samba4 domain member server: users can't see share list, instead they are prompted for a samba password
Undoubtedly it's a authentication mechanism failure of sorts. I assume Kerberos is working for you ?
kinit [email protected]
and
kinit [email protected]
Afterwards check
klist
for the two authentication tokens should show up. If not, please post back the answer. I've seen a bunch of possible faults, but let's rule them out one by one.
Related videos on Youtube
jcalfee314
Updated on September 18, 2022Comments
-
jcalfee314 almost 2 years
We need to figure out why windows domain users are being prompted for a password when accessing samba server. They can see the server under Microsoft Windows Network, but they can not see the share list because when they click on the server's name, they get a password dialogue.
The dialogue is the problem. That should not show up. I'll offer this in-case it helps: A domain login is not valid. Again, I do not need this to work, but a user with a configured local samba password can not authenticate either (setup with
smbpasswd).At one point, I had removed an extra share in smb.conf and restarted the services
nmb,smb,winbindand it started working. I do not recall making any other changes. Later, I did a reboot to see if it were stable, and it has not allowed user in to see the shares since.It was actually working for a while, it was letting people in to see the shares and even let them into there folders (as authorized by using Active Directory security group) as designed..
My setup is the following: https://wiki.samba.org/index.php/Samba4/Domain_Member
I have temporarily disabled the firewall. Once fixed, I did include firewall rules and use some commands from this guide: http://wiki.centos.org/HowTos/SetUpSamba
This is my main configuration with validation performed by
testparm:# testparm Load smb config files from /etc/samba/smb.conf Processing section "[public]" Processing section "[accounting]" Processing section "[developer]" Loaded services file OK. Server role: ROLE_DOMAIN_MEMBER Press enter to see a dump of your service definitions [global] workgroup = MYWORKGROUP realm = MYWORKGROUP.COM server string = Samba4 Server security = ADS kerberos method = dedicated keytab winbind enum users = Yes winbind enum groups = Yes winbind use default domain = Yes winbind nss info = rfc2307 idmap config MYWORKGROUP:range = 500-40000 idmap config MYWORKGROUP:schema_mode = rfc2307 idmap config MYWORKGROUP:backend = ad idmap config *:range = 70001-80000 idmap config * : backend = tdb [public] path = /mnt/public force group = domain users read only = No [accounting] path = /mnt/accounting valid users = accounting force group = accounting read only = No [developer] path = /mnt/developer force group = developer read only = No/etc/krb5.conf
# cat krb5.conf [logging] default = FILE:/var/log/krb5libs.log kdc = FILE:/var/log/krb5kdc.log admin_server = FILE:/var/log/kadmind.log [libdefaults] default_realm = MYWORKGROUP.COM dns_lookup_realm = true dns_lookup_kdc = true ticket_lifetime = 24h forwardable = yes [appdefaults] pam = { debug = false ticket_lifetime = 36000 renew_lifetime = 36000 forwardable = true krb4_convert = false }Suffixed winbind after files (note, some systems use compact instead of files):
# egrep winbind nsswitch.conf passwd: files winbind shadow: files winbind group: files winbindI did not see any SELinux Samba security features that needed to be on:
# getsebool -a | grep samba samba_create_home_dirs --> off samba_domain_controller --> off samba_enable_home_dirs --> off samba_export_all_ro --> off samba_export_all_rw --> off samba_portmapper --> off samba_run_unconfined --> off samba_share_fusefs --> off samba_share_nfs --> off sanlock_use_samba --> off use_samba_home_dirs --> off virt_use_samba --> off # getsebool -a | grep smb allow_smbd_anon_write --> offAlthough, I have to start
nmbdin a script as the service start script is throwing an error (bind failed on pipe socket /var/run/samba/nmbd/unexpected: Address already in use) on this platform. It worked at one point when I had simply started it using the command:nmbd(two messages appear in log.nmbd:nmbd ...started,standard input is not a socket, assuming -D option). So, here is my restart script:# cat smb-restart service nmb restart nmbd service smb restart service winbind restart ps -eaf|egrep "mbd|winbind"Everything appears to be running:
# ps -eaf|egrep "mbd|winbind" root 25057 1 0 12:38 ? 00:00:00 nmbd root 25071 1 0 12:38 ? 00:00:00 smbd root 25087 1 0 12:38 ? 00:00:00 winbindd root 25091 25087 0 12:38 ? 00:00:00 winbindd root 25092 25071 0 12:38 ? 00:00:00 smbd root 25512 25087 0 12:45 ? 00:00:00 winbindd root 25513 25087 0 12:45 ? 00:00:00 winbindd root 25514 25087 0 12:45 ? 00:00:00 winbindd root 25579 25087 0 12:45 ? 00:00:00 winbinddNot sure if this is required, but I have added pam winbind commands here:
# cat /etc/pam.d/system-auth-ac #%PAM-1.0 # This file is auto-generated. # User changes will be destroyed the next time authconfig is run. auth required pam_env.so auth sufficient pam_fprintd.so auth sufficient pam_unix.so nullok try_first_pass auth requisite pam_succeed_if.so uid >= 500 quiet auth sufficient pam_krb5.so use_first_pass auth sufficient pam_winbind.so use_first_pass auth required pam_deny.so account required pam_unix.so account sufficient pam_localuser.so account sufficient pam_succeed_if.so uid < 500 quiet account sufficient pam_winbind.so use_first_pass account required pam_permit.so password requisite pam_cracklib.so try_first_pass retry=3 type= password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok password sufficient pam_krb5.so use_authok password sufficient pam_winbind.so use_first_pass password required pam_deny.so session optional pam_keyinit.so revoke session required pam_limits.so session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid session required pam_unix.so session optional pam_krb5.so session optional pam_winbind.so use_first_passI have successfully joined the domain and I can see domain users and groups via
wbinfo -uandwbinfo -g.I can list and re-new the service principal with
kinit [email protected]andklist.I think winbind is loaded fine:
# ldconfig -v | grep winbind libnss_winbind.so.2 -> libnss_winbind.so.2 # locate libnss_winbind /lib64/libnss_winbind.so /lib64/libnss_winbind.so.2 /usr/lib64/libnss_winbind.so # locate libnss_wins /lib64/libnss_wins.so /lib64/libnss_wins.so.2 /usr/lib64/libnss_wins.soI have a user called jcalfee, but the
idcommand does can not find them:# wbinfo -u|egrep jcalfee jcalfee # id jcalfee id: jcalfee: No such userI am, however, able to
chgrpusing a domain group.chgrp "domain users" /mnt/publicMy host file contains a line like this, I was required to put the smb-host fully resolved name first on the 127.0.0.1 line:
127.0.0.1 smb-host.domain.com samba-host localhost ....This is how I setup a new share directory in SELinux, this has been working:
function mkdir_samba_share { path=${1?directory path} set -o xtrace mkdir -p "$path" semanage fcontext -a -t samba_share_t "$path(/.*)?" restorecon -R "$path" chmod 770 -R "$path" chgrp "domain users" "$path" ls -ldZ "$path" set +o xtrace }I added a keytab (this will warn if your smb.conf does not contain a global kerberos method).
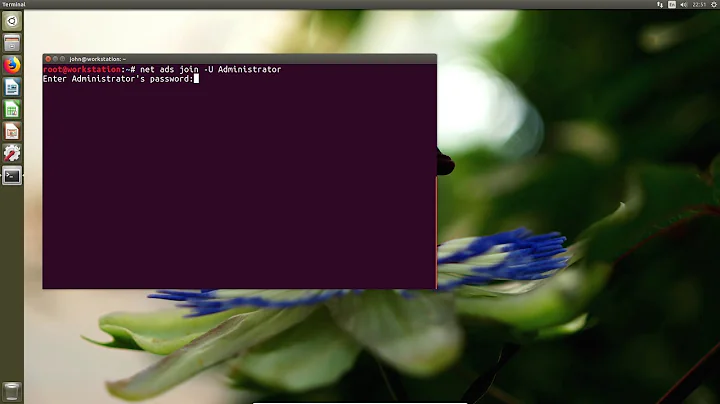
net ads keytab create -U Administrator%password-
Schrute about 11 yearsAre the client machines using credential manager to store the login for the mount perhaps? This has burned me once, when the users domain account password was changed, somehow on some machines a "net use" was done so then the stored credential was being referenced.
-
jcalfee314 about 11 yearsNot sure, but I tested with my machine and the password has not been changed recently. You are on to something though, I have since turned on log level 3 and discovered these samba errors that occur when I try to browse the shares from windows:
sam_logon returned ACCESS_DENIED. Maybe the trust account password was changed and we didn't know it. Killing connections to domain ....andAuthentication for user [jcalfee] -> [jcalfee] FAILED with error NT_STATUS_ACCESS_DENIED. -
James Hebden about 11 yearsIs the domain trust intact?
net ads testjoinwill test whether or not the server is joined to the domain successfully. Worth checking, but not sure that this is the silver bullet given you're getting user and group information from the domain. -
jcalfee314 about 11 years# net ads testjoin
Join is OK
-
-
jcalfee314 about 11 yearsI ran both command and authenticated as our administrator and a user. I see one Default princapal: [email protected] then a Valid starting / Expires / Service principal string (so, I assume that is the two you were looking for).
-
Alexandru-Florin Vintiloiu about 11 yearsOk. Next, although it might be a no brainer. still ... permissions on share/home directories. Do they match on users/ group that the user is accesing them ?
-
jcalfee314 about 11 yearsI did test it with no shares at all, one share, and left in-place the 3 shares above that had worked previously.