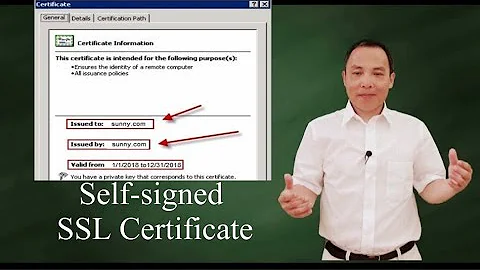
Self signed certificate in certificate chain
At some level, a self-signed certificate will always appear in a certificate chain - most notably the case with CA certs, which are by definition self-signed, but are trusted. You are seeing that message because the StartSSL CA cert is self-signed.
Your chain file is also wrong - you don't need the client certificates. The file should be in the following order, from the top of the file to the bottom, links are to StartSSL's equivalent cert, assuming class 2 validation (documentation is here):
- Private key (optional)
- Your Public certificate
- Class 2 Intermediate Certificate
- Root CA certificate
Your error could be down to using the wrong port, as discussed here. For reference, port 995 is used for POP SSL connections, port 993 is used for IMAP SSL (reference).
Related videos on Youtube
MultiformeIngegno
Updated on September 18, 2022Comments
-
MultiformeIngegno over 1 year
I'm having building the correct certificate chain. My certificate issue a class 2 issued by StartSSL.
Here's in order what I have put in my ssl.crt:
my cert https://www.startssl.com/certs/ca.pem https://www.startssl.com/certs/class2/sha1/pem/sub.class2.client.sha1.ca.pem https://www.startssl.com/certs/class2/sha1/pem/sub.class2.server.sha1.ca.pem(I put the links to allow you to see where I took the files)
If I do a
openssl s_client -connect multiformeingegno.it:993I get:Verify return code: 19 (self signed certificate in certificate chain) --- * OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE AUTH=PLAIN AUTH=LOGIN] Dovecot (Ubuntu) readyAnd if I try to add my account to Gmail here's what I get:
"Missing +OK response upon connecting to the server: * OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE AUTH=PLAIN AUTH=LOGIN] Dovecot (Ubuntu) ready."Why does it say a self-signed cert?
-
MultiformeIngegno almost 9 yearsSh*t.. that means if I want to link my account with Gmail I need to use another CA?
-
ObiwanKeTobi almost 9 yearsNo. You need to fix your certificate chain file.
-
 Steffen Ullrich almost 9 yearsThe root certificate should be in the client itself and starting from this trust anchor it will built the trust chain using the intermediate certificates until it reaches the leaf certificate. Thus the root certificate itself does not need to be including in the chain send by the server. While mostly ignored by the client there might be cases where including the root certificate might even cause problems, so it is better to leave it out.
Steffen Ullrich almost 9 yearsThe root certificate should be in the client itself and starting from this trust anchor it will built the trust chain using the intermediate certificates until it reaches the leaf certificate. Thus the root certificate itself does not need to be including in the chain send by the server. While mostly ignored by the client there might be cases where including the root certificate might even cause problems, so it is better to leave it out. -
ObiwanKeTobi almost 9 years@SteffenUllrich thanks - never knew of issues with including the root CA. Have edited my answer to include references to port issues which have the same resulting error.
-
MultiformeIngegno almost 9 yearsActually yes I'm trying to connect to POP3 using the IMAP port.. ahah -.-