Send email if user accesses the server via ssh
Solution 1
To me the question is still unclear, so I try to answer the question contained in the first paragraph. How to log SSH logins?
I will also limit my answer to all *nix systems with PAM support. This is a relevant point, because you do not limit the scope of your question by giving a particular OS.
Okay, here's what I used in the past: sshrc. If you add a file named that in /etc/ssh (location may vary!), it will be executed by interactive (i.e. with shell) SSH connections.
Downside here is that you won't get informed about the stuff that is also relevant, such as SFTP (sftp-internal subsystem) connections.
However, we have an inroute here.
We can use PAM with pam_exec.so to our advantage and limit its effect to SSH by adding this to /etc/pam.d/sshd (for me it's the last non-comment line):
session optional pam_exec.so stdout /etc/your_email_script.sh
This will ensure that the script gets run as a privileged user (relevant if you prefer to call the sendmail binary to send off the mail) and that there is hardly anything the user can do to avoid this script being run. You can effectively limit access to that script to only root.
The part with optional you should adjust if needed. Relevant reading: man pam_exec, man pam.conf, man pam.d.
You may also want to play with how early on you want to execute your script.
What you see to miss is. You have so many other ways of locking down the server. For starters: don't allow passwords. Stick to key-only authentication. Make sure that people with only SFTP access do not have additional access:
Match group sftponly
ChrootDirectory /home
X11Forwarding no
AllowTcpForwarding no
ForceCommand internal-sftp
PasswordAuthentication no
will let members of group sftponly only use SFTP and no port forwarding etc, and limit the scope to /home (file/folder permissions do the rest).
AllowGroups ssh-users
will only let members of a group ssh-users even log on via SSH. That is, you can limit SSH logon to a subset of your user base.
PermitRootLogin no
should be set and relevant users be made sudoers instead.
PasswordAuthentication no
PubkeyAuthentication yes
should ensure that password over which you have limited control cannot be used to log on.
AuthorizedKeysFile /some/protected/folder/.ssh/authorized_keys
can ensure that users aren't allowed to manage their authorized_keys file, but requires you to do it on their behalf.
Solution 2
You can do this by (carefully) editing /etc/pam.d/sshd and adding the pam_exec module into the stack. This module can be used to call an external program - such as your script - when someone has successfully started an ssh session.
Let me know if you need "how to" instructions and I'll update my answer to include them for a Debian-based system. (Other distributions have slightly different PAM stacks, so you would have to interpret my instructions rather than follow them blindly.)
Solution 3
Try this:
#!/bin/bash
if [ ! $(whoami) == root ] ; then
echo "Login on $(hostname) at $(date +%Y-%m-%d +%H:%M)"
echo "User: "$(whoami)
echo
id
echo
finger
fi
Related videos on Youtube
Comments
-
rubo77 over 1 year
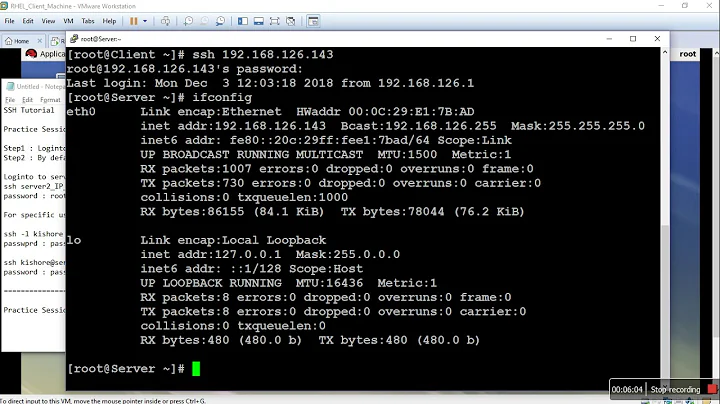
I want to get notified if any person accesses my Debian server via ssh.
So I want to send an email whenever a user logs in on my server via ssh, so I added this line at the end of
/etc/profile:/usr/local/bin/shell-login.sh | mailx -s "SSH Login User $(whoami) on YOUR-HOSTNAME" [email protected]/usr/local/bin/shell-login.shcontains:#!/bin/bash echo "Login on $(hostname) at $(date +%Y-%m-%d +%H:%M)" echo "User: "$(whoami) echo id echo fingerThis works too well: I get an email every minute now telling me that
rootis logging in, which seems to be caused bycron(see/var/log/auth.log)How do I have to change this setup to send no emails on automated internal ssh-calls?
-
 Admin over 9 yearsYou can put a check in your bash script for external user by checking the output of
Admin over 9 yearsYou can put a check in your bash script for external user by checking the output ofwand do invert match for the external connection. your bash script should return fail and then do not execute the email alert. let me know if this make sense then I will propose detail answer -
 Admin over 9 yearsHow do you make login in call this script? Do you included it in
Admin over 9 yearsHow do you make login in call this script? Do you included it in/etc/bash.bashrc? Something in/etc/ssh/sshd_config? Is someone/someprogram reallyssh-ing into your machine every minute from the machine? -
 Admin over 9 yearsWhat are the close-votes about? I edited my question to clarify the problem
Admin over 9 yearsWhat are the close-votes about? I edited my question to clarify the problem -
 Admin over 9 yearsOnly some mysterious "external" access, or a number of specific ones?
Admin over 9 yearsOnly some mysterious "external" access, or a number of specific ones? -
 Admin over 9 years@0xC0000022L: I see, there seemed to be something missing at the end of my question. I hope now it is clearer
Admin over 9 years@0xC0000022L: I see, there seemed to be something missing at the end of my question. I hope now it is clearer -
 Admin over 9 years@rubo77: quite the opposite. Before I had assumed this was about
Admin over 9 years@rubo77: quite the opposite. Before I had assumed this was aboutsshdbut you mentionedcronas a counter-example. Now after the latest edit you say effectively you want no emails aboutsshdorcron?! I am wondering, because I am contemplating to answer, but the question, to me, is still unclear. -
 Admin over 9 yearsI want to find out, if someone was able to get hold of password or ssh-key to any of the users on my server and logs in via ssh with that password or ssh-key. I also want to get notified if any person accesses my server.
Admin over 9 yearsI want to find out, if someone was able to get hold of password or ssh-key to any of the users on my server and logs in via ssh with that password or ssh-key. I also want to get notified if any person accesses my server. -
 Admin over 9 yearsNote that you're doing it wrong: if the user pressed Ctrl+C fast enough then
Admin over 9 yearsNote that you're doing it wrong: if the user pressed Ctrl+C fast enough then/etc/profilewill be skipped.pam_execis ok because that happens before the actual login. But really what you should look into is log monitoring.
-
-
rubo77 over 9 yearsAs a workaround, this would work, but only, if you have root login disabled in your ssh config, otherwise, you would miss mails on a real root login
-
DiogoSaraiva over 9 yearssorry, for that. I just want to help
-
rubo77 over 9 yearsI tried a lot now with
pam_exec.sobut I always get notified that the userrootlogged in, instead of my username. I used the script in my question. I tried the optionseteuidandquietbut still, always it sais it was root -
0xC0000022L over 9 years@rubo77: Wait wait wait ... you did read the friendly manual of
pam_exec, didn't you? Hint the following variables are available to the program run bypam_exec:PAM_RHOST,PAM_RUSER,PAM_SERVICE,PAM_TTY,PAM_USERandPAM_TYPE. -
rubo77 over 9 yearsSo I can rewrite the script like this: unix.stackexchange.com/a/126573/20661
-
 Philippe Gachoud about 4 yearsfound it here askubuntu.com/questions/179889/…
Philippe Gachoud about 4 yearsfound it here askubuntu.com/questions/179889/…