Ubuntu 20.04 - how to set lower SSL security level?
Solution 1
You don't have your config changes quite right. You need to add this to the beginning of your config file:
openssl_conf = default_conf
And then this to the end:
[ default_conf ]
ssl_conf = ssl_sect
[ssl_sect]
system_default = system_default_sect
[system_default_sect]
MinProtocol = TLSv1.2
CipherString = DEFAULT:@SECLEVEL=1
Note that if you prefer you can make changes to a local copy of the config file, and then ensure your process is started with the environment variable OPENSSL_CONF defined to point at the location of your config file:
export OPENSSL_CONF=/path/to/my/openssl.cnf
This way you can make changes without having to impact your entire system.
Note: To find the system's openssl.cnf file, run the following:
% openssl version -d
the run ls -l on the directory outputted to see where the openssl.cnf file is via its symlink in that directory as needed.
Solution 2
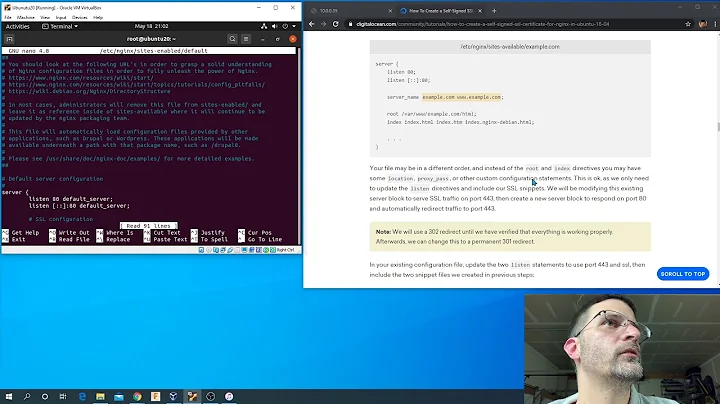
Edit openssl.conf file:
sudo nano /etc/ssl/openssl.cnf
Add this line at the top:
openssl_conf = openssl_init
And add these lines at the end:
[openssl_init]
ssl_conf = ssl_sect
[ssl_sect]
system_default = system_default_sect
[system_default_sect]
CipherString = DEFAULT@SECLEVEL=1
It works for me. :)
Ref: When I try to CURL a website I get SSL error
For the Laravel, also run
sudo service php7.4-fpm restart
Solution 3
The two solutions above were confusing for me.
You just need two blocks of modifications in /usr/lib/ssl/openssl.cnf as documented with this diff:
rcsdiff ./openssl.cnf
===================================================================
RCS file: ./openssl.cnf,v
retrieving revision 1.1
diff -r1.1 ./openssl.cnf
13a14,15
> openssl_conf = default_conf
>
350a353,362
>
> [default_conf]
> ssl_conf = ssl_sect
>
> [ssl_sect]
> system_default = system_default_sect
>
> [system_default_sect]
> MinProtocol = TLSv1.2
> CipherString = DEFAULT@SECLEVEL=1
For cut&paste:
openssl_conf = default_conf
[default_conf]
ssl_conf = ssl_sect
[ssl_sect]
system_default = system_default_sect
[system_default_sect]
MinProtocol = TLSv1.2
CipherString = DEFAULT@SECLEVEL=1
Solution 4
Update: the previous answer seems to work if you extract the default configuration from the deb file by downloading it on https://packages.ubuntu.com/search?keywords=openssl&searchon=names.
Update 2: in fact the previous answer did not work for me because I had a wrong config file using [system_default_sect] instead of [ssl_default_sect]. It seems to be an error that I copy-pasted from https://wiki.debian.org/ContinuousIntegration/TriagingTips/openssl-1.1.1. It is possible to use the name system_default_sect to be consistent with Debian, you just need to use it everywhere instead of ssl_default_sect.
Original answer:
The previous answer was not working for me on Ubuntu 20.04 so I used the config file from my Debian LXC container on Ubuntu and changed SECLEVEL=2 to SECLEVEL=1.
I saved the file as /etc/ssl/openssl_custom.cnf and then used the command shared in the previous answer to load another config file when you need to:
export OPENSSL_CONF=/etc/ssl/openssl_custom.cnf
Here is the full config file that worked for me (you can also extract the default configuration from the deb file by downloading it on https://packages.debian.org/stable/openssl):
#
# OpenSSL example configuration file.
# This is mostly being used for generation of certificate requests.
#
# Note that you can include other files from the main configuration
# file using the .include directive.
#.include filename
# This definition stops the following lines choking if HOME isn't
# defined.
HOME = .
# Extra OBJECT IDENTIFIER info:
#oid_file = $ENV::HOME/.oid
oid_section = new_oids
# System default
openssl_conf = default_conf
# To use this configuration file with the "-extfile" option of the
# "openssl x509" utility, name here the section containing the
# X.509v3 extensions to use:
# extensions =
# (Alternatively, use a configuration file that has only
# X.509v3 extensions in its main [= default] section.)
[ new_oids ]
# We can add new OIDs in here for use by 'ca', 'req' and 'ts'.
# Add a simple OID like this:
# testoid1=1.2.3.4
# Or use config file substitution like this:
# testoid2=${testoid1}.5.6
# Policies used by the TSA examples.
tsa_policy1 = 1.2.3.4.1
tsa_policy2 = 1.2.3.4.5.6
tsa_policy3 = 1.2.3.4.5.7
####################################################################
[ ca ]
default_ca = CA_default # The default ca section
####################################################################
[ CA_default ]
dir = ./demoCA # Where everything is kept
certs = $dir/certs # Where the issued certs are kept
crl_dir = $dir/crl # Where the issued crl are kept
database = $dir/index.txt # database index file.
#unique_subject = no # Set to 'no' to allow creation of
# several certs with same subject.
new_certs_dir = $dir/newcerts # default place for new certs.
certificate = $dir/cacert.pem # The CA certificate
serial = $dir/serial # The current serial number
crlnumber = $dir/crlnumber # the current crl number
# must be commented out to leave a V1 CRL
crl = $dir/crl.pem # The current CRL
private_key = $dir/private/cakey.pem# The private key
x509_extensions = usr_cert # The extensions to add to the cert
# Comment out the following two lines for the "traditional"
# (and highly broken) format.
name_opt = ca_default # Subject Name options
cert_opt = ca_default # Certificate field options
# Extension copying option: use with caution.
# copy_extensions = copy
# Extensions to add to a CRL. Note: Netscape communicator chokes on V2 CRLs
# so this is commented out by default to leave a V1 CRL.
# crlnumber must also be commented out to leave a V1 CRL.
# crl_extensions = crl_ext
default_days = 365 # how long to certify for
default_crl_days= 30 # how long before next CRL
default_md = default # use public key default MD
preserve = no # keep passed DN ordering
# A few difference way of specifying how similar the request should look
# For type CA, the listed attributes must be the same, and the optional
# and supplied fields are just that :-)
policy = policy_match
# For the CA policy
[ policy_match ]
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
# For the 'anything' policy
# At this point in time, you must list all acceptable 'object'
# types.
[ policy_anything ]
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
####################################################################
[ req ]
default_bits = 2048
default_keyfile = privkey.pem
distinguished_name = req_distinguished_name
attributes = req_attributes
x509_extensions = v3_ca # The extensions to add to the self signed cert
# Passwords for private keys if not present they will be prompted for
# input_password = secret
# output_password = secret
# This sets a mask for permitted string types. There are several options.
# default: PrintableString, T61String, BMPString.
# pkix : PrintableString, BMPString (PKIX recommendation before 2004)
# utf8only: only UTF8Strings (PKIX recommendation after 2004).
# nombstr : PrintableString, T61String (no BMPStrings or UTF8Strings).
# MASK:XXXX a literal mask value.
# WARNING: ancient versions of Netscape crash on BMPStrings or UTF8Strings.
string_mask = utf8only
# req_extensions = v3_req # The extensions to add to a certificate request
[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = AU
countryName_min = 2
countryName_max = 2
stateOrProvinceName = State or Province Name (full name)
stateOrProvinceName_default = Some-State
localityName = Locality Name (eg, city)
0.organizationName = Organization Name (eg, company)
0.organizationName_default = Internet Widgits Pty Ltd
# we can do this but it is not needed normally :-)
#1.organizationName = Second Organization Name (eg, company)
#1.organizationName_default = World Wide Web Pty Ltd
organizationalUnitName = Organizational Unit Name (eg, section)
#organizationalUnitName_default =
commonName = Common Name (e.g. server FQDN or YOUR name)
commonName_max = 64
emailAddress = Email Address
emailAddress_max = 64
# SET-ex3 = SET extension number 3
[ req_attributes ]
challengePassword = A challenge password
challengePassword_min = 4
challengePassword_max = 20
unstructuredName = An optional company name
[ usr_cert ]
# These extensions are added when 'ca' signs a request.
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This is required for TSA certificates.
# extendedKeyUsage = critical,timeStamping
[ v3_req ]
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature, keyEncipherment
[ v3_ca ]
# Extensions for a typical CA
# PKIX recommendation.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid:always,issuer
basicConstraints = critical,CA:true
# Key usage: this is typical for a CA certificate. However since it will
# prevent it being used as an test self-signed certificate it is best
# left out by default.
# keyUsage = cRLSign, keyCertSign
# Some might want this also
# nsCertType = sslCA, emailCA
# Include email address in subject alt name: another PKIX recommendation
# subjectAltName=email:copy
# Copy issuer details
# issuerAltName=issuer:copy
# DER hex encoding of an extension: beware experts only!
# obj=DER:02:03
# Where 'obj' is a standard or added object
# You can even override a supported extension:
# basicConstraints= critical, DER:30:03:01:01:FF
[ crl_ext ]
# CRL extensions.
# Only issuerAltName and authorityKeyIdentifier make any sense in a CRL.
# issuerAltName=issuer:copy
authorityKeyIdentifier=keyid:always
[ proxy_cert_ext ]
# These extensions should be added when creating a proxy certificate
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This really needs to be in place for it to be a proxy certificate.
proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo
####################################################################
[ tsa ]
default_tsa = tsa_config1 # the default TSA section
[ tsa_config1 ]
# These are used by the TSA reply generation only.
dir = ./demoCA # TSA root directory
serial = $dir/tsaserial # The current serial number (mandatory)
crypto_device = builtin # OpenSSL engine to use for signing
signer_cert = $dir/tsacert.pem # The TSA signing certificate
# (optional)
certs = $dir/cacert.pem # Certificate chain to include in reply
# (optional)
signer_key = $dir/private/tsakey.pem # The TSA private key (optional)
signer_digest = sha256 # Signing digest to use. (Optional)
default_policy = tsa_policy1 # Policy if request did not specify it
# (optional)
other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional)
digests = sha1, sha256, sha384, sha512 # Acceptable message digests (mandatory)
accuracy = secs:1, millisecs:500, microsecs:100 # (optional)
clock_precision_digits = 0 # number of digits after dot. (optional)
ordering = yes # Is ordering defined for timestamps?
# (optional, default: no)
tsa_name = yes # Must the TSA name be included in the reply?
# (optional, default: no)
ess_cert_id_chain = no # Must the ESS cert id chain be included?
# (optional, default: no)
ess_cert_id_alg = sha1 # algorithm to compute certificate
# identifier (optional, default: sha1)
[default_conf]
ssl_conf = ssl_sect
[ssl_sect]
system_default = system_default_sect
[system_default_sect]
MinProtocol = TLSv1.2
CipherString = DEFAULT@SECLEVEL=1
Related videos on Youtube
Łukasz Sypniewski
Software engineer with materials science 🧪 and 3D printing 🔧 background. Amateur stock investor 📈 and handball player🤾♂️. Recently I have taken interest in DDD 📕, microservices ⚙️ and cloud ☁️.
Updated on September 18, 2022Comments
-
 Łukasz Sypniewski over 1 year
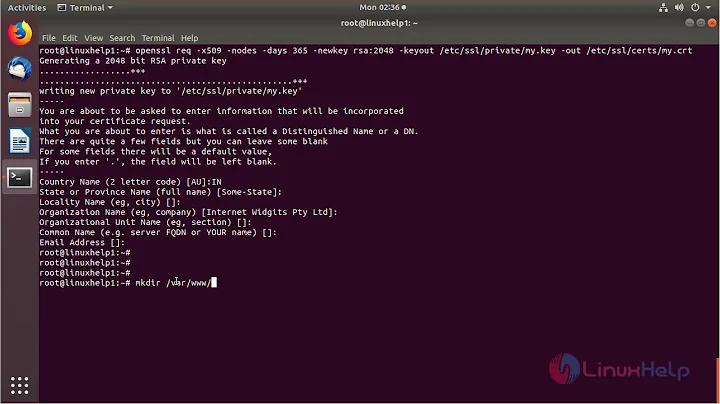
Łukasz Sypniewski over 1 yearI'd like to ask if there's a way to lower SSL security level to 1 on Ubuntu 20.04, since I'm receiving:
141A318A:SSL routines:tls_process_ske_dhe:dh key too smallwhen trying to curl the website.
Curl works if I add
--ciphers 'DEFAULT:!DH'parameter, however, I am not able to fetch a website via my client app written in C#. The website also works when opened via browser.According to bugs.launchpad.net the Ubuntu team set higher SSL security level on purpose.
In several places I came across an information that changing
CipherString = DEFAULT@SECLEVEL=2to1inopenssl.cnfhelps, but my config file did not have such a line at all and adding it had no effect.I do not control the website server, so I am not able to change its security configuration.
Any ideas? Would installing some older openSSL package help?
Thanks in advance
EDIT: As for changes to my config file, I've added the following at the end:
system_default = system_default_sect [system_default_sect] MinProtocol = TLSv1.2 CipherString = DEFAULT@SECLEVEL=1Output from
openssl version -a:OpenSSL 1.1.1f 31 Mar 2020 built on: Mon Apr 20 11:53:50 2020 UTC platform: debian-amd64 options: bn(64,64) rc4(16x,int) des(int) blowfish(ptr) compiler: gcc -fPIC -pthread -m64 -Wa,--noexecstack -Wall -Wa, --noexecstack -g -O2 -fdebug-prefix-map=/build/openssl-P_ODHM/openssl-1.1.1f=. -fstack-protector-strong -Wformat -Werror=format-security -DOPENSSL_TLS_SECURITY_LEVEL=2 -DOPENSSL_USE_NODELETE -DL_ENDIAN -DOPENSSL_PIC -DOPENSSL_CPUID_OBJ -DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 -DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DKECCAK1600_ASM -DRC4_ASM -DMD5_ASM -DAESNI_ASM -DVPAES_ASM -DGHASH_ASM -DECP_NISTZ256_ASM -DX25519_ASM -DPOLY1305_ASM -DNDEBUG -Wdate-time -D_FORTIFY_SOURCE=2 OPENSSLDIR: "/usr/lib/ssl" ENGINESDIR: "/usr/lib/x86_64-linux-gnu/engines-1.1" Seeding source: os-specific-
 Admin almost 4 yearsIs your C# application calling OpenSSL APIs directly? I'm not familiar with the C# OpenSSL bindings, but in C you can change the security level using
Admin almost 4 yearsIs your C# application calling OpenSSL APIs directly? I'm not familiar with the C# OpenSSL bindings, but in C you can change the security level usingSSL_CTX_set_cipher_list(ctx, "DEFAULT:@SECLEVEL=1");. Or alternativelySSL_CTX_set_security_level(ctx, 1). -
 Admin almost 4 yearsUnfortunately I use a high-level class to do HTTP requests. But would it be possible to call this function from C to change security level for the whole system?
Admin almost 4 yearsUnfortunately I use a high-level class to do HTTP requests. But would it be possible to call this function from C to change security level for the whole system? -
 Admin almost 4 yearsCalling it in C will only change the setting for the current process
Admin almost 4 yearsCalling it in C will only change the setting for the current process -
 Admin almost 4 yearsCan you show what changes you made to your config file, and also the output from
Admin almost 4 yearsCan you show what changes you made to your config file, and also the output fromopenssl version -a? -
 Admin almost 4 years@MattCaswell I added the information you asked for to the question
Admin almost 4 years@MattCaswell I added the information you asked for to the question
-
-
Norbert S almost 4 yearsThanks! That fixed it for me. After upgrading from Ubuntu 18.04 LTS to 20.04 LTS my
wgetrefused to connect to a server I had previously copied files from. With this modification ofopenssl.cnfit works again. -
johnny almost 4 yearsI did the updates to the openssl.cnf but still the same issue.. even after rebooting the system
-
Caleb almost 4 yearsThanks, this had me stumped, the server I was having an issue with is rated A on SSL Labs, surely this is a bug?
-
 baptx over 3 years@Caleb good question, maybe it is not considered a security vulnerability but just a security that can be improved?
baptx over 3 years@Caleb good question, maybe it is not considered a security vulnerability but just a security that can be improved? -
 baptx over 3 years@johnny it is not working for me either, did anyone get this solution working on Ubuntu 20.04? At least I found a workaround by using the curl command in a Debian LXC container where I just need to change SECLEVEL=2 to SECLEVEL=1. Update: I shared an answer that works by using the Debian config file on Ubuntu. Update 2: in fact this solution seems to work if you extract the default configuration from the deb file by downloading it on packages.ubuntu.com/search?keywords=openssl&searchon=names.
baptx over 3 years@johnny it is not working for me either, did anyone get this solution working on Ubuntu 20.04? At least I found a workaround by using the curl command in a Debian LXC container where I just need to change SECLEVEL=2 to SECLEVEL=1. Update: I shared an answer that works by using the Debian config file on Ubuntu. Update 2: in fact this solution seems to work if you extract the default configuration from the deb file by downloading it on packages.ubuntu.com/search?keywords=openssl&searchon=names. -
 baptx over 3 years@johnny In fact the answer did not work for me because I had a wrong config file using
baptx over 3 years@johnny In fact the answer did not work for me because I had a wrong config file using[system_default_sect]instead of[ssl_default_sect]. It seems to be an error that I copy-pasted from wiki.debian.org/ContinuousIntegration/TriagingTips/…. I think it is better to use the system_default_sect name to be consistent with Debian. By the way, there seems to be an unnecessary colon inDEFAULT:@SECLEVEL=1which is not present in the Debian config file. -
Costas Bakoulias about 3 yearsIt works for me! I have clear setup of ubuntu 20.04 LTS. Thanks!
-
 Top-Bot about 3 yearsThank you!!!! 3 days of searching ODBC driver 17 SQL issues with server 2012 r2 led me here and you fixed it!!
Top-Bot about 3 yearsThank you!!!! 3 days of searching ODBC driver 17 SQL issues with server 2012 r2 led me here and you fixed it!! -
 Pardeep Poria over 2 yearsI think you need to restart the service like php-fpm.
Pardeep Poria over 2 yearsI think you need to restart the service like php-fpm. -
Brice about 2 yearsTwo remarks, one this also works for fedora, and likely other distributions. However
openssl version -dmay not return the system openssl binary, because it depends on thePATHand as such this command return a different install (and config).