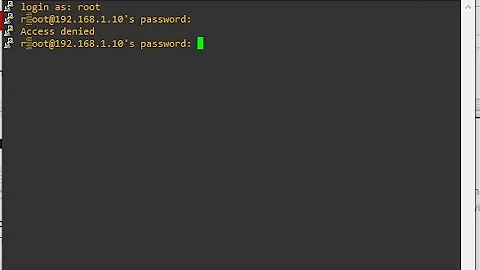
SSH fails with error "Permission denied (Password)"
I had PasswordAuthentication no added to my /etc/ssh/ssh_config on A!
After commenting out the line it worked.
Related videos on Youtube
Fynn
Updated on September 18, 2022Comments
-
Fynn over 1 year
I am trying to SSH into a PC (lets call it B) with Ubuntu Server 18.04 from a Raspberry Pi (lets call it A) with Raspbian Stretch Lite. Both are on my local network. PublicKeyAuth is disabled and PasswordAuth is enabled on B (a copy of my /etc/ssh/sshd_config on B is appended to the end of the question)
When I try to
ssh user@Bfrom A it fails with the messagePermission denied (Password)after looking at the output ofssh -v user@BI thought that it might still try to use the PublicKeyAuth and found this other question discussing how to force the client to use PasswordAuth.But the suggested command doesn't work either, so it seems to be another issue.
I also deleted the entry for B from my
known_hostsfile on A in case this comes with any default values attached, but ssh still failed.When I try to ssh from my notebook with the same settings on B it asks me for a password instead and logs me in after I supply it.
It is possible to just add the key of A manually on B, but I would like to know what I misconfigured in order to avoid it the next time!
Output of
ssh -o PreferredAuthentications=password -o PubkeyAuthentication=no user@ipon A:OpenSSH_7.4p1 Raspbian-10+deb9u4, OpenSSL 1.0.2l 25 May 2017 debug1: Reading configuration data /etc/ssh/ssh_config debug1: /etc/ssh/ssh_config line 19: Applying options for * debug2: resolving "192.168.x.x" port 22 debug2: ssh_connect_direct: needpriv 0 debug1: Connecting to 192.168.x.x [192.168.x.x] port 22. debug1: Connection established. debug1: identity file /home/user/.ssh/id_rsa type 1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_rsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_dsa type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_dsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_ecdsa type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_ecdsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_ed25519 type -1 debug1: key_load_public: No such file or directory debug1: identity file /home/user/.ssh/id_ed25519-cert type -1 debug1: Enabling compatibility mode for protocol 2.0 debug1: Local version string SSH-2.0-OpenSSH_7.4p1 Raspbian-10+deb9u4 debug1: Remote protocol version 2.0, remote software version OpenSSH_7.6p1 Ubuntu-4 debug1: match: OpenSSH_7.6p1 Ubuntu-4 pat OpenSSH* compat 0x04000000 debug2: fd 3 setting O_NONBLOCK debug1: Authenticating to 192.168.x.x:22 as 'user' debug3: hostkeys_foreach: reading file "/home/user/.ssh/known_hosts" debug3: record_hostkey: found key type ECDSA in file /home/user/.ssh/known_hosts:3 debug3: load_hostkeys: loaded 1 keys from 192.168.x.x debug3: order_hostkeyalgs: prefer hostkeyalgs: [email protected],[email protected],[email protected],ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521 debug3: send packet: type 20 debug1: SSH2_MSG_KEXINIT sent debug3: receive packet: type 20 debug1: SSH2_MSG_KEXINIT received debug2: local client KEXINIT proposal debug2: KEX algorithms: curve25519-sha256,[email protected],ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha256,diffie-hellman-group14-sha1,ext-info-c debug2: host key algorithms: [email protected],[email protected],[email protected],ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,[email protected],[email protected],ssh-ed25519,rsa-sha2-512,rsa-sha2-256,ssh-rsa debug2: ciphers ctos: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected],aes128-cbc,aes192-cbc,aes256-cbc debug2: ciphers stoc: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected],aes128-cbc,aes192-cbc,aes256-cbc debug2: MACs ctos: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: MACs stoc: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: compression ctos: none,[email protected],zlib debug2: compression stoc: none,[email protected],zlib debug2: languages ctos: debug2: languages stoc: debug2: first_kex_follows 0 debug2: reserved 0 debug2: peer server KEXINIT proposal debug2: KEX algorithms: curve25519-sha256,[email protected],ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256,diffie-hellman-group14-sha1 debug2: host key algorithms: ssh-rsa,rsa-sha2-512,rsa-sha2-256,ecdsa-sha2-nistp256,ssh-ed25519 debug2: ciphers ctos: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected] debug2: ciphers stoc: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected] debug2: MACs ctos: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: MACs stoc: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: compression ctos: none,[email protected] debug2: compression stoc: none,[email protected] debug2: languages ctos: debug2: languages stoc: debug2: first_kex_follows 0 debug2: reserved 0 debug1: kex: algorithm: curve25519-sha256 debug1: kex: host key algorithm: ecdsa-sha2-nistp256 debug1: kex: server->client cipher: [email protected] MAC: <implicit> compression: none debug1: kex: client->server cipher: [email protected] MAC: <implicit> compression: none debug3: send packet: type 30 debug1: expecting SSH2_MSG_KEX_ECDH_REPLY debug3: receive packet: type 31 debug1: Server host key: ecdsa-sha2-nistp256 SHA256:ycsiE8n8WxPvLtO29np2RbItqRhExmsSITflO7c67qQ debug3: hostkeys_foreach: reading file "/home/user/.ssh/known_hosts" debug3: record_hostkey: found key type ECDSA in file /home/user/.ssh/known_hosts:3 debug3: load_hostkeys: loaded 1 keys from 192.168.x.x debug1: Host '192.168.x.x' is known and matches the ECDSA host key. debug1: Found key in /home/user/.ssh/known_hosts:3 debug3: send packet: type 21 debug2: set_newkeys: mode 1 debug1: rekey after 134217728 blocks debug1: SSH2_MSG_NEWKEYS sent debug1: expecting SSH2_MSG_NEWKEYS debug3: receive packet: type 21 debug1: SSH2_MSG_NEWKEYS received debug2: set_newkeys: mode 0 debug1: rekey after 134217728 blocks debug2: key: /home/user/.ssh/id_rsa (0x1f2c0c0) debug2: key: /home/user/.ssh/id_dsa ((nil)) debug2: key: /home/user/.ssh/id_ecdsa ((nil)) debug2: key: /home/user/.ssh/id_ed25519 ((nil)) debug3: send packet: type 5 debug3: receive packet: type 7 debug1: SSH2_MSG_EXT_INFO received debug1: kex_input_ext_info: server-sig-algs=<ssh-ed25519,ssh-rsa,rsa-sha2-256,rsa-sha2-512,ssh-dss,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521> debug3: receive packet: type 6 debug2: service_accept: ssh-userauth debug1: SSH2_MSG_SERVICE_ACCEPT received debug3: send packet: type 50 debug3: receive packet: type 51 debug1: Authentications that can continue: password debug3: start over, passed a different list password debug3: preferred password debug3: authmethod_lookup password debug3: remaining preferred: debug1: No more authentication methods to try. Permission denied (password).My
/etc/ssh/sshd_confon B:# $OpenBSD: sshd_config,v 1.101 2017/03/14 07:19:07 djm Exp $ # This is the sshd server system-wide configuration file. See # sshd_config(5) for more information. # This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin # The strategy used for options in the default sshd_config shipped with # OpenSSH is to specify options with their default value where # possible, but leave them commented. Uncommented options override the # default value. #Port 22 #AddressFamily any #ListenAddress 0.0.0.0 #ListenAddress :: #HostKey /etc/ssh/ssh_host_rsa_key #HostKey /etc/ssh/ssh_host_ecdsa_key #HostKey /etc/ssh/ssh_host_ed25519_key # Ciphers and keying #RekeyLimit default none # Logging #SyslogFacility AUTH #LogLevel INFO # Authentication: #LoginGraceTime 2m #PermitRootLogin prohibit-password #StrictModes yes #MaxAuthTries 6 #MaxSessions 10 PubkeyAuthentication no PasswordAuthentication yes # Expect .ssh/authorized_keys2 to be disregarded by default in future. #AuthorizedKeysFile .ssh/authorized_keys .ssh/authorized_keys2 #AuthorizedPrincipalsFile none #AuthorizedKeysCommand none #AuthorizedKeysCommandUser nobody # For this to work you will also need host keys in /etc/ssh/ssh_known_hosts #HostbasedAuthentication no # Change to yes if you don't trust ~/.ssh/known_hosts for # HostbasedAuthentication #IgnoreUserKnownHosts no # Don't read the user's ~/.rhosts and ~/.shosts files #IgnoreRhosts yes # To disable tunneled clear text passwords, change to no here! #PermitEmptyPasswords no # Change to yes to enable challenge-response passwords (beware issues with # some PAM modules and threads) ChallengeResponseAuthentication no # Kerberos options #KerberosAuthentication no #KerberosOrLocalPasswd yes #KerberosTicketCleanup yes #KerberosGetAFSToken no # GSSAPI options #GSSAPIAuthentication no #GSSAPICleanupCredentials yes #GSSAPIStrictAcceptorCheck yes #GSSAPIKeyExchange no # Set this to 'yes' to enable PAM authentication, account processing, # and session processing. If this is enabled, PAM authentication will # be allowed through the ChallengeResponseAuthentication and # PasswordAuthentication. Depending on your PAM configuration, # PAM authentication via ChallengeResponseAuthentication may bypass # the setting of "PermitRootLogin without-password". # If you just want the PAM account and session checks to run without # PAM authentication, then enable this but set PasswordAuthentication # and ChallengeResponseAuthentication to 'no'. UsePAM yes #AllowAgentForwarding yes #AllowTcpForwarding yes #GatewayPorts no X11Forwarding yes #X11DisplayOffset 10 #X11UseLocalhost yes #PermitTTY yes PrintMotd no #PrintLastLog yes #TCPKeepAlive yes #UseLogin no #PermitUserEnvironment no #Compression delayed #ClientAliveInterval 0 #ClientAliveCountMax 3 #UseDNS no #PidFile /var/run/sshd.pid #MaxStartups 10:30:100 #PermitTunnel no #ChrootDirectory none #VersionAddendum none # no default banner path #Banner none # Allow client to pass locale environment variables AcceptEnv LANG LC_* # override default of no subsystems Subsystem sftp /usr/lib/openssh/sftp-server # Example of overriding settings on a per-user basis #Match User anoncvs # X11Forwarding no # AllowTcpForwarding no # PermitTTY no # ForceCommand cvs server-
 D'Arcy Nader over 5 yearsperhaps your password is wrong.
D'Arcy Nader over 5 yearsperhaps your password is wrong. -
Fynn over 5 yearsIt does not ask me for a password
-
Fynn over 5 yearsIt might automagically try one, but i dont know where it would get that from. But that might be the answer if you can tell me where default passwords are stored (or how to delete them)
-
Fynn over 5 yearsno, but i generated some for the first time (before trying to ssh in)
-
Fynn over 5 yearsi have
id_rsaandid_rsa.pubin my~/.sshdir (on A) -
 D'Arcy Nader over 5 yearsyes those are good !
D'Arcy Nader over 5 yearsyes those are good ! -
 D'Arcy Nader over 5 yearshave you tried
D'Arcy Nader over 5 yearshave you triedssh -o PreferredAuthentications=keyboard-interactive -o PubkeyAuthentication=no B -
Fynn over 5 yearsjust tried it for the first time, but still gives the same error
-
 D'Arcy Nader over 5 yearswhy don't you try to create another user on your raspberry, and try to use the new user to connect to B and see if it works.
D'Arcy Nader over 5 yearswhy don't you try to create another user on your raspberry, and try to use the new user to connect to B and see if it works. -
Fynn over 5 yearsshould i append the debug messages?
-
 D'Arcy Nader over 5 yearsis it different from the first one? if yes .. yes if no .. no .
D'Arcy Nader over 5 yearsis it different from the first one? if yes .. yes if no .. no . -
 D'Arcy Nader over 5 yearsLet us continue this discussion in chat.
D'Arcy Nader over 5 yearsLet us continue this discussion in chat.
-
-
 Admin about 2 yearsFynn's answer was part of the solution, but I had to set
Admin about 2 yearsFynn's answer was part of the solution, but I had to setChallengeResponseAuthenticationtoyesfor a password prompt to appear.