Permissionless external drive with NTFS
Solution 1
Your external drive is formatted with the NTFS file system, which supports access restrictions.
Unfortunately, while some users and security groups are built-in to Windows with predefined Security IDs which are the same on all machines (such as Everyone), other users and groups have SIDs derived from the machine they're defined on.
To normalize the situation you should:
- While logged-in as Administrator, right-click the drive's root directory and select Properties.
- Click the Security tab, then the Advanced button.
- In the Advanced Security Settings dialog for the drive, click the Owner tab, then the Edit button.
- Click the Administrators group, check Replace owner on subcontainers and objects and click OK. If asked about replacing existing permissions with ones giving you Full Control, click Yes.
- Back in the Security tab and on the original Properties sheet again, click the Edit button, and in the Security dialog click Remove for all entries for all accounts listed under "Group or user names", except for the well-known ones of System, Administrators, Users and Authenticated Users.
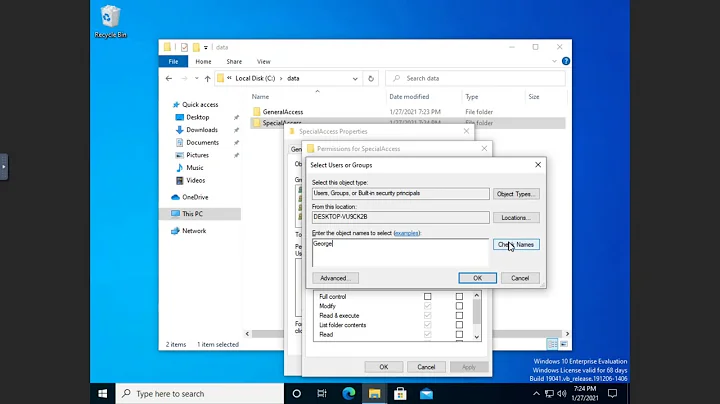
- Click Add, and in the "Select Users,
Computer or Groups" dialog under
"Enter the object names to select",
type
Everyoneand click OK. You should verify thatEveryonehas been added to the list. - Click Everyone, check Full Control, then click on Apply.
- Click Advanced again to go back to the Advanced Security Settings dialog box and click the Change Permissions button. Check Replace permission entries on all child objects and click OK and OK.
- Click OK.
Be careful in the future not to allocate separate access permissions to sub-folders of the drive (leaving all permissions as inherited). If this happens again, repeat the step for "Replace permission entries on all child objects".
Be mindful of the fact that under Windows 7/8 the Guest account is not part of the Everyone group. If you need it, you'll have to add Guest as above for the Everyone group.
If you encounter problems with UAC, try using Explorer via "Run as administrator".
Solution 2
The example above:
takeown /f f:\ /r /d y
will assign owner to the current user. To assign owner to the administrators group add the /a option, For example:
takeown /f f:\ /a /r /d y
This will accomplish steps 1-4 of harrymc's solution.
Note that /d y is localisation dependent, with German localisation it is e.g. /D j.
Solution 3
takeown is the easiest tool to get rid of this braindamaged permission system.
start a cmd as administrator (right-click cmd icon, run as admin), and enter
takeown /f [root dir of drive] /r /d y
example for drive F:
c:\>takeown /f f:\ /r /d y
Related videos on Youtube
malejpavouk
Updated on September 17, 2022Comments
-
 malejpavouk almost 2 years
malejpavouk almost 2 yearsI am currently trying to implement RDFa breadcrumbs to my webpages. I think that I am following the example for multiple breadcrumbs on one page correctly, however in the testing tool and search results the breadcrumbs are not processed as expected (are extracted, but the breadcrumbs are not displayed).
Can you plese give me a hint what am I doing wrong.
Thanks.
<div class="breadCrumb"> <span typeof="v:Breadcrumb"> <a href="/" ref="v:url" property="v:title">Algoritmy.net</a> > <span rel="v:child"> <span typeof="v:Breadcrumb"> <a ref="v:url" property="v:title" href="/category/39974/Mathematics">Mathematics</a> > <span rel="v:child"> <span typeof="v:Breadcrumb"> <a ref="v:url" property="v:title" href="/category/48669/Primality">Primality</a> > <span rel="v:child"> <span typeof="v:Breadcrumb"> <a href="/article/47455/Rabin-Miller-test" ref="v:url" property="v:title">Rabin-Miller test</a> </span> </span> </span> </span> </span> </span> </span> </div> -
jtreser about 14 yearsThe above is the correct solution and really the only easy way to deal with external NTFS drives that may used by multiple user accounts or on different machines. If there are files you want private you can always use something like TrueCrypt to make a folder and it's contents private.
-
afrazier about 14 years+1 - "Everyone Full Control" or "Administrators Full Control / Users Modify" is the easiest way around this. Beyond that, it's a matter of making sure something doesn't decide to mess with the ACLs.
-
kahen almost 13 yearsUAC... my sworn enemy. 2 reboots later and a
takeown /f e:\ /r /d ylater, and everything is in order again. -
 Andreas Spindler about 11 yearsA radical solution is to TrueCrypt the drive in FAT32 and suffer the limitations. As there are no ACLs under FAT32 it is g'teed you can access your files on virtually any machine... your home and work Windows PCs, Linux, OS X, and unless encrypted, even your phone and TV/SAT receiver. It's a shame that M$ made it so hard to attach memory even to simple Windows PCs. Really a crude and unfriendly design.
Andreas Spindler about 11 yearsA radical solution is to TrueCrypt the drive in FAT32 and suffer the limitations. As there are no ACLs under FAT32 it is g'teed you can access your files on virtually any machine... your home and work Windows PCs, Linux, OS X, and unless encrypted, even your phone and TV/SAT receiver. It's a shame that M$ made it so hard to attach memory even to simple Windows PCs. Really a crude and unfriendly design. -
Chris Chilvers almost 11 yearsWatch out for things like junctions in Windows Vista/7, it ended up recursing in to
F:\Documents And Settingsfor me, which linked toC:\Users. -
Jon Bentley over 10 yearsAt step 7, I get, "An error occured while applying security information to: <file name>... Access is denied.". This pops up for every single file on the drive until I click cancel.
-
 harrymc over 10 years@JonBentley: You probably have problems with UAC. Try using Explorer via "Run as administrator".
harrymc over 10 years@JonBentley: You probably have problems with UAC. Try using Explorer via "Run as administrator". -
Jon Bentley over 10 years@harrymc Thanks, that solves the problem. Might be worth adding that to the answer.
-
Ikus over 9 yearsI can set the owner of files to Everyone as well. Just wondering whether this is a good idea? Because even the local administrator group won't exist on another machine, I guess. And who will be the owner of new files added on another machine, will it be inherited, too?
-
Holistic Developer almost 8 years@ygoe The Administrators group has what is known as a "well-known SID" (security identifier) so it is the same on every Windows computer. Assigning it as the owner means it will apply to any machine to which the drive is connected in the future. See support.microsoft.com/en-us/kb/243330.
-
 Brethlosze about 7 yearsI have a doubt... it should be
Brethlosze about 7 yearsI have a doubt... it should beAdministratorsorEveryone?. OrAdministratorsas the owner andEveryonein the permissions?. Or it is the same?. What about if i plug this disk into a Linux or a Mac OS system?.. it will be able to recognize theAdministratorsor theEveryoneSIDs? -
 Brethlosze about 7 years+1 with opening a 'cmd.exe' as "Run as Administrator", through
Brethlosze about 7 years+1 with opening a 'cmd.exe' as "Run as Administrator", throughdiskmgmt.msccommand. Just changing directly often dont do anything. I thinks that is one of the major caveats in all of this. -
 Scott - Слава Україні over 6 years(1) You say “I'd advise opening it as administrator if possible”. Is there any possibility that this command could succeed if run by a non-privileged user? (2) You say “This will keep the NTFS format but convert security on all files & folders to allow access by all users.” Does that apply to files that are created in the future?
Scott - Слава Україні over 6 years(1) You say “I'd advise opening it as administrator if possible”. Is there any possibility that this command could succeed if run by a non-privileged user? (2) You say “This will keep the NTFS format but convert security on all files & folders to allow access by all users.” Does that apply to files that are created in the future? -
laggingreflex over 6 yearsHow long does it take? Is it quicker than resursive
takeown? -
 harrymc over 6 years
harrymc over 6 yearsconvert /NoSecuritywill need to be run again on each use, and administrator permissions may be required as it locks the disk. For exFAT: The convert command description says: "Volumes converted to the NTFS file system cannot be converted back to FAT or FAT32", so because exFAT is just FAT64, it might not be possible to convert NTFS to exFAT. -
greenlungus about 3 yearsFor me on Windows 10, when the drive is already NTFS, the command just says
Drive X: is already NTFS.So it looks like the command is not suitable for adjusting security settings on an existing NTFS drive. @harrymc What do you mean with "will need to be run on each use again"? Did the utility behave differently in past versions?