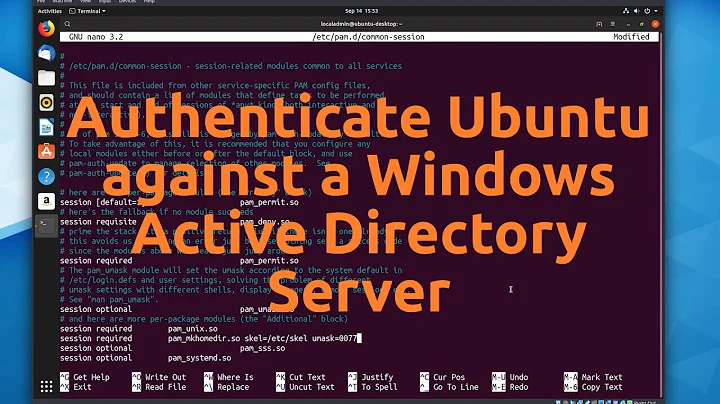
Or modified the common-auth file
Related videos on Youtube
t6d
Updated on September 17, 2022Comments
-
t6d almost 2 years
I can't wrap my brain around the new pam.d configuration syntax used in Ubuntu 10.04. How do I setup PAM so that it allows users stored in my LDAP database to login.
I already configured nscd, so
id <user>orgetent passwdare already listing my LDAP users, but PAM doesn't work, whether the normal shell login norsu.Update June, 17th 2010 18:45
LDAP is already working. I can list all accounts by executing
getent passwd, but my PAM configuration is still not working.The listing below shows my /etc/pam.d/login
# # The PAM configuration file for the Shadow `login' service # # Enforce a minimal delay in case of failure (in microseconds). # (Replaces the `FAIL_DELAY' setting from login.defs) # Note that other modules may require another minimal delay. (for example, # to disable any delay, you should add the nodelay option to pam_unix) auth optional pam_faildelay.so delay=3000000 # Outputs an issue file prior to each login prompt (Replaces the # ISSUE_FILE option from login.defs). Uncomment for use # auth required pam_issue.so issue=/etc/issue # Disallows root logins except on tty's listed in /etc/securetty # (Replaces the `CONSOLE' setting from login.defs) # Note that it is included as a "required" module. root will be # prompted for a password on insecure ttys. # If you change it to a "requisite" module, make sure this does not leak # user name information. auth required pam_securetty.so # Disallows other than root logins when /etc/nologin exists # (Replaces the `NOLOGINS_FILE' option from login.defs) auth requisite pam_nologin.so # SELinux needs to be the first session rule. This ensures that any # lingering context has been cleared. Without out this it is possible # that a module could execute code in the wrong domain. # When the module is present, "required" would be sufficient (When SELinux # is disabled, this returns success.) session [success=ok ignore=ignore module_unknown=ignore default=bad] pam_selinux.so close # This module parses environment configuration file(s) # and also allows you to use an extended config # file /etc/security/pam_env.conf. # # parsing /etc/environment needs "readenv=1" session required pam_env.so readenv=1 # locale variables are also kept into /etc/default/locale in etch # reading this file *in addition to /etc/environment* does not hurt session required pam_env.so readenv=1 envfile=/etc/default/locale # Standard Un*x authentication. @include common-auth # This allows certain extra groups to be granted to a user # based on things like time of day, tty, service, and user. # Please edit /etc/security/group.conf to fit your needs # (Replaces the `CONSOLE_GROUPS' option in login.defs) auth optional pam_group.so # Uncomment and edit /etc/security/time.conf if you need to set # time restrainst on logins. # (Replaces the `PORTTIME_CHECKS_ENAB' option from login.defs # as well as /etc/porttime) # account requisite pam_time.so # Uncomment and edit /etc/security/access.conf if you need to # set access limits. # (Replaces /etc/login.access file) # account required pam_access.so # Sets up user limits according to /etc/security/limits.conf # (Replaces the use of /etc/limits in old login) session required pam_limits.so # Prints the last login info upon succesful login # (Replaces the `LASTLOG_ENAB' option from login.defs) session optional pam_lastlog.so # Prints the motd upon succesful login # (Replaces the `MOTD_FILE' option in login.defs) session optional pam_motd.so # Prints the status of the user's mailbox upon succesful login # (Replaces the `MAIL_CHECK_ENAB' option from login.defs). # # This also defines the MAIL environment variable # However, userdel also needs MAIL_DIR and MAIL_FILE variables # in /etc/login.defs to make sure that removing a user # also removes the user's mail spool file. # See comments in /etc/login.defs session optional pam_mail.so standard # Standard Un*x account and session @include common-account @include common-session @include common-password # SELinux needs to intervene at login time to ensure that the process # starts in the proper default security context. Only sessions which are # intended to run in the user's context should be run after this. session [success=ok ignore=ignore module_unknown=ignore default=bad] pam_selinux.so open # When the module is present, "required" would be sufficient (When SELinux # is disabled, this returns success.)The listing below shows my /etc/pam.d/common-auth
# # /etc/pam.d/common-auth - authentication settings common to all services # # This file is included from other service-specific PAM config files, # and should contain a list of the authentication modules that define # the central authentication scheme for use on the system # (e.g., /etc/shadow, LDAP, Kerberos, etc.). The default is to use the # traditional Unix authentication mechanisms. # # As of pam 1.0.1-6, this file is managed by pam-auth-update by default. # To take advantage of this, it is recommended that you configure any # local modules either before or after the default block, and use # pam-auth-update to manage selection of other modules. See # pam-auth-update(8) for details. # here are the per-package modules (the "Primary" block) auth [success=2 default=ignore] pam_unix.so nullok_secure auth [success=1 default=ignore] pam_ldap.so use_first_pass # here's the fallback if no module succeeds auth requisite pam_deny.so # prime the stack with a positive return value if there isn't one already; # this avoids us returning an error just because nothing sets a success code # since the modules above will each just jump around auth required pam_permit.so # and here are more per-package modules (the "Additional" block) # end of pam-auth-update config-
Shtééf about 14 yearsYour
common-authlooks correct. Perhaps the problem is somewhere else? Is there anything in/var/log/auth.log? Check some other logs too, such assyslog,messages,user.loganddaemon.log. Are there any other LDAP-related files you've edited? Did you configure any authentication or access control on the LDAP server?
-
-
t6d about 14 yearsI guess I messed up my configuration. I tried again by installing the packages and configuring /etc/nsswitch.conf, and see, it works! Great, thanks a lot.