Samba use freeipa auth for windows clients accessing cifs share
After 8 months, I finally solved the problem!
Samba share with freeipa auth
The complete set of information is at https://bgstack15.wordpress.com/2017/05/10/samba-share-with-freeipa-auth/.
On the freeipa controller:
yum -y install ipa-server-trust-ad
ipa-adtrust-install --add-sids
After running the --add-sids, users need to reset their passwords, in order for freeipa to generate the ipaNTHash value of their passwords.
On the samba server:
yum -y install ipa-server-trust-ad
Open the firewall ports it asks for (TCP 135,138,139,445,1024-1300; UDP 138,139,389,445)
Allow samba to read passwords
ipa permission-add "CIFS server can read user passwords" \
--attrs={ipaNTHash,ipaNTSecurityIdentifier} \
--type=user --right={read,search,compare} --bindtype=permission
ipa privilege-add "CIFS server privilege"
ipa privilege-add-permission "CIFS server privilege" \
--permission="CIFS server can read user passwords"
ipa role-add "CIFS server"
ipa role-add-privilege "CIFS server" --privilege="CIFS server privilege"
ipa role-add-member "CIFS server" --services=cifs/host2.vm.example.com
Prepare samba conf and restart samba.
tf=/etc/samba/smb.conf
touch "${tf}"; chmod 0644 "${tf}"; chown root:root "${tf}"; restorecon "${tf}"
cat < "${tf}"
[global]
debug pid = yes
realm = VM.EXAMPLE.COM
workgroup = VM
domain master = Yes
ldap group suffix = cn=groups,cn=accounts
ldap machine suffix = cn=computers,cn=accounts
ldap ssl = off
ldap suffix = dc=vm,dc=example,dc=com
ldap user suffix = cn=users,cn=accounts
log file = /var/log/samba/log
max log size = 100000
domain logons = Yes
registry shares = Yes
disable spoolss = Yes
dedicated keytab file = FILE:/etc/samba/samba.keytab
kerberos method = dedicated keytab
#passdb backend = ipasam:ldapi://%2fvar%2frun%2fslapd-VM-EXAMPLE-COM.socket
#passdb backend = ldapsam:ldapi://%2fvar%2frun%2fslapd-VM-EXAMPLE-COM.socket
passdb backend = ipasam:ldap://host2.vm.example.com ldap://host1.vm.example.com
security = USER
create krb5 conf = No
rpc_daemon:lsasd = fork
rpc_daemon:epmd = fork
rpc_server:tcpip = yes
rpc_server:netlogon = external
rpc_server:samr = external
rpc_server:lsasd = external
rpc_server:lsass = external
rpc_server:lsarpc = external
rpc_server:epmapper = external
ldapsam:trusted = yes
idmap config * : backend = tdb
ldap admin dn = cn=Directory Manager
[homes]
comment = Home Directories
valid users = %S, %D%w%S
browseable = No
read only = No
inherit acls = Yes
EOFCONF
systemctl restart smb.service
Related videos on Youtube
bgStack15
IT professional. #movingtogitlab: I am now on gitlab.
Updated on September 18, 2022Comments
-
 bgStack15 almost 2 years
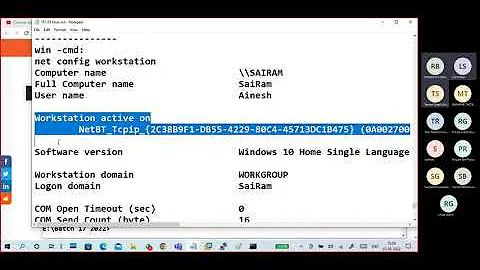
bgStack15 almost 2 yearsTL;DR
I want a Windows client to be able to access a samba share by using a freeipa credential.
Problem
This is on superuser and not serverfault because it's not a work production environment; this is my home network. There are many guides for using GNU/Linux samba for interoperability with Windows. But I don't want to have cross-domain trust (my Windows AD domain is going away eventually).
Can I configure samba to point to freeipa (ipasam? ldapsam?) so that on my Windows client (I keep around for games) I can use "[email protected]" to connect to the \linuxserver\sharename?
I know how to configure samba to use an existing AD domain for a domain-joined GNU/Linux host but that's not what I'm doing here. My host this time is the freeipa domain controller, but I might make a freeipa client my file server. I have nfs for the other Linux hosts, but my quick search on "nfs windows" didn't show anything that would be any better/easier than my desired goal here.
Possibilities
- Could I use ipasam or ldapsam backends?
- Could I use samba as a "Windows domain controller" and have it trust the ipa domain and map the users?
update on Sept 7
I found https://techslaves.org/2011/08/24/freeipa-and-samba-3-integration/ and followed its steps which show how to modify freeipa's schema to include samba properties. But I am still getting errors: NT_STATUS_WRONG_PASSWORD.