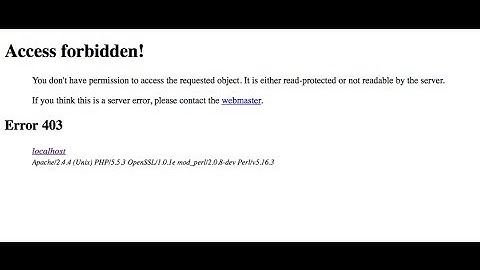
PUT request results in 403 Forbidden - Need Apache to allow PUT requests
Solution 1
Add this to the .htaccess file in this folder
-- For Apache 2.2
<Limit GET POST PUT OPTIONS DELETE PATCH HEAD>
Order allow,deny
Allow from all
</Limit>
<LimitExcept GET POST PUT OPTIONS DELETE PATCH HEAD>
Order deny,allow
Deny from all
</LimitExcept>
-- For Apache 2.4
<Limit GET POST PUT OPTIONS DELETE PATCH HEAD>
Require all granted
</Limit>
<LimitExcept GET POST PUT OPTIONS DELETE PATCH HEAD>
Require all denied
</LimitExcept>
Note: you can remove methods which you dont want
Solution 2
At least with the last Apache's version (2.4.38) with modsecurity enabled, only these methods are allowed by default: GET HEAD POST OPTIONS
When a PUT request is made the error log of Apache2 returns this message:
[Wed May 06 11:46:56.680835 2020] [:error] [pid 20162] [client 172.16.x.x:58147] [client 172.16.12.144] ModSecurity: Warning. Match of "within %{tx.allowed_methods}" against "REQUEST_METHOD" required. [file "/usr/share/modsecurity-crs/rules/REQUEST-911-METHOD-ENFORCEMENT.conf"] [line "46"] [id "911100"]
[msg "Method is not allowed by policy"] [data "PUT"] [severity "CRITICAL"] [ver "OWASP_CRS/3.1.0"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-generic"] [tag "OWASP_CRS/POLICY/METHOD_NOT_ALLOWED"] [tag "WASCTC/WASC-15"] [tag "OWASP_TOP_10/A6"] [tag "OWASP_AppSensor/RE1"] [tag "PCI/12.1"] [hostname "192.168.x.x"] [uri "/app/api/widgets/grid"] [unique_id "XrKHkEqec4EieQ@yCDCkkQAAABI"], referer: https://192.168.x.x/app
The best way to solve it is changing this policy in modsecurity, so edit the file "/etc/modsecurity/crs/crs-setup.conf" and uncomment the following lines adding PUT as allowed:
SecAction \
"id:900200,\
phase:1,\
nolog,\
pass,\
t:none,\
setvar:'tx.allowed_methods=GET HEAD POST OPTIONS PUT DELETE'"
Solution 3
Edit:
Add this to your Apache conf:
Script PUT /api/index.php
This assumes your actual handler script is called index.php and it's located on /api.
Related videos on Youtube
mmattax
I have a BS in Computer Science from Purdue University. My main interests are in open source, platform agnostic tools and software.
Updated on September 18, 2022Comments
-
mmattax almost 2 years
I am building a RESTFUL API and need to get Apache to accept PUT requests. Whenever I put to a URL, I am getting a
403 Forbiddenerror.curl -X PUT api.example.com/api/foo
I have tried to add the following to my Virtual Directory (To no avail):
<Limit GET POST PUT DELETE HEAD OPTIONS> Order allow,deny Allow from all </Limit> <LimitExcept GET POST PUT DELETE HEAD OPTIONS> Order deny,allow Deny from all </LimitExcept>What other config settings might be causing this?
EDIT
I am re-writing my URL's, all get re-written to index.php as follows:
RewriteEngine On RewriteCond %{REQUEST_FILENAME} !-f RewriteCond %{REQUEST_FILENAME} !-d RewriteCond %{REQUEST_FILENAME} !\. RewriteRule ^(.*)$ /api/index.php/$1 [L,QSA] -
mmattax about 13 yearsI updated my post with the mod_rewrite info, if I make the PUT request directly to the PHP script it returns 403 as well.
-
ravi yarlagadda about 13 yearsSounds like Apache's allowing the request just fine, but the PHP is spitting out the 403.
-
Eduardo Ivanec about 13 yearsWhat @Shane said. Can you GET it?
-
mmattax about 13 yearsYes, GET and POST work fine. Could it be PHP even though the error page being served is Apache's?
-
Eduardo Ivanec about 13 yearsI think I was wrong - try making the change in my edit.
-
 HBruijn almost 9 yearsAre you certain your
HBruijn almost 9 yearsAre you certain yourRequireDirective syntax was already valid for Apache 2.2 (see the tag in the question) because as far as I knowRequire allwas introduced with Apacge 2.4 -
 tisc0 over 6 yearsWorks great in centos7 / Apache 2.4 / Prestashop webservices context, since some methods are forbidden by default (it wasn't in 2.2/Debian). @HBruijn : Limit and LimitExcept are in the official Apache 2.2 documentation, so it should also work with the adapted syntax (httpd.apache.org/docs/2.2/en/mod/core.html#limit).
tisc0 over 6 yearsWorks great in centos7 / Apache 2.4 / Prestashop webservices context, since some methods are forbidden by default (it wasn't in 2.2/Debian). @HBruijn : Limit and LimitExcept are in the official Apache 2.2 documentation, so it should also work with the adapted syntax (httpd.apache.org/docs/2.2/en/mod/core.html#limit). -
Stefan S almost 4 yearsThank you, this led my to the issue. I would never have thought for the modsecurity module
-
 CodeGodie over 2 yearsThis helped me as well. Along with this post in cpanel forums.cpanel.net/threads/…
CodeGodie over 2 yearsThis helped me as well. Along with this post in cpanel forums.cpanel.net/threads/…
![How to Fix The 403 Forbidden Error [Step by Step] ☑️](https://i.ytimg.com/vi/ob6ySsAEzZk/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLDr1V11KKapIaGZYhQsQ-tJ9par-Q)