Terminal Server - Group Policy prevent command line
Solution 1
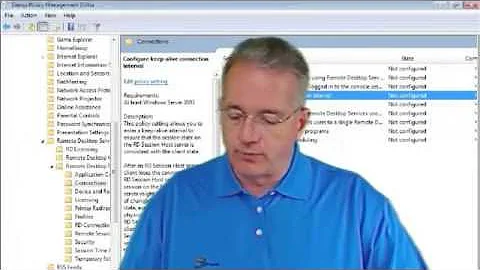
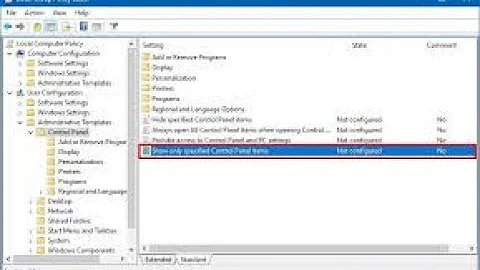
There's a group policy setting that explicitly sets this, located here: Computer Configuration -> Administrative Templates -> Windows Components -> Terminal Services -> "Allow users to connect remotely via Terminal Services"
To fix the issue, you need to unset (not 'disable') this on the GPO. After a policy refresh you should get back the ability to control logon availability.
Solution 2
You can also remove Group Policy's ability to actually apply that setting by setting up the permissions without System. Mark Russinovich has a good article on doing this.
This is slightly better than a Scheduled Task to change the registry value. I wouldn't call it elegant, though :)
But really, the right way to do this is to either unset the Group Policy (as Chris Thorpe said), or disable inheritance for the server's OU and make another GPO without that particular policy.
EDIT: You can also use WMI filtering to exclude that particular server from receiving the entire policy. Note that if a particular GPO is filtered out, the ENTIRE GPO's policies are not applied. If you go this route, I'd recommend breaking out the Terminal Server connection policy into a new GPO, so the rest of the settings aren't ignored.
Microsoft TechNet info: http://technet.microsoft.com/en-us/library/cc779036(WS.10).aspx
Filtering based on computer name (scroll down for the answer): http://www.experts-exchange.com/Software/Server_Software/File_Servers/Active_Directory/Q_22864893.html
Related videos on Youtube
Developer
Updated on September 17, 2022Comments
-
Developer over 1 year
Retrieve the receipt data from the transaction’s transactionReceipt property and encode it using base64 encoding.How can I encode NSData using base64 encoding? Please give the code for that.
EDIT
I did it. but now the response is{exception = "java.lang.NullPointerException"; status = 21002;}my recipt verification method is this
-(BOOL)verifyReceipt:(SKPaymentTransaction *)transaction { NSString *recieptString = [transaction.transactionReceipt base64EncodingWithLineLength:0]; NSLog(@"%@",recieptString); ASIFormDataRequest *request = [[ASIFormDataRequest alloc] initWithURL:[NSURL URLWithString:[NSString stringWithFormat:@"https://buy.itunes.apple.com/verifyReceipt"]]]; [request setPostValue:recieptString forKey:@"receipt-data"]; [request setPostValue:@"95140bdac98d47a2b15e8e5555f55d41" forKey:@"password"]; [request start]; NSDictionary* subsInfo = [[request responseString] JSONValue]; NSLog(@"%@",subsInfo); return subscriptionEnabled; }Where
NSString *recieptString = [transaction.transactionReceipt base64EncodingWithLineLength:0];returns me base64 encoded string.
I also triedNSString *recieptString = [transaction.transactionReceipt base64EncodingWithLineLength:[transaction.transactionReceipt length]];but response is same.
can any one of you let me know where I could be wrong.
Thanks--
 Admin about 14 yearsHave you found an answer to this?
Admin about 14 yearsHave you found an answer to this? -
 Admin about 14 yearsno, i found no solution to this problem.
Admin about 14 yearsno, i found no solution to this problem. -
Dancreek about 13 yearsIt would be helpful to have some more context.
-
-
Zoredache almost 14 yearsWhile I agree this is the problem and changing the policy may fix the issue, given the current OU/GPO structure making this change is not an option. Are their any alternatives? One thing that looks tempting is in the Session Host Configuration. There is an option
User Login Modewhere you can set the host to prevent new connections. Do you know how to modify theUser Login Modefrom a script/command line? I would like to be able toggle betweenAllow allandPrevent reconnections. -
Aashraya Singal almost 14 yearsThere's no way of fixing the issue unless you can somehow remove that policy's applicance onto that particular server. You could do this by creating a dedicated OU for the terminal server, moving the terminal server object into this OU, and creating a copy of the policy applied to the previous OU and setting 'block inheritence' on the OU. Then just take off the one setting you wanted to remove. I'm not aware of a non-GPO solution to this, as bypassing GPO settings is generally not possible regardless of the approach. By design.
-
NorbyTheGeek over 11 yearsAs an update for people finding this answer via Google, the policy is now located in Administrative Templates -> Windows Components -> Remote Desktop Services -> Remote Desktop Session Host -> Connections -> "Allow users to connect remotely using Remote Desktop Services"
-
beretis over 7 yearsThank you for this!
-
Zennichimaro over 7 yearswhere did you get the base64 encoding code that works with Apple receipt verifier server? it was working but it is no longer working anymore (current iOS 10.0, base sdk: 8.0)
-
Zennichimaro over 7 yearssorry.. I POST receipt-data="xxx" whereas I should POST in JSON "{ \"receipt-data\" : \"xxx\"}"
-
Zennichimaro over 7 yearsnow it works, but I am still curious where did you get the code.. even Apple's [NSData base64EncodedStringWithOptions] doesn't work, whatever the options is... stupid Apple..
-
Saurabh over 7 yearsThis above is the core algorithm to convert anything to base64 if you search google you could find this in almost every other language
![DevOps & SysAdmins: Re-Posting this - Terminal Server - Group Policy prevent command line [2]](https://i.ytimg.com/vi/c0tukJvkFCw/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLCXUMQr0PldEau5vS-oQ8IGyV4Rfw)
