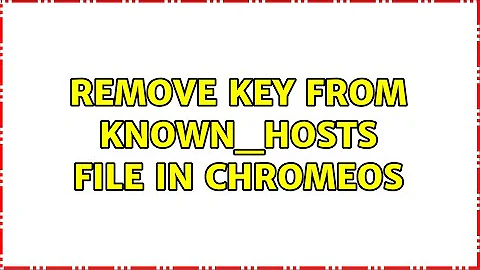
Remove key from known_hosts
Solution 1
sed -i '6d' ~/.ssh/known_hosts
Will modify the file ~/.ssh/known_hosts:6 , removing the 6th line.
In my opinion, using ssh-keygen -R is a better solution for an openssh power user, while your regular Linux admin would do better to keep his/her sed skills fresh by using the above method.
Solution 2
The simplest solution is:
rm -f .ssh/known_hosts
ssh will recreate the file again, but you lose key checking for other hosts!
Or, you can use:
ssh-keygen -R "hostname"
Or the ssh "man-in-the-middle" message should indicate which line of the known_hosts file has the offending fingerprint. Edit the file, jump to that line and delete it.
Solution 3
There is an ssh-keygen switch (-R) for this.
man ssh-keygen reads:
-RhostnameRemoves all keys belonging to
hostnamefrom aknown_hostsfile. This option is useful to delete hashed hosts (see the-Hoption above).
Solution 4
You need to run the following command to get rid of this problem. Open the terminal and type the following command:
For all examples below just replace the value after -R:
ssh-keygen -R server-name
ssh-keygen -R server.ip.addre.ss
ssh-keygen -R 202.54.1.5
ssh-keygen -R server1.example.com
Solution 5
All answers are good, but for real SSH pro we have missing information how to remove ssh signature with (non-standard) port number.
Simple SSH host signature remove command:
ssh-keygen -R example.comComplex ssh key remove, e.g. you connect to ssh on non standard port 222:
ssh example.com -p 222
and you get warning, and to remove this, you need to use square brackets colon port number:
ssh-keygen -R [example.com]:222
Note, that probably there will be IP record for the same host, so you will need to remove that one also.
Hope this helps for non-standard configuration users.
Related videos on Youtube
Adam Matan
Team leader, developer, and public speaker. I build end-to-end apps using modern cloud infrastructure, especially serverless tools. My current position is R&D Manager at Corvid by Wix.com, a serverless platform for rapid web app generation. My CV and contact details are available on my Github README.
Updated on September 17, 2022Comments
-
 Adam Matan over 1 year
Adam Matan over 1 yearI built several virtual machines during the last few weeks. The problem is, the
.ssh/known_hostsgives me the Man in the middle warning. This happens because another fingerprint is associated with the virtual machine IP.In the
.ssh/known_hostsfile, however, I don't find the record related to the IP, only two bizarre, key-like strings and "ssh-rsa".Does anyone have any ideas about how to remove the old key from
known_hosts?-
Deebster almost 10 yearsThe "bizarre, key-like strings" you refer to are the hashed hosts/ip addresses. This a security feature which helps stops an intruder from knowing which systems you have access to. If you see this then your ssh_config has
HashKnownHosts yesset. -
Daniel B almost 6 yearsIf you feel the file contents are too confusing, you probably have line-wrapping activated. Deactivate it. All lines start with a host name or an IP address.
-
-
 Adam Matan over 14 yearsCorrect - the line number is somewhat shy : "Add correct host key in /home/adam/.ssh/known_hosts to get rid of this message. Offending key in /home/udi/.ssh/known_hosts:48". Removed line 48 and it worked!
Adam Matan over 14 yearsCorrect - the line number is somewhat shy : "Add correct host key in /home/adam/.ssh/known_hosts to get rid of this message. Offending key in /home/udi/.ssh/known_hosts:48". Removed line 48 and it worked! -
user1686 over 14 years
ssh-keygen -R hostnamewill work too. -
 Andy Lester almost 14 yearsWhat's the benefit of this over doing it in any given text editor? Is there some reason not to do it that way, like how sudoers has to be edited with visudo?
Andy Lester almost 14 yearsWhat's the benefit of this over doing it in any given text editor? Is there some reason not to do it that way, like how sudoers has to be edited with visudo? -
Andre Holzner about 13 yearsThanks for mentioning
ssh-keygen -R. I just wanted to remove a host fromknown_hostsfor testing purposes (i.e. without that the host key changed) and this hosts entry was hashed... -
 flickerfly almost 11 yearsWhat distros come with this? Ubuntu doesn't seem to have it.
flickerfly almost 11 yearsWhat distros come with this? Ubuntu doesn't seem to have it. -
grosser almost 11 yearsThe benefit is that it's automated and quick / it's a separate binary you add yourself
-
chicken about 10 yearsThis is the easiest and safest method.
-
shgnInc about 10 yearsIf we remove that file, other keys will remove too.
-
kraxor almost 10 yearsRemoving the file is a bad advice, it's like telling someone to buy a new PC because the old one has a broken mouse. Manually editing a file that can be edited by an official application is also a bad idea. The
ssh-keygenoption was added because of a comment, but with no explanation. I don't think this answer deserves so many upvotes. -
kraxor almost 10 yearsWhat a horrible idea. Permanently disable a layer of security just because you're too lazy keeping your
~/.ssh/known_hostsup-to-date? Why not just go ahead and usetelnet? "whenever you are sure" - if you are ever sure, then you have no idea what a MITM attack is and you should probably spend some time reading some good literature. -
kraxor almost 10 yearsYou could have just posted your script here instead of linking your own blog entry that you created on the day you posted this answer. This qualifies as spam IMHO. Not to mention that you could create a simple alias to achieve the same result, no need for a 7 lines long ruby script.
-
Olivier Dulac about 9 years-1 because of the whole "delete the whole known_hosts file" first lines. This is a terrible, terrible, terrible thing to propose, and should be edited out.
-
 Rick Chatham over 8 yearsBased on the OP's question I think this is a valid answer. Sometimes you have a test system that you're creating/destroying a lot of VMs on. (I'm doing this right now as I prep for the RHCE exam.) There might not be any security implications. While noting the security implications is great, I don't think this has to be labeled a "horrible idea".
Rick Chatham over 8 yearsBased on the OP's question I think this is a valid answer. Sometimes you have a test system that you're creating/destroying a lot of VMs on. (I'm doing this right now as I prep for the RHCE exam.) There might not be any security implications. While noting the security implications is great, I don't think this has to be labeled a "horrible idea". -
 Rick Chatham over 8 yearsI don't see how editing the file directly in VIM is "unsafe". It's based on your comfort level with VIM. Especially with this file, the biggest risk you have is deleting too many keys, in which case you'll just get prompted again.
Rick Chatham over 8 yearsI don't see how editing the file directly in VIM is "unsafe". It's based on your comfort level with VIM. Especially with this file, the biggest risk you have is deleting too many keys, in which case you'll just get prompted again. -
Ryan Griggs over 8 yearsThe "safety" I was referring to involves 1) forgetting/not knowing to remove dependent info in other files (if any) and 2) Accidentally deleting more or less than needs to be, thus breaking the file.
-
 Blake Frederick almost 8 yearsThis solution is overkill. Just remove the offending line. That's it.
Blake Frederick almost 8 yearsThis solution is overkill. Just remove the offending line. That's it. -
Burgi almost 8 yearsThis method has already been suggested in the previous answers. Could you expanded upon what is different in your answer?
-
michael over 7 years"if you have an official application for that" => both
ssh-keygen -Randsed -i {line}dare pretty "official", and both will work for the foreseeable future. Util ssh-keygen allows removal by line number, both are perfectly acceptable (because, line numbers are often easier to deal with, and less error prone, than dealing with modern data center host-names). -
michael over 7 yearsrelated: superuser.com/a/1126243/73961
-
 hello_there_andy about 7 yearsAre newest known_hosts added on the top line or bottom?
hello_there_andy about 7 yearsAre newest known_hosts added on the top line or bottom? -
Jiri Klouda over 6 yearsNote: This will change the permissions of the known_hosts file to 0600. If you have a shared known_hosts file for any reason, this could disable the sharing of it.
-
Yitz over 6 years@Burgi - this answer gives more detail about the syntax of
ssh-keygen -Rthan any of the other answers so far. It show by example exactly what you can write after-R. So this answer is worthwhile, even though it is not a totally new answer. -
Burgi over 6 years@Yitz My comment was made as part of review. At the time (18 months ago) I thought the question needed a little help to make it even better.
-
barlop about 6 yearsA)The deletion of specifically the 6th line, is all very "look no hands". No explanation at all as to what is significant about the 6th line of the file?! B)Also
man ssh-keygenmentionsssh-keygen -R hostnameyou've just saidssh-keygen -Rwith no hostname specified, and you haven't explained what you mean by that. -
Pysis over 5 yearsand the correct one. Also, I had to do
[localhost]:port, using the brackets because I used a custom port I guess =/. Like others have said, I would also use the no SSH key-checking approach for my transient/test system development. -
 rubynorails over 4 yearsor just add this to your ~/.bashrc:
rubynorails over 4 yearsor just add this to your ~/.bashrc:sshdel() { sed -i "${@}d" ~/.ssh/known_hosts; }and call it withsshdel [line number]. no ruby, no binary, no worries. -
Nux over 4 yearsThis removes all ocurences so the best way. You can add new key with:
ssh-keyscan -H my.ssh.server.example.com >> ~/.ssh/known_hosts; -
redbandit almost 4 yearsadding an example would add great value to this post
-
 jtessier72 about 2 yearsThis answer could be improved by placing the good advice at the top, and then presenting the other option as an "if all else fails" option.
jtessier72 about 2 yearsThis answer could be improved by placing the good advice at the top, and then presenting the other option as an "if all else fails" option. -
 Admin almost 2 yearsWhen we aren't using default SSH port, then the hostname for
Admin almost 2 yearsWhen we aren't using default SSH port, then the hostname for-Rshould be provided with the following format'[<host-name OR IP>]:<SSH Port>'. For example:ssh-keygen -f ~/.ssh/known_hosts -R '[192.168.23.2]:1234'